 Neue Version der berüchtigten Locky Ransomware ist erschienen, Anhängen der .thor Dateierweiterung. Die Variante tauchte sofort nach einer anderen Variante heraus, dass die .shit Dateierweiterung verwendet, um mit Infektionen in verschiedenen Ländern auf der ganzen Welt explodierte. Die .thor Version von Locky ist sehr gefährlich und wenn nachgewiesen, Beratung ist es mit einem Anti-Malware-Programm auf den ersten Blick zu entfernen und nicht das Lösegeld zahlen angefordert von 0.5 BTC.
Neue Version der berüchtigten Locky Ransomware ist erschienen, Anhängen der .thor Dateierweiterung. Die Variante tauchte sofort nach einer anderen Variante heraus, dass die .shit Dateierweiterung verwendet, um mit Infektionen in verschiedenen Ländern auf der ganzen Welt explodierte. Die .thor Version von Locky ist sehr gefährlich und wenn nachgewiesen, Beratung ist es mit einem Anti-Malware-Programm auf den ersten Blick zu entfernen und nicht das Lösegeld zahlen angefordert von 0.5 BTC.
Herunterladen Malware Removal Tool, Wenn Ihr System zu sehen ist von Locky Ransomware Virus und Scannen Sie Ihr System für .SHIT Virus Dateien betroffen
Locky .thor Variant - Was bedeutet es tun (methodische Beschreibung)
Die erste Stufe des Ransomware-Virus ist es weit verbreitet zu sein. Damit dies erreicht werden, die Schöpfer des Virus haben eine ziemlich heimtückische aber erwartete Liefermethode. Sie nutzen Spam-E-Mail-Nachrichten mit unterschiedlichen contant, die unerfahrenen Anwender dazu verleiten wollen eine archivierte Datei mit dem Namen öffnen, ähnlich der folgenden:
Nachdem die archivierten Datei geöffnet wurde, kann es eine Datei enthalten, die eine der folgenden Dateitypen
Sobald öffnet der Benutzer diese Datei, die Infektion Prozess hat begonnen. Die Infektion Datei verbindet remote zu einem einem von Hunderten von Hosts die Nutzlast der .thor Variante Locky Ransomware zum Download.
Sobald die Nutzlast-Datei heruntergeladen wurde, der Ransomware-Virus wird sofort aktiv von Anfang Windows-Einstellungen zu ändern.
Zunächst verbindet es mit den Kommando- und Kontrollserver angewiesen Informationen zu beginnen zu leben, ob nicht die Infektion erfolgreich ist und was der böswillige Benutzer will mit dem infizierten Computer durchgeführt werden. Die Kommandozentralen von Locky bisher berichtet worden hinter den folgenden Bereichen verstecken:
fvhnnhggmck.ru/linuxsucks.php
krtwpukq.su/linuxsucks.php
tdlqkewyjwakpru.ru/linuxsucks.php
185.102.136.77:80/linuxsucks.php
91.200.14.124:80/linuxsucks.php
91.226.92.225:80/linuxsucks.php
77.123.14.137:221/linuxsucks.php
Unter den gelöschten Dateien von Locky Ransowmare ist die DLL-Datei, die für die Verschlüsselung von Dateien verantwortlich ist. Das Virus kann sofort ausführen, die Datei, etwas, das auch als Drive-by-Download bekannt sein kann,. Jedoch, die .thor Variante Locky können auch die Datei in% Startup% Verzeichnis löschen oder die Run und RunOnce Registrierungsschlüssel ändern, so dass der Verschlüssler auf Windows-Start ausgeführt wird.
