Cerber Ransomware a été récemment renaissant. Il est maintenant fait rage autour de sous le nom de Cerber2 - sa nouvelle version améliorée. Le nouveau nom, cependant, est pas la seule différence entre l'ancien et les nouvelles variantes. Lisez la suite pour savoir comment Cerber2 agit maintenant et comment vous pouvez le supprimer et restaurer vos fichiers.
Cerber2 Ransomware - Comment t-il dans votre ordinateur?
La méthode de livraison de Cerber2 est pas différent de la plupart des virus de ransomware, y compris son prédécesseur. Il se propage principalement via des e-mails de spam contenant un fichier exécutable avec l'icône « Anka » (un personnage de jeu vidéo), et une fois que vous ouvrez le fichier, Cerber2 téléchargements à votre système et l'infection commence. D'autres moyens de livraison, cependant, sont également possibles, à savoir. via les réseaux sociaux, services de partage de fichiers, exploiter kits, etc.
Pour inciter les utilisateurs à ouvrir un e-mail compromis, cyber-escrocs utilisent généralement familier pour les noms de l'expéditeur de l'utilisateur, tels que les factures des banques, sites Web populaires, etc. Nous conseillons à tous les utilisateurs d'être vigilants lors de la vérification supplémentaire et leurs boîtes de réception lors de la réception des fichiers provenant d'expéditeurs suspects. Si vous avez le moindre doute sur l'e-mail / fichier que vous êtes sur le point d'ouvrir, ne pas le faire, comme ransomware entrera votre système avec un clin d'œil et il brouille vos fichiers importants pour une bonne.
Cerber2 Ransomware - Que faut-il faire?
Une fois que vous avez cliqué sur un fichier corrompu contenant Cerber2, il entre dans votre système et s'active comme son prédécesseur. Il analyse ensuite l'ensemble de votre système pour rechercher des fichiers avec les extensions suivantes pour les chiffrer:
1CD, .3dm, .3ds, .3fr, .3g2, .3gp, .3par, .7de, .7fermeture éclair, .aac, .AB4, .abd, .acc, .accdb, .accde, .accdr, .accdt, .mais, .acr, .acte, .adb, .adp, .les publicités, .AGDL, .à, .aiff, .appartenant à, .Al, .aoi, .APJ, .apk, .arw, .ascx, .asf, .personne, .aspic, .ASPX, .atout, .asx, .atb, .avi, .awg, .retour, .sauvegarde, .backupdb, .derrière, .banque, .baie, .bdB, .BGT, .Bik, .poubelle, .PKP, .mélange, .bmp, .BPW, .bsa, .c, .en espèces, .cdb, .cdf, .cdr, .CDR3, .CDR4, .cdr5, .CDR6, .CDRW, .CDX, .ce1, .ce2, .ciel, .cfg, .CFN, .cgm, .poche, .classe, .cls, .cmt, .config, .contact, .cpi, .cpp, .CR2, .jabot, .crt, .CRW, .pleurer, .cs, .csh, .csl, .css, .csv, .d3dbsp, .Dacian, .la, .qui, .db, .db_journal, .db3, .dbf, .DBX, .DC2, .DCR, .dcs, .ddd, .quai, .NRW, .dds, .def, .la, .des, .conception, .DGC, .avec, .cette, .djvu, .DNG, .doc, .docm, .docx, .point, .DOTM, .dotx, .DRF, .DRW, .dtd, .DWG, .DXB, .dxf, .DXG, .ordinateur, .EML, .eps, .erbsql, .propriété, .EXF, .FDB, .ffd, .fff, .fh, .FHD, .Floride, .flac, .FLB, .FLF, .flv, .flvv, .forger, .fpx, .FXG, .gbr, .gho, .gif, .gris, .gris, .groupes, .jeu, .h, .HBK, .hdd, .HPP, .html, .iBank, .IBD, .FLR, .IDX, .ssi, .IIQ, .incpas, .indd, .Info, .Info_, .cette, .iwi, .pot, .Java, .JNT, .jpe, .jpeg, .jpg, .js, .JSON, .K2P, .kc2, .kdbx, .kdc, .clé, .KPDX, .histoire, .laccdb, .lbf, .LCK, .LDF, .Lit, .litemod, .litesql, .fermer