Deze blogpost is gemaakt met het doel om te laten zien wat er .grovas ransomware virus en uitleggen hoe je dit ransomware van uw computer kunt verwijderen en hoe u bestanden kunt herstellen, versleuteld door deze infectie zonder dat het losgeld te betalen.
De .grovas ransomware virus, waarvan wordt aangenomen dat het een variant van STOP-ransomware is, is gemeld dat het computers infecteert in een enorme golf van spam-e-mails. De ransomware virus's primaire doel is om computers te infecteren, terwijl onontdekt blijven. De ransomware virus versleutelt vervolgens de bestanden op de computers die zijn geïnfecteerd door het zo dat het dan kan vallen is het losgeld notitiebestand, naam _open.txt die tot doel heeft om de slachtoffers te overtuigen in het betalen van losgeld om de bestanden weer aan het werk. Als uw computer is geïnfecteerd door .grovas, we aanraden dat je dit artikel leest want het zal je helpen om deze ransomware virus van uw computer effectief te verwijderen en laten zien hoe je kunt proberen en bestanden herstellen, versleuteld door deze ransomware.
| bedreiging Naam | .grovas Virus |
| Categorie | Ransomware / Cryptovirus. |
| Hoofdactiviteit | Infecteert de computer waarna versleutelt belangrijke documenten en houdt ze in gijzeling totdat er een losgeld wordt betaald. |
| Tekenen van Presence | Bestanden worden versleuteld met .grovas extensie en gebruikers worden afgeperst om losgeld te betalen om de gegevens weer aan het werk.. |
| Verspreiding | Via schadelijke e-mail spam en set van infectie gereedschappen. |
| Detection + Removal | DOWNLOAD Removal Tool VOOR .grovas Virus |
| Bestandherstel | Download Data Recovery Software, om te zien hoeveel bestanden versleuteld door .grovas Virus ransomware u in staat om te herstellen zal zijn. |
De .grovas Virus virus is gespot met behulp van de eigen bestandsextensie. De .grovas Virus virus communiceert ook via TOR waardoor het stuurt een decrypter nadat het losgeld is betaald. In het geval u een slachtoffer van de nieuwe .grovas Virus virus adviseren wij u om dit artikel te lezen en te leren hoe ze het virus bestanden te verwijderen en te proberen om gecodeerde objecten te decoderen.
.grovas Virus Virus - wat doet het
Omdat het een variant van de ransomware familie, die bestaat in veel virus families, de .grovas Virus ransomware is gemeld dat één of meer uitvoerbare bestanden te laten vallen in de %App data% Windows-map.
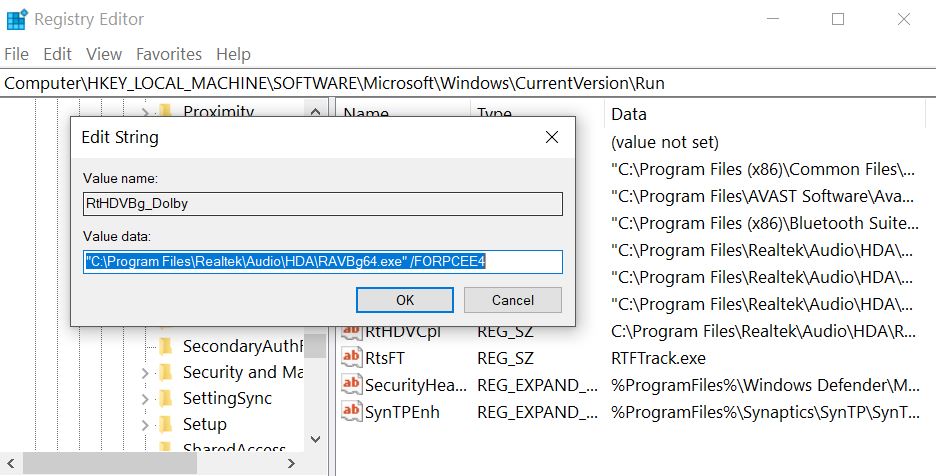
Na het doen dus, de .grovas Virus virus kan de Windows registry entries te wijzigen, meer specifiek de Shell subsleutel de volgende locatie:
- HKLM / Software / Microsoft / Windows NT / CurrentVersion / Winlogon / Shell
Vervolgens, de .grovas Virus virus kan ook wijzigen de Run registersleutel naar het uitvoerbare bestand uit te voeren(met) in de map% AppData% directory. De sleutel is met de volgende pad:
- HKLM / Software / Microsoft / Windows / CurrentVersion / Run /
Dit kan resulteren in het virus bestand opstarten naast de Windows start-up proces.
