What are Tisc files? What is the Tisc virus? How to remove Tisc virus ransomware from your computer? How to try and restore Tisc virus encrypted files?
Tisc virus is a ransomware infection that makes the files of the innocent victim PC unreadable via encrypting them. This cryptomalware appends Tisc virus extension or similar to all files that it manages to compromise. Once the complex process of changing the core structure of your data ends, you may lose access to everything valuable to you like your photos, documents, notes, videos, etc. Just like all ransomware Trojans, Tisc virus will keep them encrypted until the victim feels he has no other choice but to pay the ransom by buying and transferring the anonymous cryptocurrency BitCoin. This decision is not supported by the cyber security expers for several different reasons, which will be explained later in this article. Read this material to learn how you can remove Tisc virus and how to try and restore compromised files by it.
| Threat Name | Tisc virus |
| Category | Ransomware/Cryptovirus. |
| Main Activity | Infects the computer after which encrypts important documents and holds them hostage until a ransom is paid. |
| Signs of Presence | Files are encrypted with a custom file extension and users are extorted to pay ransom to get the data to work again.. |
| Spread | Via malicious e-mail spam and set of infection tools. |
| Detection+Removal | DOWNLOAD REMOVAL TOOL FOR
Note!For Mac users, please use the following instructions. |
How Does the Infection with Begin?
The developers of this ransomware try to deploy it to the computers of the victims via a variety of clever tactics. The hackers most commonly rely on spam email campaigns to reach the unsuspecting PC users. With only a few clicks, the cyber criminals may send the infection of Tisc virus towards hundreds or even thousands of users at once. This process also involves very little operational costs and a high success rate, which explains why it is so preferred. While the spam emails is a single tactic, it can come in very different forms. The hackers may try to look as if the malicious message was coming from banks, financial platforms like PayPal, shipping companies like DHL or famous email providers. Usually, the content of the letters mentions some unauthorized transactions or other information that may worry the recipient. The end goal is for you to download and open the file attached to those e-mails.
The email itself contains very little information, and the supplementary data is supposed to appear in the attached file. If you make the mistake to download or open it, you may infect your machine with Tisc virus. The problem may also happen if you install programs like Adobe or Java from random suspicious platforms like the majority of adult and other software download sites.
What May Follow If Ransomware Finds a Way into Your System?
If Tisc virus sneaks in, it will not reveal its presence immediately. It will first perform an encryption of all partitions of your hard disk. Depending on the amount of files you have there, the process may take between 15-20 mins and a few hours. Tisc virus uses a ‘strong’ encryption, which would be either RSA or AES. These ciphers are indeed difficult to break without the corresponding key. Unfortunately, this tool cannot be extracted from your system because it is simply not there. As soon as the encryption ends, Tisc virus automatically transfers the key towards distant hosts, which serve as Command and Control (C&C) servers. As of now, there is no data that some security researcher has managed to breach into these databases, but it may happen in the future. Tisc virus encourages the user to pay a ransom in the form of Bitcoins, which varies from hundreds to thousands of dollars worth. The person has limited time to act – only several hours, which is a scare mechanism. The key is supposed to get destroyed when the timer reaches zero.
What to and Not to Do After You Lose Your Files Due to Tisc Ransomware?
The first and most important thing to remember is not to succumb to the pressure. No matter how the hackers threaten you, you should not pay the ransom. It is true that the sum is not that high in comparison to other file-encoding Trojans, but even if the hackers receive your money, they may not release the precious key. Or if they do, you should expect them to continue creating and spreading more ransomware, which means you may get infected by a similar cyber threat anytime in the future. The right action is to delete Tisc virus immediately. Since this parasite compromises various areas of the system, it will be best to eliminate it via special security software. When the removal is completed, you can use some free decryptor that may manage to break the ciphers. Another possibility is to use a data restoring tool, which may revert your PC to an earlier date. If you have a recent copy of your hard drives, you can safely import all of your files back to your device.
To REMOVE and TRY TO RESTORE files, please follow the instructions underneath
Preparation before removal of :
1.Make sure to backup your files.
