This is an article, explain what is Searchlee.com, how to remove it from your computer and how you can get rid of advertisements that are associated with it on your computer.
Searchlee.com is the name of a website, that is likely related to an ad-supported program installed on your computer. Such PUPs (Potentially Unwanted Programs) aim to introduce pop-ups, banners, ad-supported search results, redirects and other forms of ads on your computer. Their primary purpose is to get you to click on the ads that may redirect you to a lot of different websites, whose primary purpose may be to get you to visit a scam page or even infect your PC with malware. If you want to remove redirects from Searchlee.com and try to protect your PC against such intrusive programs in the future, we strongly advise to read this article.
| Threat Name | Searchlee.com |
| Category | Adware/PUP/Browser Hijacker. |
| Main Activity | Slithers onto your computer and heavily modifies your web browser settings to cause advertisements and collect data. Mostly displays browser redirects to Searchlee.com pages. They may ask you to accept Push Notifications. |
| Signs of Presence | Multiple third-party advertisements as well as a slow down in computer performance. |
| Spread | Via software bundling. |
| Detection+Removal | For Windows: DOWNLOAD WINDOWS REMOVAL TOOL FOR Searchlee.com |
How Does Searchlee.com Affect Your PC?
Once Searchlee.com lands on your computer, it modifies the settings of your browser (Mozilla Firefox, Google Chrome or Internet Explorer) and changes its home page to Searchlee.com. As with most browser hijackers, it starts displaying unwanted pop-up ads which will disturb your browsing routine.
The main purpose of Searchlee.com Virus is to generate traffic on its main page, monetizing it in various ways such as pay-per-click schemes profiting from infected visitors to the home page.
The worst part of all, however, is not that you are forced to click on a particular website every time you wish to surf the Web. Or that the search results may be manipulated. Or, that your browsing activities are constantly disturbed by annoying pop-up advertisements. What’s worse is thatSearchlee.com may track your searching habits and record them. Your personal information may then be shared with third parties for advertising and monetization purposes.