.grovas Virus daalt ook een losgeldnota bestand met een losgeld bericht en plaatst het ergens gemakkelijk te vinden. Vervolgens, de .grovas Virus virus kan bestanden aan te vallen met de volgende bestandstypen om ze te versleutelen:
- Videos.
- Afbeeldingen.
- documenten.
- Geluidsbestanden.
- Archief.
Na .grovas virus versleutelt bestanden, het virus laat de bestanden niet meer kunnen worden geopend en waarschijnlijk voegt een aangepast bestand Extenson om hen.
.grovas Virus Ransomware - How Did I Get Infected
Het infectieproces van .grovas Virus wordt uitgevoerd in de eerste plaats via gespamde e-mails die misleidende berichten ingebed in hen hebben. Dergelijke boodschappen kunnen doen alsof ze worden verzonden vanaf diensten zoals PayPal, UPS, FedEx en anderen. Zij kunnen bijlagen die doen alsof ze facturen en andere nep-type bestanden bevatten. Andere social engineering technieken omvatten:
- Fake knoppen en foto's alsof de e-mails worden verzonden vanaf een social media site, als LinkedIn.
- Frauduleuze PayPal koppelingen.
- Links naar Google Drive en nep e-mails die er hetzelfde uitzien alsof ze zijn verzonden vanaf Google.
Andere infectie gereedschap kan ook het gebruik van torrent websites en andere sites van derden bevatten om nep-updates te uploaden, fake installateurs alsmede andere frauduleuze executables.
Welke bestanden kunnen krijgen Beïnvloed door .grovas Virus Ransomware?
.grovas Virus Ransomware dient als een typisch bestand codeert Trojan. Zodra het toegang krijgt tot uw machine, dit cryptomalware zal een quick scan uit te voeren om de paden te vinden om al uw persoonlijke bestanden. De beoogde data omvat alle MS Office-documenten, uw kostbare foto's en video, uw databases, de programmabestanden, etc. Slechts een paar bestanden zoals die welke verband houden met de kern Windows-processen kunnen worden gespaard. Wanneer de bewerking eindigt, vindt u een bedreigende lockdown bericht krijgt op uw bureaublad en de standaard bestandsextensie ‘.dll’ te worden. De cybercriminelen geven de slachtoffers slechts enkele dagen te betalen het losgeld van Bitcoins, of anders dreigen ze voor altijd de decryptie sleutel te verwijderen. Het doel van deze angstaanjagende boodschap is om de persoon te schokken en maak hem irrationeel handelen. De slachtoffers voelen zich vaak als de enige oplossing voor het probleem is om het geld te betalen. In werkelijkheid, Alle specialisten bevelen unaniem aan de aanwijzingen van de hackers niet te volgen voor verschillende redenen.Hoe jezelf te beschermen tegen .grovas Virus Ransomware?
Dit ransomware kan enorm en vaak onherstelbare schade aan de getroffen machines veroorzaken. Gelukkig, kunt u de infectie, zolang je waakzaam zijn tijdens uw online sessies te voorkomen. Deze Trojan is niet bekend dat een aantal unieke methoden te gebruiken om de verdediging van uw computer te infiltreren. De meest waarschijnlijke oorzaak voor .grovas Virus Ransomware aan te gaan is via spam e-mails. U kunt een bericht met een schokkende inhoud, moedigen u aan ofwel klikken op een kwaadaardige link of het downloaden van een gecompromitteerde bestand. De hackers hebben een heel arsenaal van tools om u te manipuleren om te doen. Bij voorbeeld, kunnen zij aanspraak maken op een internationale bank of een populaire rederij vertegenwoordigen. Als ze pakken je zonder vermelding van uw naam, de e-mail is waarschijnlijk een scam en je moet negeren. Helaas, als je gewoon op of download de geïnfecteerde bestand, Uw actie zal waarschijnlijk genoeg zijn om de schadelijke codes van .grovas Virus Ransomware activeren. In dit geval, slechts een geloofwaardige beveiligingsoplossing in staat zijn om de komende schade te voorkomen.