à clé, .bûche, .LTX, .prendre, .m, .M2TS, .m3u, .m4a, .M4P, .m4v, .mère, .mab, .MAPIMAIL, .max, .MBX, .Maryland, .CIS, .mdc, .MDF, .MEF, .mfw, .milieu, .mkv, .mlb, .MMW, .MNY, .argent, .MoneyWell, .mos, .mov, .mp3, .mp4, .mpeg, .mpg, .mrw, .mpc, .msg, .monde, .Dakota du Nord, .ndd, .ndf, .nef, .NK2, .nop, .nrw, .NS2, .NS3, .NS4, .NSD, .nsf, .NSG, .NSH, .NVRAM, .nwb, .NX2, .nxl, .NYF, .OAB, .obj, .spec, .Épisode, .odf, .réponse, .odm, .Répondre, .ods, .odt, .ogg, .pétrole, .OMG, .un, .orf, .ost, .OTG, .OTH, .Bureau du Procureur, .OTS, .là, .p12, .p7b, .P7C, .aider, .pages, .pas, .tapoter, .PBF, .pcd, .pct, .pdb, .pdd, .pdf, .pef, .PEM, .pfx, .php, .pif, .PL, .plc, .plus_muhd, .h!, .h, .pmi, .PMJ, .LEMP, .PMM, .CPM, .PMR, .pnc, .DPN, ..png, .PNX, .pot, .potm, .potx, .ppam, .pps, .PPSM, .ppsx,.ppt, .GRP, .pptx, .prf, .privé, .ps, .psafe3, .psd, .pspimage, .tvp, .ptx, .pub, .MLI, .py, .qba, .QBB, .QBM, .QBR, .QBW, .QBX, .QBY, .qcow, .qcow2, .sont, .QTB, .R3D, .raf, .rar, .rat, .brut, .RDB, .RE4, .rm, .rtf, .RVT, .rw2, .rwl, .RWZ, .S3DB, .coffre-fort, .sas7bdat, .sav, .enregistrer, .dire, .sd0, .sda, .salésien, .sdf, .sh, .SLDM, .sldx, .slm, .sql, .sqlite, .sqlite3, .sqlitedb, .sqlite-SHM, .sqlite-wal, .SR2, .SRB, .SRF, .srs, .srt, .SRW, .ST4, .ST5, .ST6, .ST7, .ST8, .stc, .std, .sti, .taille, .stm, .STW, .stx, .svg, .swf, .sxc, .SXD, .sxg, .elle, .sxm, .sxw, .impôt, .TBB, .tbk, .TBN, .Texas, .tga, .thm, .TIF, .querelle, .pcs, .tlx, .SMS, .Upk, .usr, .Vbox, .vdi, .VHD, .VHDX, .VMDK, .vmsd, .VMX, .vmxf, .vob, .VPD, .vsd, .WAB, .liasse, .portefeuille, .guerre, .wav, .WB2, .wma, .WMF, .wmv, .WPD, .WPS, .x11, .x3f, .film, .XLA, .xlam, .xlk, .XLM, .xlr, .xls, .xlsb, .xlsm, .xlsx, .XLT, .xltm, .xltx, ..xlw, .xml, .xps, .xxx, .ycbcra, .yuv, .fermeture éclair
Cerber2 est capable de chiffrer plus 450 types de fichier. Vous savez que vos fichiers ont été verrouillés par Cerbe2 quand ils reçoivent une extension .cerber2 à la fin et les noms de fichiers sont remplacés par ce qui contient dix caractères aléatoires.
Après le cryptage des fichiers, Cerber2 va scanner pour certains processus, et si elles sont actives, il les arrête:
- excel.exe
- infopath.exe
- msaccess.exe
- mspub.exe
- OneNote.exe
- outlook.exe
- powerpnt.exe
- steam.exe
- Sqlservr.exe
- thebat.exe
- thebat64.exe
- thunderbird.exe
- visio.exe
- winword.exe
- wordpad.exe
Comme mentionné précédemment, le nom de cette variante ransomware et les extensions ses fichiers cryptés reçoivent, ne sont pas la seule différence entre les virus et ransomware Cerber Cerber2. L'amélioration la plus importante de la nouvelle est qu'il n'utilise plus Cypher AES-256 comme technique de cryptage principale. Plutôt, il utilise CryptGenRansom de Microsoft.