How Does Searchlee.com Infiltrate Your PC?
In order to avoid being infected by Searchlee.com, as well as any other malicious software, you must always be alert when browsing the Web. This browser hijacker, for example, can enter your system in a variety of ways- via spam emails and attachments, or bundled with a free program you have downloaded.
The “bundling” practice is quite insidious because you intend to download a specific freeware, but you end up with a potentially unwanted program (PUP) in addition. In most cases, this bundled deal is mentioned throughout the installation process, but because you rarely pay attention to such details, you often miss to opt out of that deal. This way, you become exposed to various threats depending on the essence of the infection.
How Do You Remove Searchlee.com from Your System?
Searchlee.com sneaks into your system without your knowledge, manipulates your search results, collects your personal data, and disturbs your browsing with pop-up ads. These are good reasons to remove Searchlee.com from your PC the moment you realize you have it.
Uninstalling the browser hijacker may not be quite effective, however. It may keep redirecting you to its home page endlessly. Therefore, you must use a reputable anti-malware program to assist you in removing the Searchlee.com.
Preparation before removal of Searchlee.com:
1.Make sure to backup your files.
2.Make sure to have this instructions page always open so that you can follow the steps.
3.Be patient as the removal may take some time.
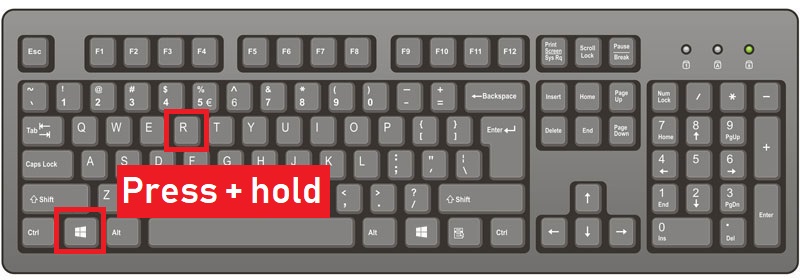
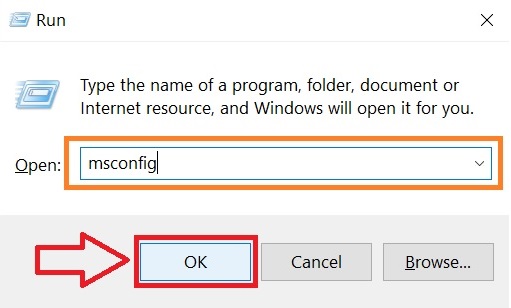
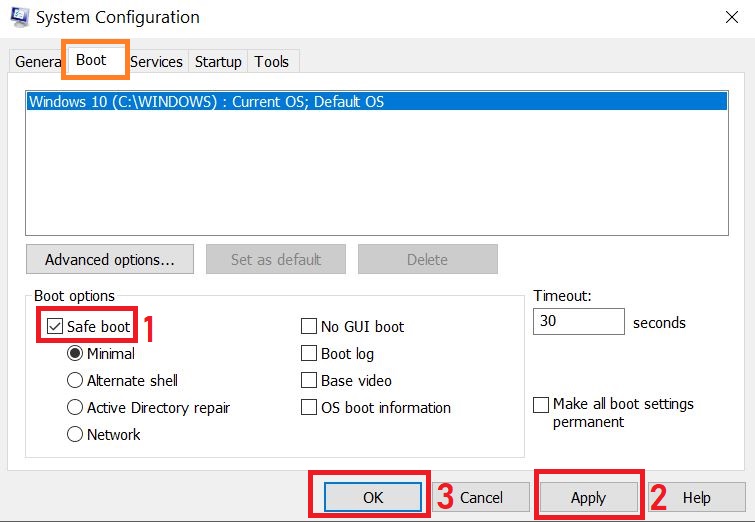
Step 1: Reboot your computer in Safe Mode:
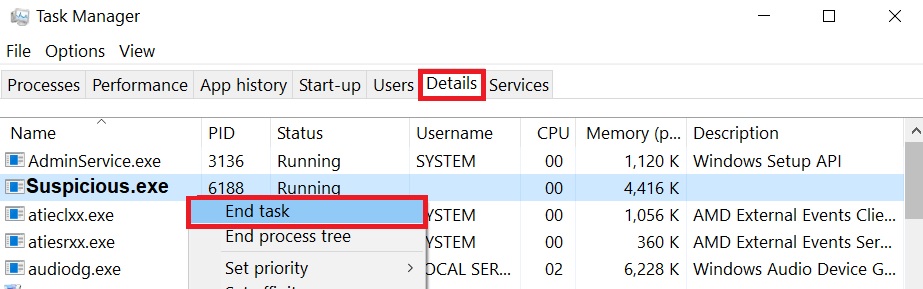
Step 2: Cut out Searchlee.com in Task Manager
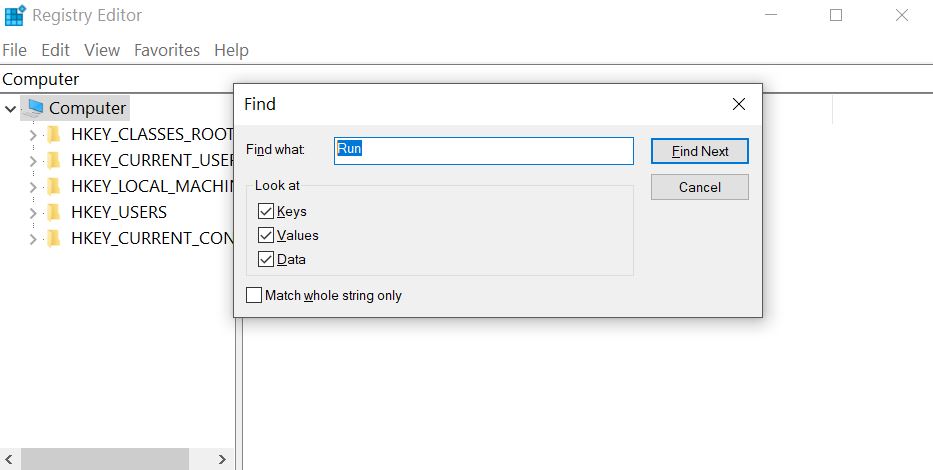
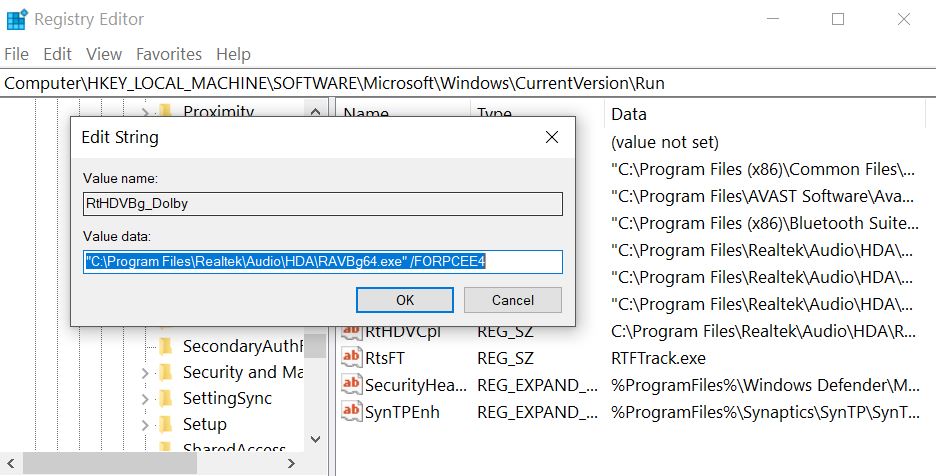
Step 3: Eliminate Searchlee.com‘s Malicious Registries.