Voorbereiding voor verwijdering van .grovas Virus:
1.Zorg ervoor dat u back-up van uw bestanden.
2.Zorg ervoor dat u deze pagina instructies altijd open, zodat u de stappen kunt volgen.
3.Wees geduldig als de verwijdering enige tijd duren.
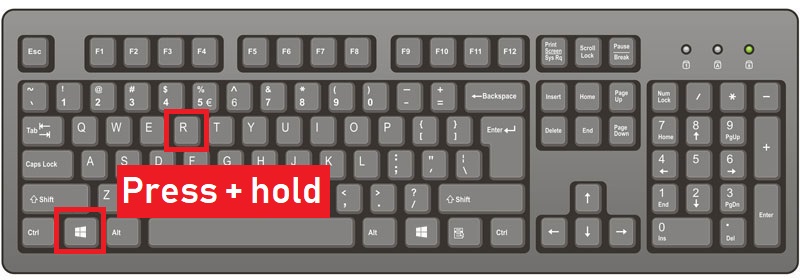
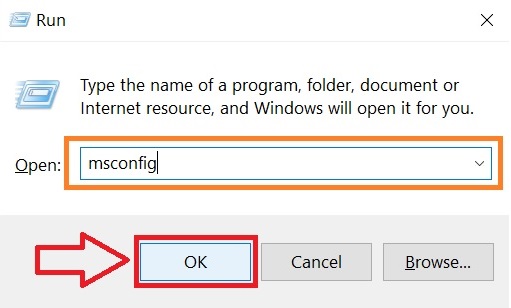
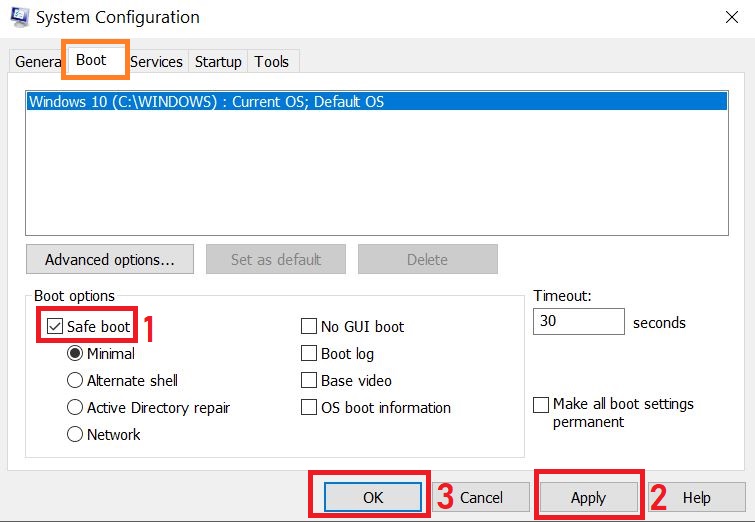
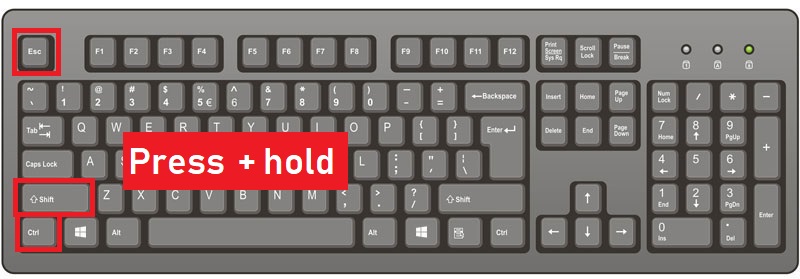
Stap 1: Start de computer opnieuw in de veilige modus:
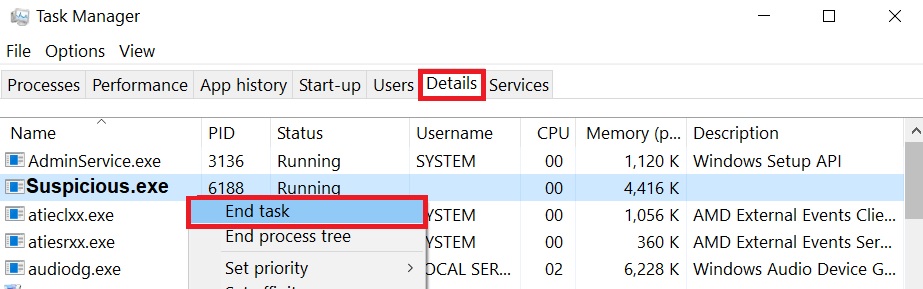
Stap 2: Knip .grovas Virus in Taakbeheer
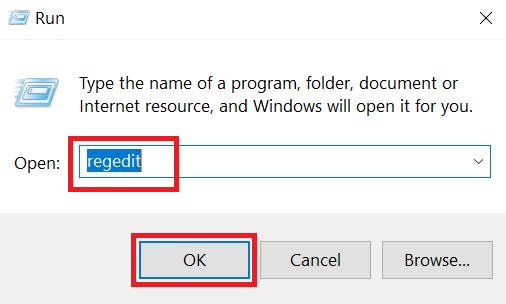
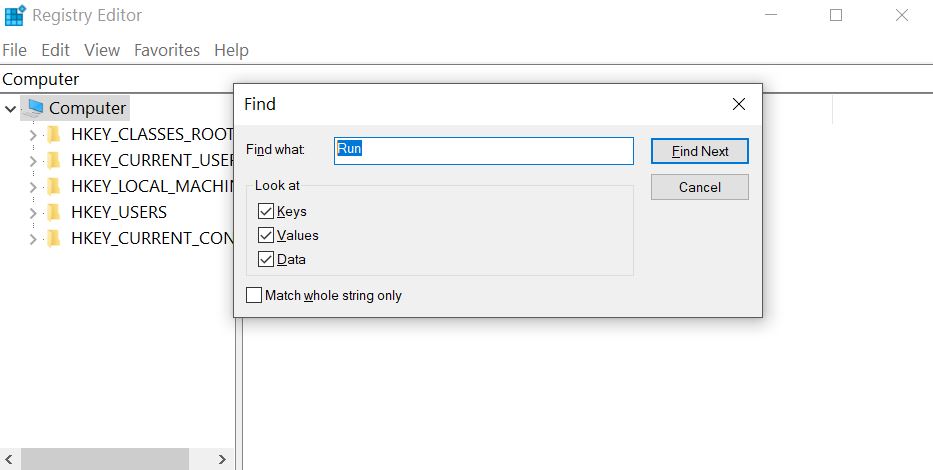
Stap 3: Elimineer Schadelijke Registries .grovas Virus.
Voor de meeste Windows-varianten:
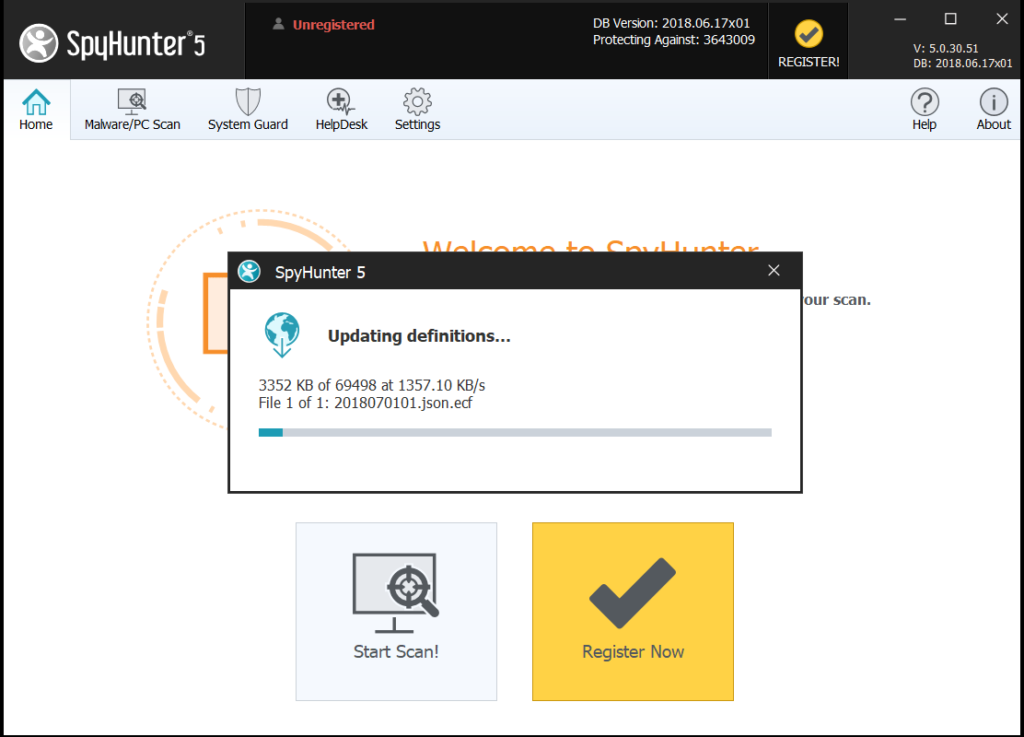
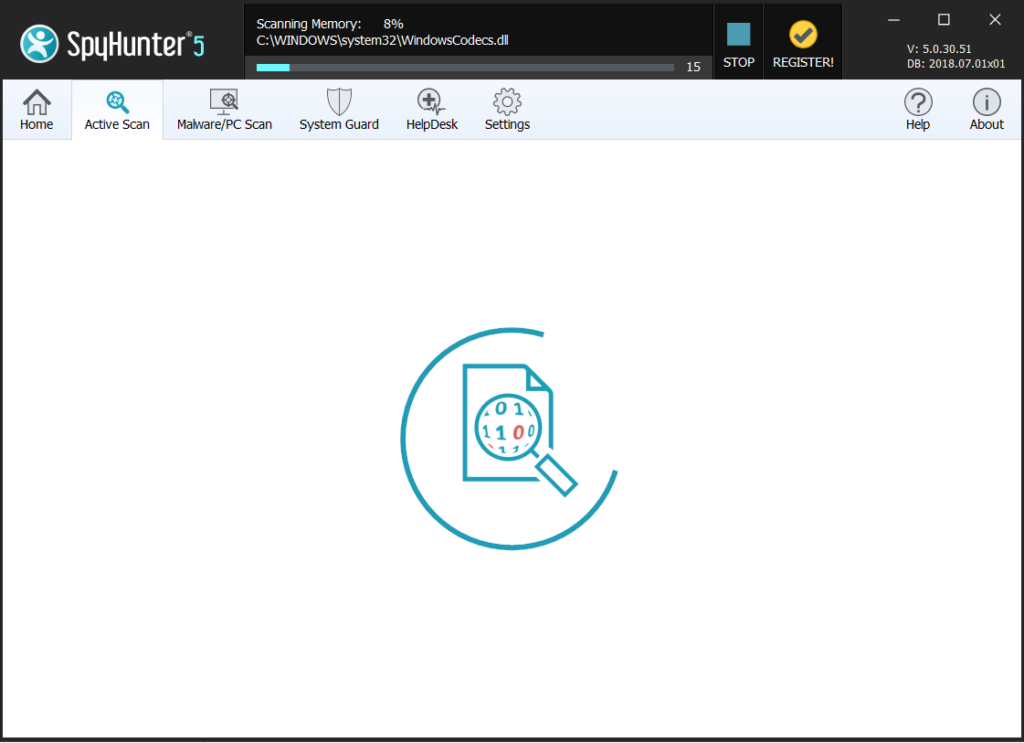
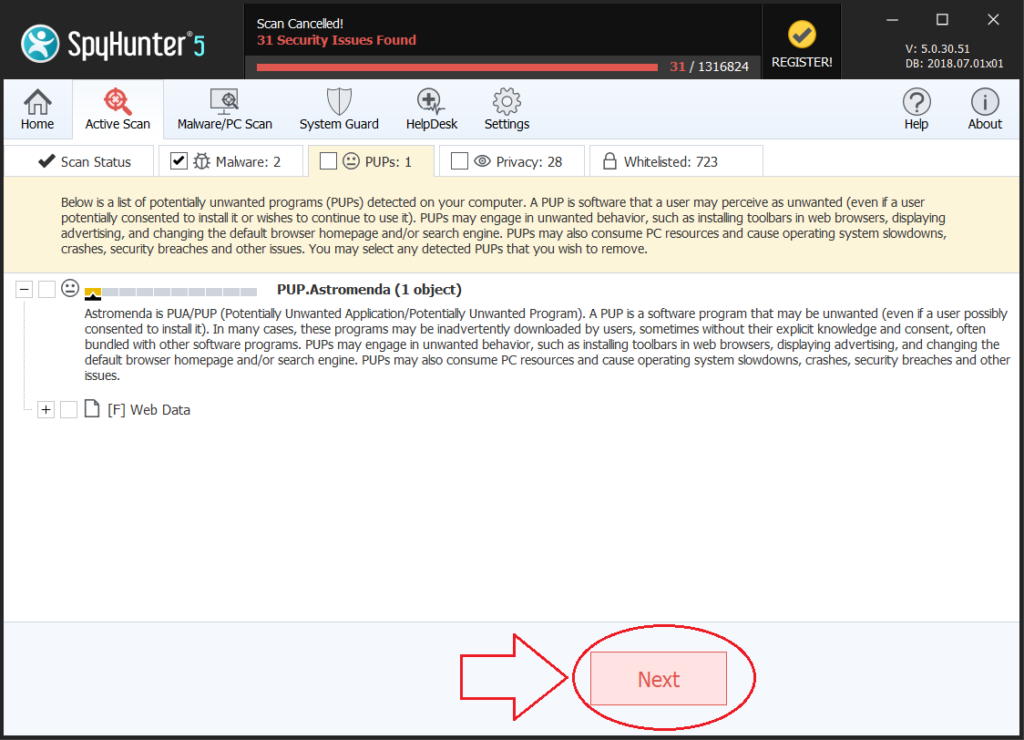