Cerber2 dispose également d'une liste des programmes anti-malware qu'il est à l'abri. Ces programmes sont:
- Arcbit
- ArcaVir
- avast
- BitDefender
- BullGuard
- EMSISOFT
- ESET
- eTrust
- F-Secure
- G Data
- Kaspersky Lab
- LavaSoft
- TrustPort
Un compteur à rebours d'une « promotion » de cinq jours commencera alors. Le compteur affiche la date limite de la victime doit payer le montant de 0.3 bitcoins (ou 175 Dollars américains). Si la victime ne fait pas la transaction dans 5 journées, le montant double.
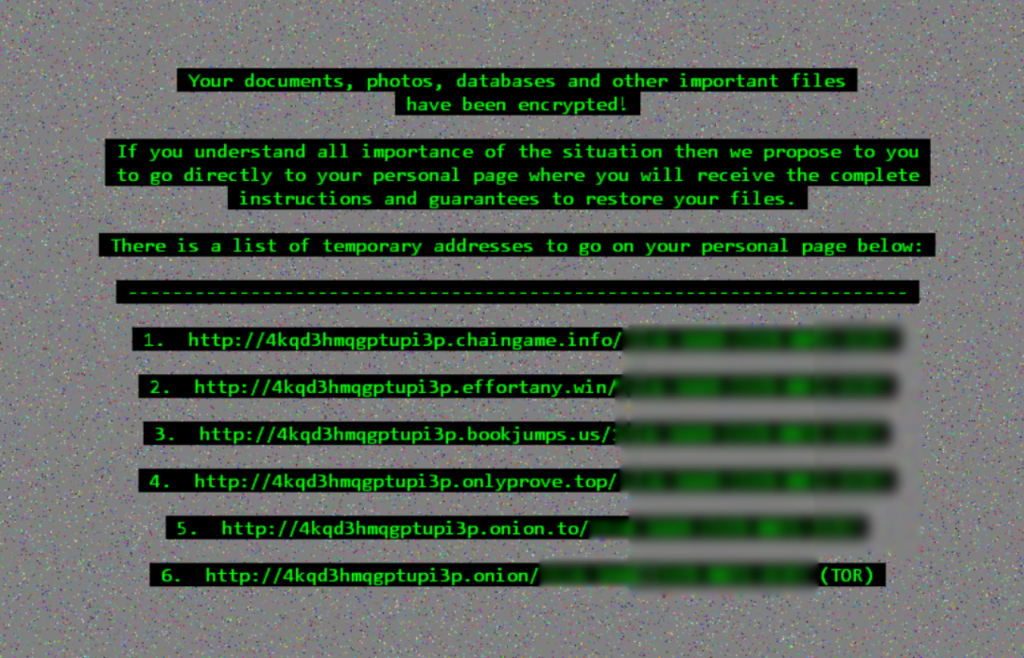
Le message de rançon ressemble à ceci:
…et il se lit comme celui-ci:
vos documents, Photos, bases de données, et d'autres fichiers importants ont été chiffrés!
Si vous comprenez toute l'importance de la situation alors que nous vous proposons d'aller directement à votre page personnelle, où vous recevrez les instructions et garanties complètes pour restaurer vos fichiers.
Cerber2 Ransomware - Suppression manuelle
Bien que cela puisse paraître tentant de simplement payer la rançon et obtenir une clé de décryptage pour vos fichiers, nous vous conseillons vivement de ne pas le faire. Payer les cyber-criminels ne vous garantit pas une clé de déchiffrement, ni elle assure la suppression de Cerber2. Le virus restera simplement dans votre système et peu importe si vous avez vos fichiers, il peut frapper à nouveau.
Payer les cyber-escrocs ne les encourage à propager l'infection. Au lieu, nous vous suggérons d'utiliser un outil anti-malware puissant qui va scanner votre système, détecter le virus et le supprimer définitivement de votre système. Une fois Cerber2 ransomware est complètement supprimé de votre PC, vous pouvez essayer de récupérer certains d'entre vous des fichiers via des outils de récupération de fichiers.