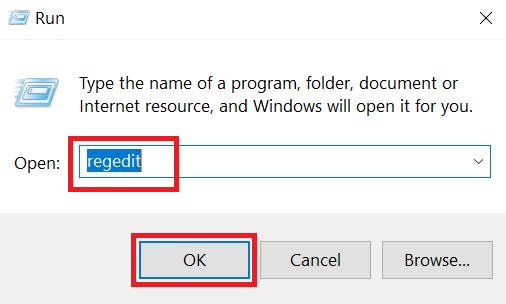
For most Windows variants:
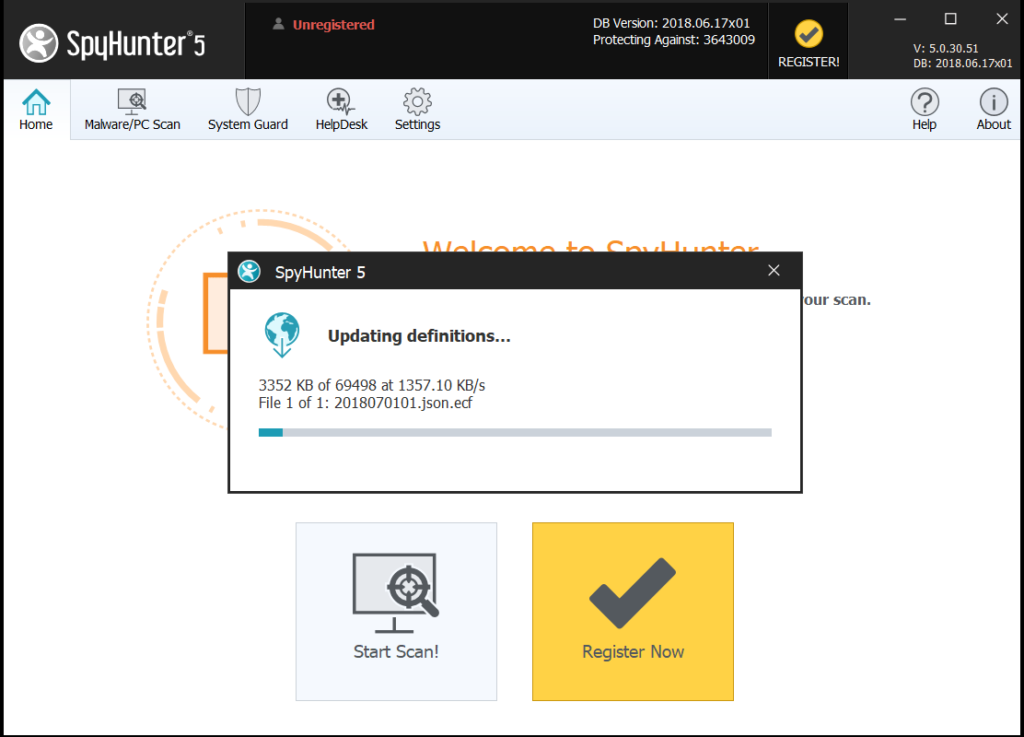
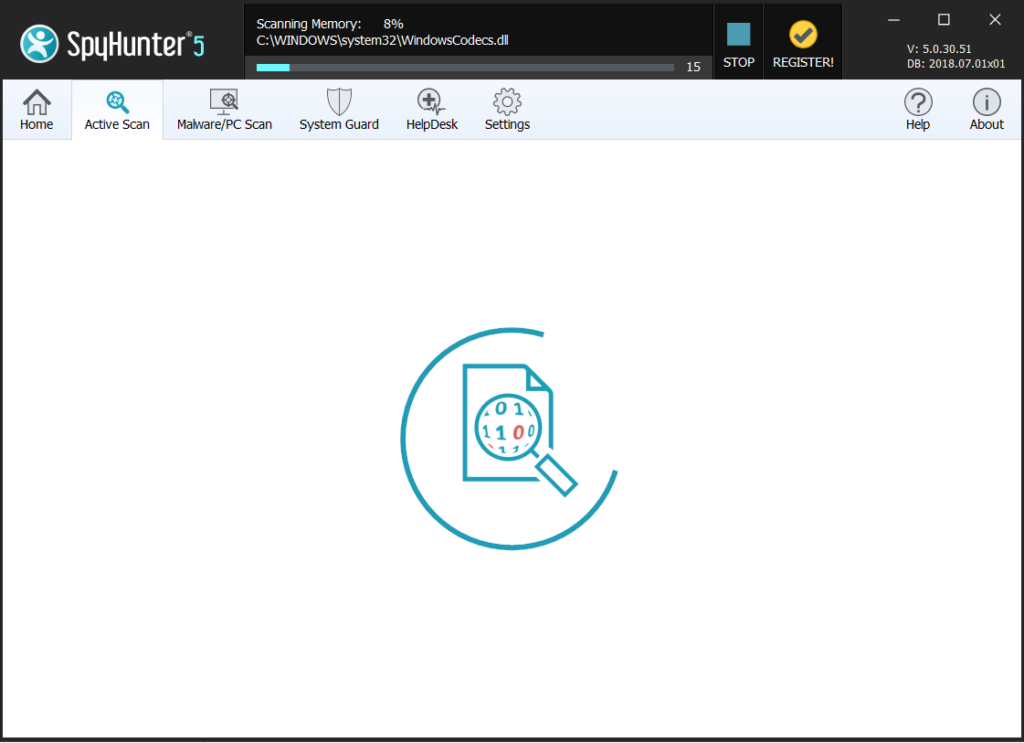
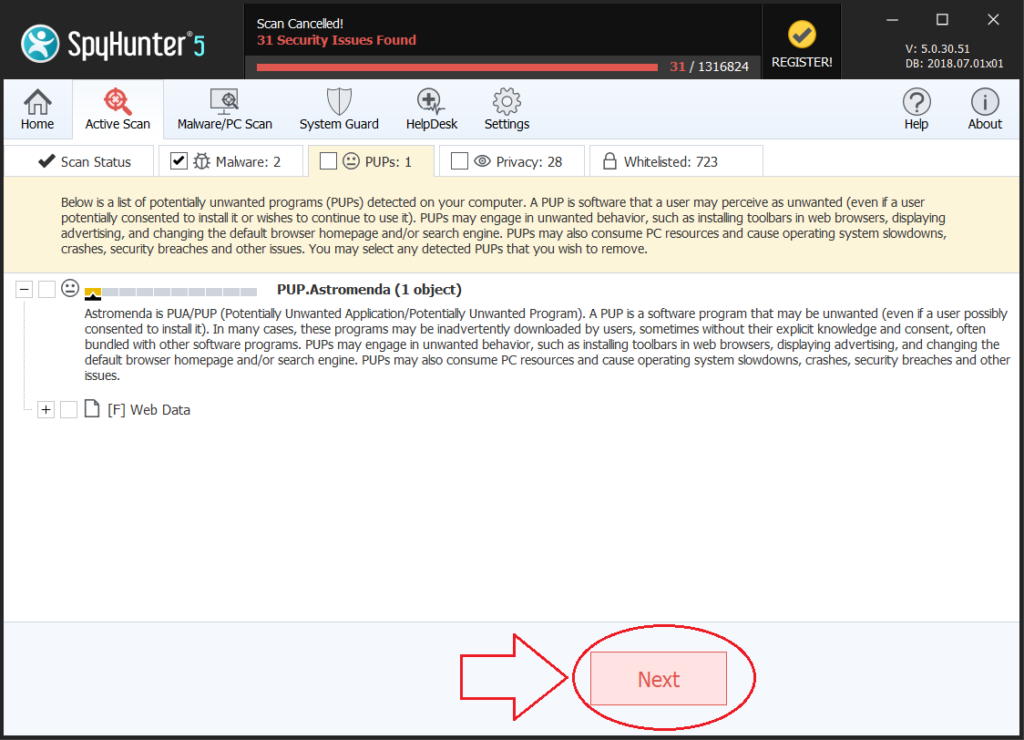
Step 4: Scan for all virus files, related to Searchlee.com and secure your system.
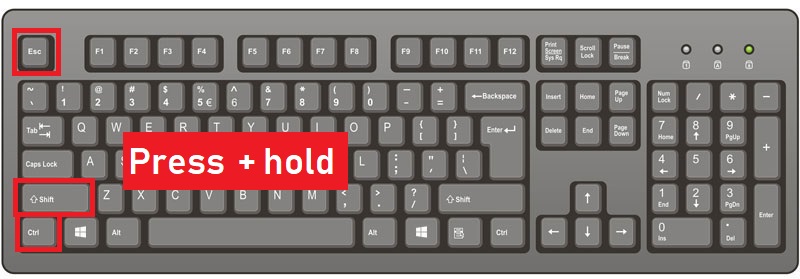
If you are in Safe Mode, boot back into normal mode and follow the steps below
It is advisable to run a free scan before committing to the full version. You should make sure that the malware is detected by SpyHunter first.