Stap 4: Scan op en verwijder alle virusbestanden, in verband met Virus .grovas en het systeem te beveiligen.
Als u in Veilige modus, laars terug in de normale modus en volg de onderstaande stappen
Het is raadzaam om een gratis scan uit te voeren voor het plegen van de volledige versie. Je moet ervoor zorgen dat de malware voor het eerst wordt gedetecteerd door SpyHunter.
Stap 5:Recover bestanden versleuteld door de .grovas Virus Ransomware.
Methode 1: Met behulp van Shadow Explorer. In het geval dat je de geschiedenis File ingeschakeld op uw Windows machine een ding dat je kunt doen is Shadow Explorer gebruiken om uw bestanden terug te krijgen. Helaas zijn sommige ransomware virussen kunnen die schaduw volume kopieën te verwijderen met een administratieve commando om te voorkomen dat u precies dat te doen.
Methode 2: Als je probeert om je bestanden te decoderen met behulp van derden decryptie gereedschap. Er zijn veel antivirus aanbieders die meerdere ransomware hebben ontcijferd virussen de afgelopen paar jaar en gepost decryptors voor hen. De kans is groot als je ransomware virus maakt gebruik van dezelfde encryptie code gebruikt door een decryptable virus, kunt u de bestanden terug te krijgen. Echter, dit is ook geen garantie, dus je zou willen proberen deze methode met kopieën van de originele gecodeerde bestanden, want als er een programma van derden knoeit met hun gecodeerde structuur, ze kan er door beschadigen. De meeste van de momenteel beschikbare decryptors voor ransomware virussen kan worden gezien als u het NoMoreRansom project te bezoeken – een project dat is het resultaat van gezamenlijke inspanningen van de onderzoekers over de hele wereld om decryptie software te maken voor alle ransomware virussen. Gewoon gaan er door te klikken op de volgende KOPPELING en vind uw ransomware versie decrypter en probeer het, maar altijd onthouden om eerst een backup te doen.
Methode 3: Met behulp van data recovery tools. Deze methode wordt voorgesteld door meerdere deskundigen in het veld. Het kan gebruikt worden om de sectoren van uw harde schijf scannen en dus klauteren de versleutelde bestanden opnieuw alsof ze zijn verwijderd. De meeste ransomware virussen meestal een bestand te verwijderen en een versleutelde kopie aan dergelijke programma's te voorkomen voor het herstellen van de bestanden te maken, maar niet alle zijn deze verfijnde. Dus je kan een kans op herstel van sommige van uw bestanden met deze methode hebben. Hier zijn verschillende data recovery programma's die je kunt proberen en herstellen van ten minste enkele van uw bestanden: