We are all using antivirus programs in order to protect our devices and the data they have. However, are these antivirus products protected? Which are the antivirus products that are best at securing their own protection? After all the security software is also subject to flaws. The German laboratory AV-Test Institute has recently presented a report showing how the vendors of security products are actually protecting them.
What was found?
According to the test report from AV-Test Institute, the best antivirus programs have one error on every 2000 code lines. However, one main program contains millions of code lines, which means plenty of errors. Naturally, not every error makes the antivirus program vulnerable to malware, yet some errors can do that.
For the attack to succeed, the victim’s program should execute the malicious code. I some cases the cybercriminals slip the code in masking it as data, making the victim to run it. In other cases the cybercriminals manipulate the stack and the memory areas that are used by the programs as temporary storage zones. In yet other situations, they jam more data in the buffer zone than the memory allows and in this way they get an arbitrary code into the memory space of the program.
Mature Technologies
Users can apply two mature technologies that can prevent the malware from getting into the antivirus program. The first one is the Data Execution Protection, which can prevent the code execution in the memory area marked as holding data. The second one is the Address Space Layout Randomization, which shuffles all the memory sectors that are used by the program. In this way it is impossible for the cybercriminal to find out the sector which has the vulnerable code.
These two mature technologies are used by Windows and their implementation is very easy.
Methodology Testing
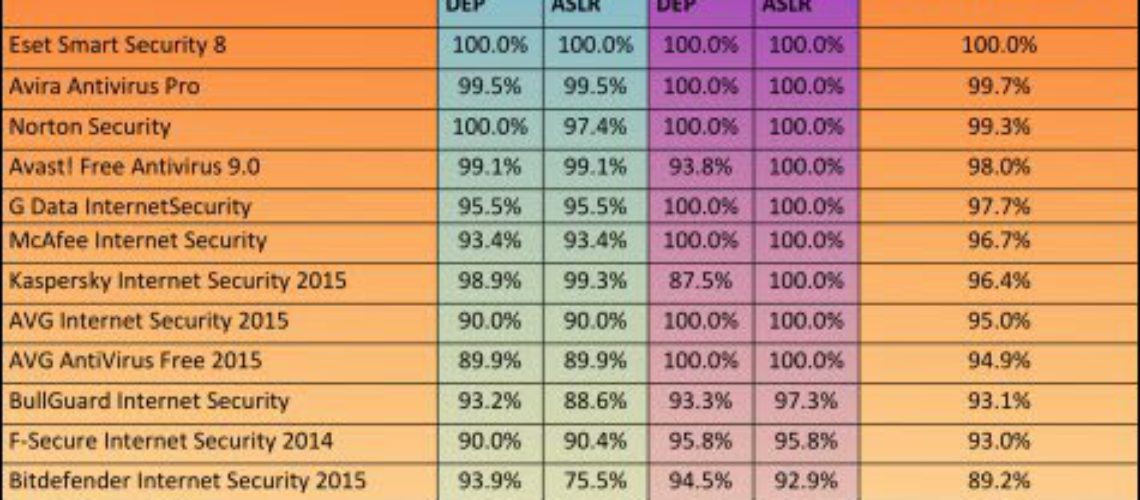
The researchers from the AV-Test Institute made a test based on 8 business oriented products and 24 consumer oriented security products. For each of the products they have enumerated the executable file, the driver, the .sys file, the dynamic link library. Then they noted if each of the modules implemented Data Execution Protection, Address Space Layout Randomization, or both of these technologies. The researchers also evaluated the 32-bit products and the 64-bit products separately.
The Results
The testing results were of a wide range:
- The only consumer product that showed 100 % coverage was ESET, with Symantec being the only business product of the same level.
- McAfee, Avira, G Data and AVG offered full protection on their 64-bit products using ASLR and DEP. At the same time their 32-bit products showed 90 to 100 % protection.
- eScan Internet Security Suite offered only 17.5 % protection.
- Kingsoft Antivirus provided 19 % protection, but did not apply DEP on all its 64-bit products.
The researchers confirm that in order for the protective mechanisms to be enabled, the user has to switch on the complier. So, a question comes – why did the vendors ignore the protection? It turned out that some of the vendors are using third-party libraries which are not complied with security on. Others use proprietary security technology that is not compatible with ASLR and DEP.
Antivirus Protection
Together with the report for self-protection, the AV-Test Institute released the last report concerning, performance and also usability. According to the report, Kaspersky showed top results of 18 points, no change from the last report. At the same time Avira got a 1.5 point increase from the last report. Down the table are ZoneAlarm and Vipre with 2.5 points and 8.5 points. The points required for certification are 10.
Checking the security products for their self-protection was important, as the security vendors had to understand that they cannot operate without DEP and ASLR.