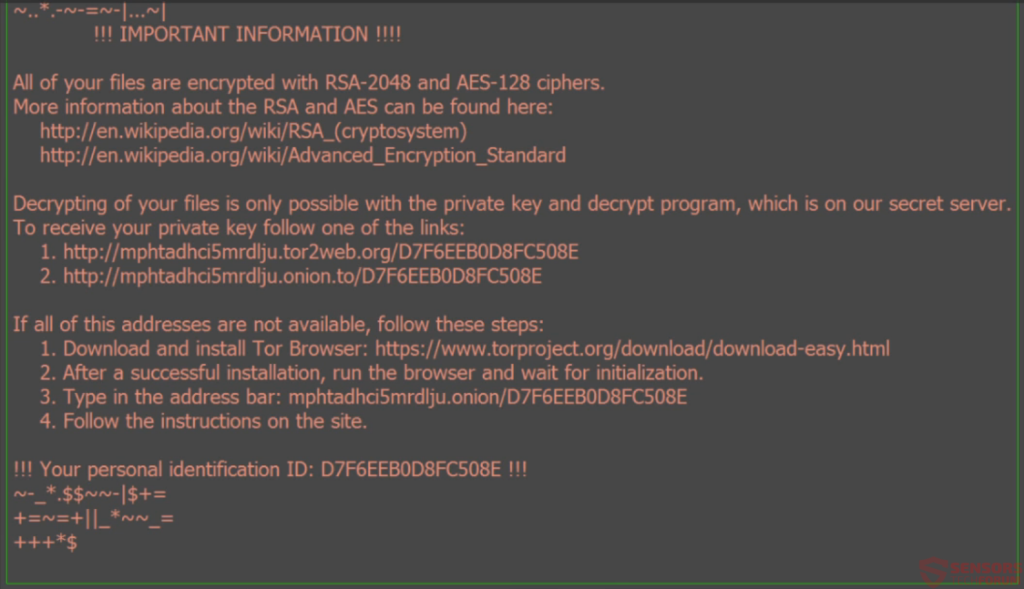
Nach der Verschlüsselung wurde lief, genau wie die .Scheiß Dateierweiterung Variante Locky, Diese Variante kann auch verheerend auf Ihrem Computer anrichten. Es fällt sofort seine einzigartige Erpresserbriefe, das ist eine Tapete und eine _WHAT_is.html Datei.
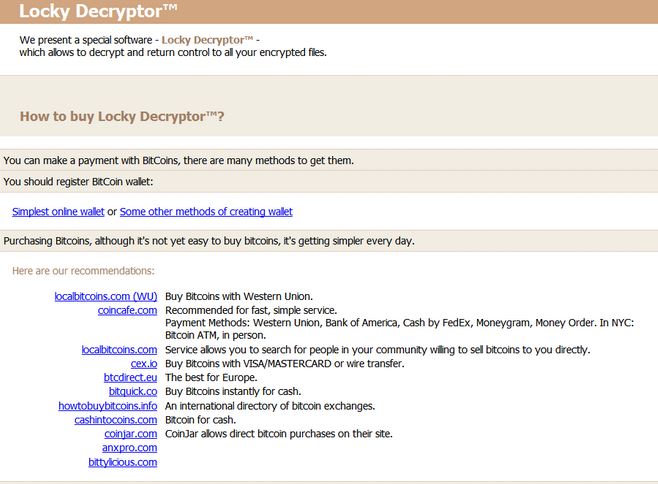
Der Hinweis auf beiden führt zu einer eindeutigen URL zu Locky Ransomware gehört, die weiteren Anweisungen hat, wie eine BitCoin Brieftasche zu schaffen und das Lösegeld auf diese Weise bezahlen.
Nach der Verschlüsselung wurde getan,, die .thor Variante Locky stellt sicher, dass die ursprünglichen Versionen der Dateien sind für immer verschwunden, Kopien der verschlüsselten Dateien und „läuft über“ die Originaldateien über mehrere Pässe zum Löschen Erstellen. Es löscht auch Schatten Volume-Kopien, nur für den Fall gibt es einige mit dem folgenden Befehl über Windows-Eingabeaufforderung injizierte.
Wie entferne ich Locky Ransomware und Entschlüsseln von Dateien .thor?
Leider ist für alle der Locky Varianten, es wurde nicht eine einzige Datei Entschlüsselung entdeckt. Du kannst, jedoch mehrere andere Aufgaben, wie Versuch, den Entschlüsselungsschlüssel zu finden, um die Verschlüsselung von Locky entsprechen, die Ihre Dateien, um sie verschlüsselt und gemacht wie folgt aussehen:
Ein Verfahren, dies zu tun ist, über ein Netzwerk Sniffing-Software, aber Sie den Moment fangen müssen, wenn die Malware-Informationen über HTTP senden, UDP oder TCP an den böswilligen C2-Server.
Eine weitere Möglichkeit, den Schlüssel zu bekommen ist durch das Lösegeld zu zahlen, die nicht zu empfehlen. Stattdessen können Sie versuchen, Daten-Recovery-Software zu verwenden und versuchen, einige Ihrer Dateien wiederherzustellen, indem das Scannen der Sektoren der Festplatte.
Herunterladen Malware Removal Tool, Wenn Ihr System zu sehen ist von Locky Ransomware Virus und Scannen Sie Ihr System für .SHIT Virus Dateien betroffen