2.Make sure to have this instructions page always open so that you can follow the steps.
3.Be patient as the removal may take some time.
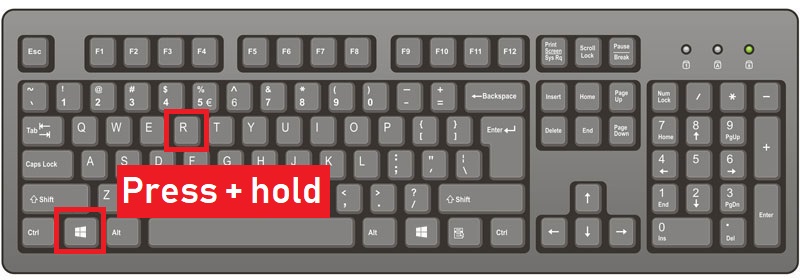
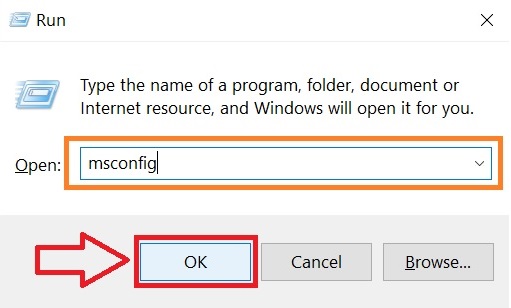
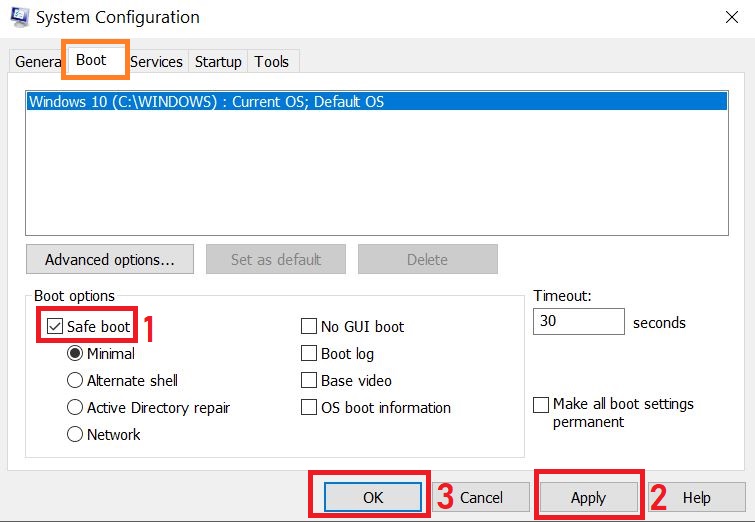
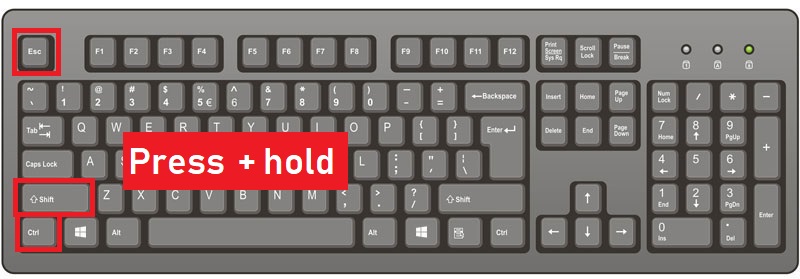
Step 1: Reboot your computer in Safe Mode:
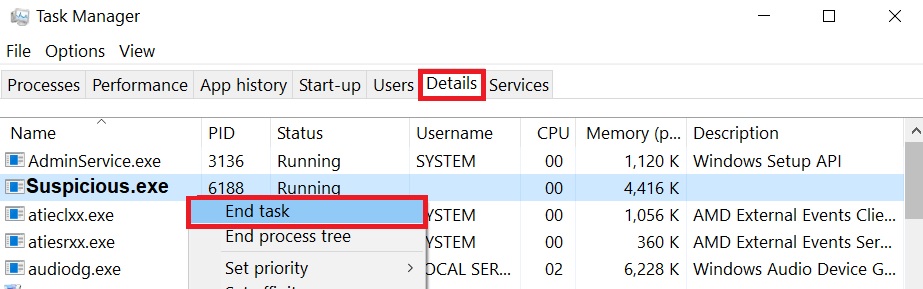
Step 2: Cut out in Task Manager
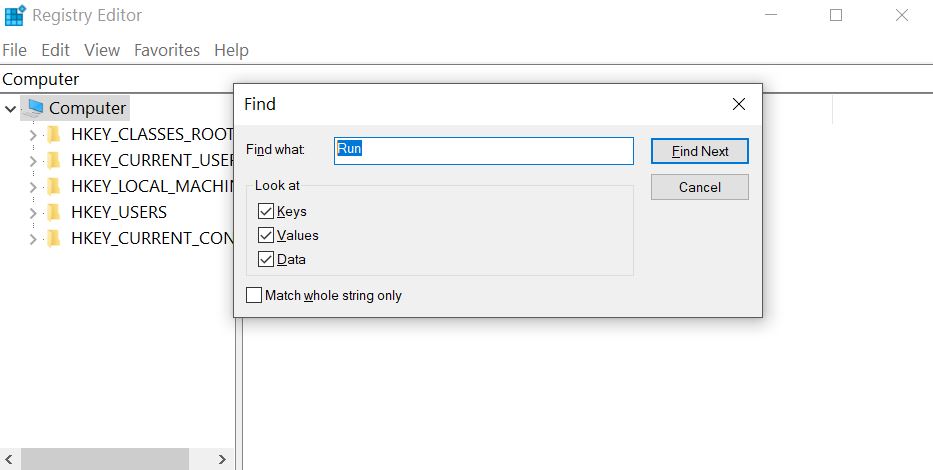
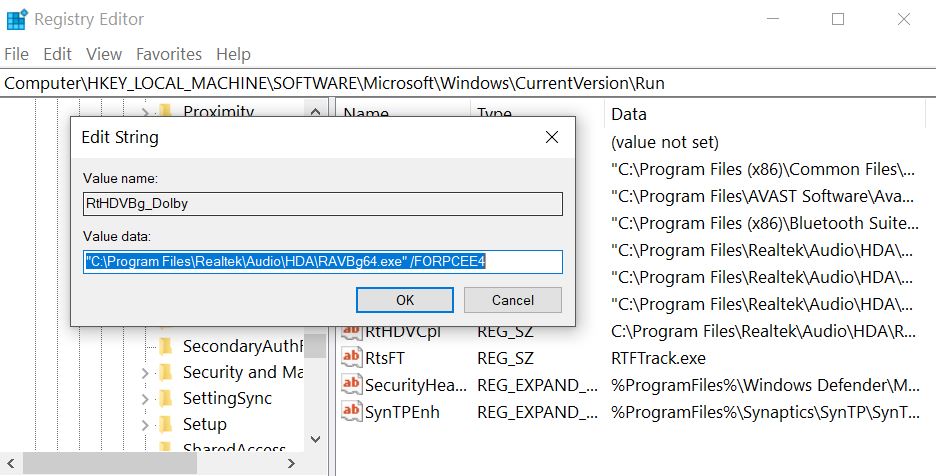
Step 3: Eliminate ‘s Malicious Registries.
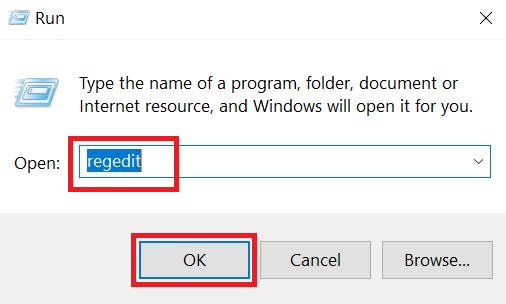
For most Windows variants:
Step 4: Scan for and remove all virus files, related to and secure your system.
If you are in Safe Mode, boot back into normal mode and follow the steps below
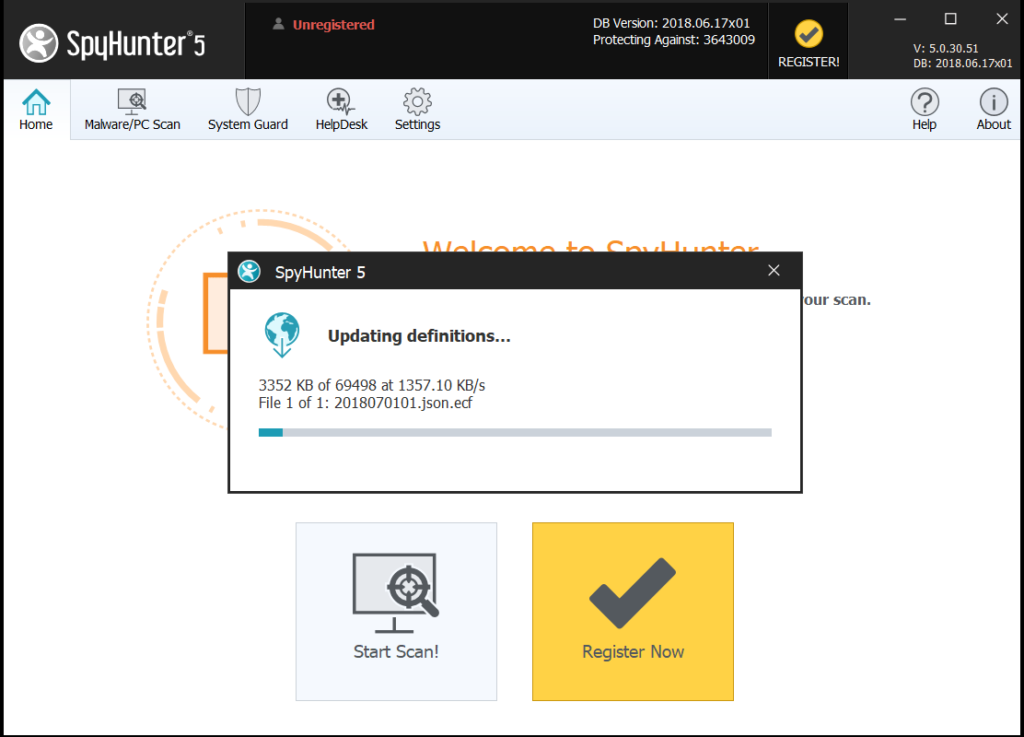
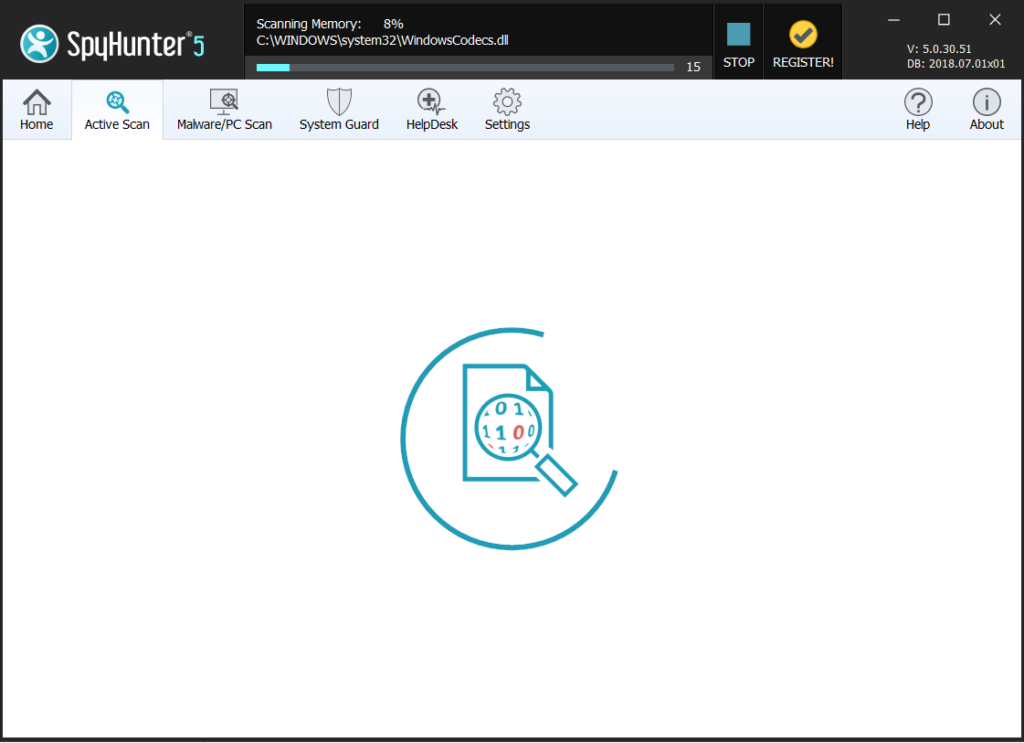
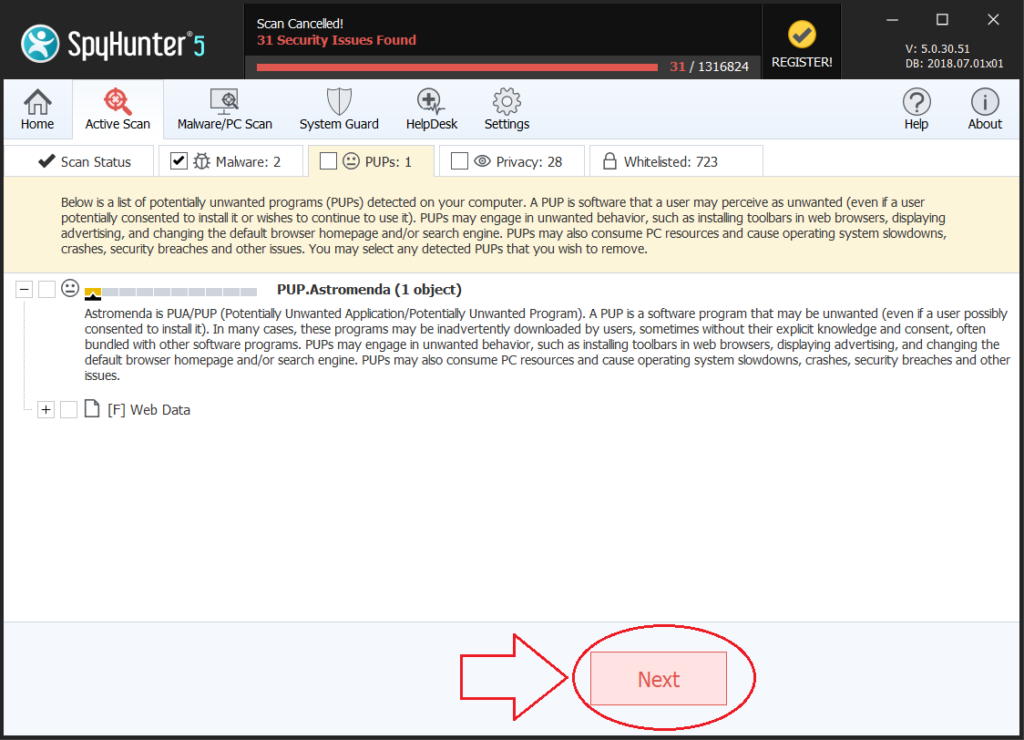
It is advisable to run a free scan before committing to the full version. You should make sure that the malware is detected by SpyHunter first.
Step 5:Recover files encrypted by the Ransomware.
Method 1: Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Most of the currently available decryptors for ransomware viruses can be seen if you visit the NoMoreRansom project – a project that is the result of combined efforts of researchers worldwide to create decryption software for all ransomware viruses. Simply go there by clicking on the following LINK and find your ransomware version decrypter and try it, but always remember to do a BACKUP first.
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files: