This blog post has been made with the purpose to show you what is Ryuk ransomware virus and explain how you can remove this ransomware from your computer and how you can recover files, encrypted by this infection without having to pay the ransom.
The Ryuk ransomware virus, which is believed to be a variant of Hermes ransomware has been reported to infect computers in a massive wave of spammed e-mails. The ransomware virus’s primary purpose is to infect computers while remaining undetected. The ransomware virus then encrypts the files on the computers that have been infected by it so that it can then drop it’s ransom note file, name RyukReadMe.txt which aims to convince victims into paying ransom to get the files to work again. If your computer has been infected by Ryuk, we reccomend that you read this article as it will help you to remove this ransomware virus from your computer effectively and show you how you can try and recover files, encrypted by this ransomware.
| Threat Name | Ryuk Ransomware |
| Category | Ransomware virus. |
| Main Activity | Variant of Hermes ransomware. Infects the computer and then encrypts important documents and holds them hostage until a ransom is paid. |
| Signs of Presence | Files are encrypted with no file extension and the e-mails of the crooks and ransom note are dropped with ransom instructions.. |
| Spread | Via malicious e-mail spam and set of infection tools. |
| Detection+Removal | DOWNLOAD REMOVAL TOOL FOR Ryuk Ransomware |
| File Recovery | Download Data Recovery Software, to see how many files encrypted by Ryuk Ransomware ransomware you will be able to recover. |
What Type of Malware Is the Ryuk Ransomware Ransomware
Ransomware in general has been a growing trend with infection and particularly effective. Dharma ransomware prays primarily on those users who do not have a backup of their important files. The Ryuk Ransomware Ransomware encrypts your important documents, music, videos, pictures, archives and other data, making them no longer effective. The files cannot be opened after they have been attacked by the Ryuk Ransomware Ransomware and they have a custom extension added after their file name – a random A-Z 0-9 letters.
In fact, the infections with ransomware, just like Ryuk Ransomware have become so massive that you can be sure that at the moment somebody somewhere in the world is either opening a suspicious spammed e-mail attachment, believing it is legit or clicking on a malicious web link. The .TRON infection also has a ransom note, typical to most ransomware viruses and it’s called RyukReadMe.txt. It has the following contents:
All files on each host in the network have been encrypted with a strong algorithm.
Backups were either encrypted or deleted or backup disks were formatted.
Shadow copies also removed, so F8 or any other methods may damage encrypted data but not recover.
We exclusively have decryption software for your situation
No decryption software is available in the public.
DO NOT RESET OR SHUTDOWN – files may be damaged.
DO NOT RENAME OR MOVE the encrypted and readme files.
DO NOT DELETE readme files.
This may lead to the impossibility of recovery of the certain files.
To get info (decrypt your files) contact us at
[email protected]
or
[email protected]
BTC wallet:
14hVKm7Ft2rxDBFTNkkRC3kGstMGp2A4hk
Ryuk
No system is safe
But the ransomware can also be spread completely automatically, similar to the previous versions of the Dharma virus which was spread via a e-mail spam messages, causing the data of thousands of computers all over the world to be encrypted. The creators of ransomware who are involved in this act as if they have nothing to lose and do not mess around. They have invested a lot in their attacks and organized them so that as many inexperienced users as possible become victims.
How to Protect Oneself Against Ransomware Viruses?
After the inevitable has happened, you should learn how to prevent it from happening to you in the future. There are several different solutions to ransomware, but they all come down to two main strategy.
Solution number one is to understand what you are dealing with. If the ransomware virus that has infected you, in this case Ryuk Ransomware ransomware, make sure to check our website for any solutions of the threat. Usually most antivirus vendors create decryptors for those ransomware viruses that can be cracked, in other words, which are decryptable. Usually a ransomware virus can be decrypted if there is a mistake in the code written by the hackers who made it or of the encryption algorithm (the language used to make your files non-readable) has a method to be decrypted. Usually, however, most ransom viruses have an immensely strong encryption algorithm and they are non-decryptable. Usually it takes some time do develop a decrypter, but keep following this blog post as we will update with a download link to the tool which can get back your data.
How to Remove Ryuk Ransomware Ransomware and Recovery My Data
The removal process of this virus may prove to be a tricky one. This is primarily because the virus may be involved in several different stages of operation that create mutexes, registry entries and files on your computer. All of the objects created by Ryuk Ransomware Ransomware may be difficult to remove manually and In some situations may even cause harm to your computer. The safest way to remove malicious files, according to experts is to use an advanced tool that hunts specifically for these type of ransomware infections and removes them. Such tool will not get your files back but will scan your computer automatically and delete the virus as fast as possible so that your PC is safe. And after the removal, you can try using some other third-party methods to restore files that have been encrypted by Ryuk Ransomware Ransomware while you wait for antivirus vendors to develop a decrypter.
Booting in Safe Mode
For Windows:
1) Hold Windows Key and R
2) A run Window will appear, in it type “msconfig” and hit Enter
3) After the Window appears go to the Boot tab and select Safe Boot
Cut out Ryuk Ransomware in Task Manager
1) Press CTRL+ESC+SHIFT at the same time.
2) Locate the “Processes” tab.
3) Locate the malicious process of Ryuk Ransomware, and end it’s task by right-clicking on it and clicking on “End Process”
Eliminate Ryuk Ransomware‘s Malicious Registries
For most Windows variants:
1) Hold Windows Button and R.
2) In the “Run” box type “Regedit” and hit “Enter”.
3) Hold CTRL+F keys and type Ryuk Ransomware or the file name of the malicious executable of the virus which is usually located in %AppData%, %Temp%, %Local%, %Roaming% or %SystemDrive%.
4) After having located malicious registry objects, some of which are usually in the Run and RunOnce subkeys delete them ermanently and restart your computer. Here is how to find and delete keys for different versions.
For Windows 7: Open the Start Menu and in the search type and type regedit –> Open it. –> Hold CTRL + F buttons –> Type Ryuk Ransomware Virus in the search field.
Win 8/10 users: Start Button –> Choose Run –> type regedit –> Hit Enter -> Press CTRL + F buttons. Type Ryuk Ransomware in the search field.
Automatic Removal of Ryuk Ransomware
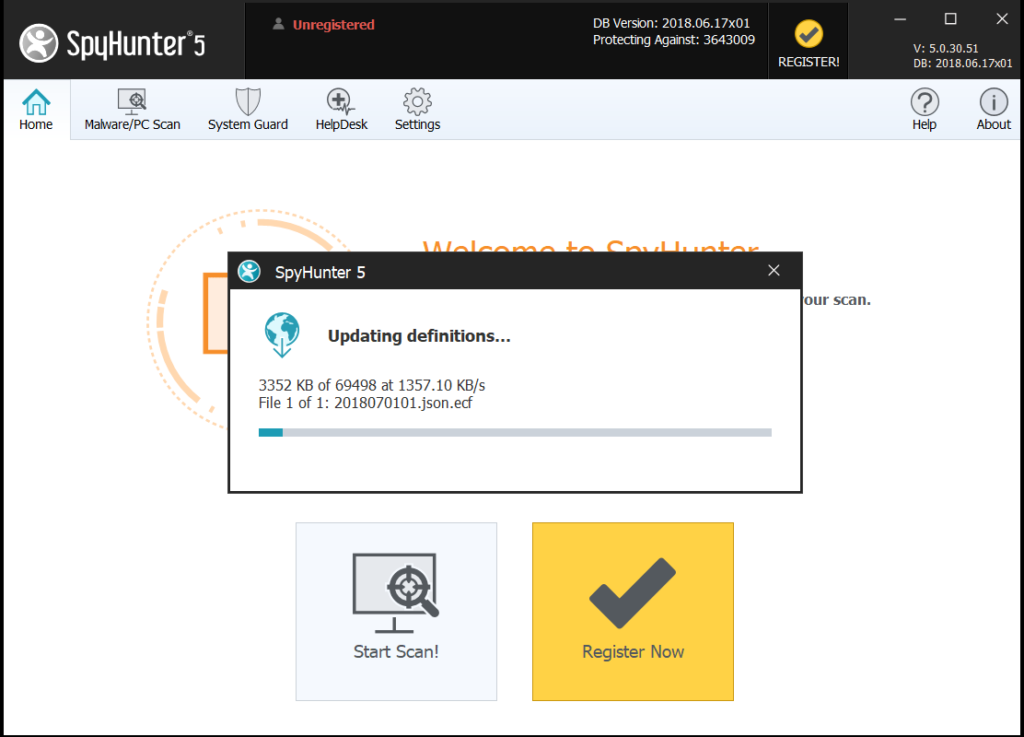
Step 1:Click on the button to download SpyHunter’s installer.
It is advisable to run a scan before committing to purchase the full version. You should make sure that the malware is detected by SpyHunter first.
Step 2: Guide yourself by the download instructions provided for each browser.
Step 3: After you have installed SpyHunter, wait for the program to update.
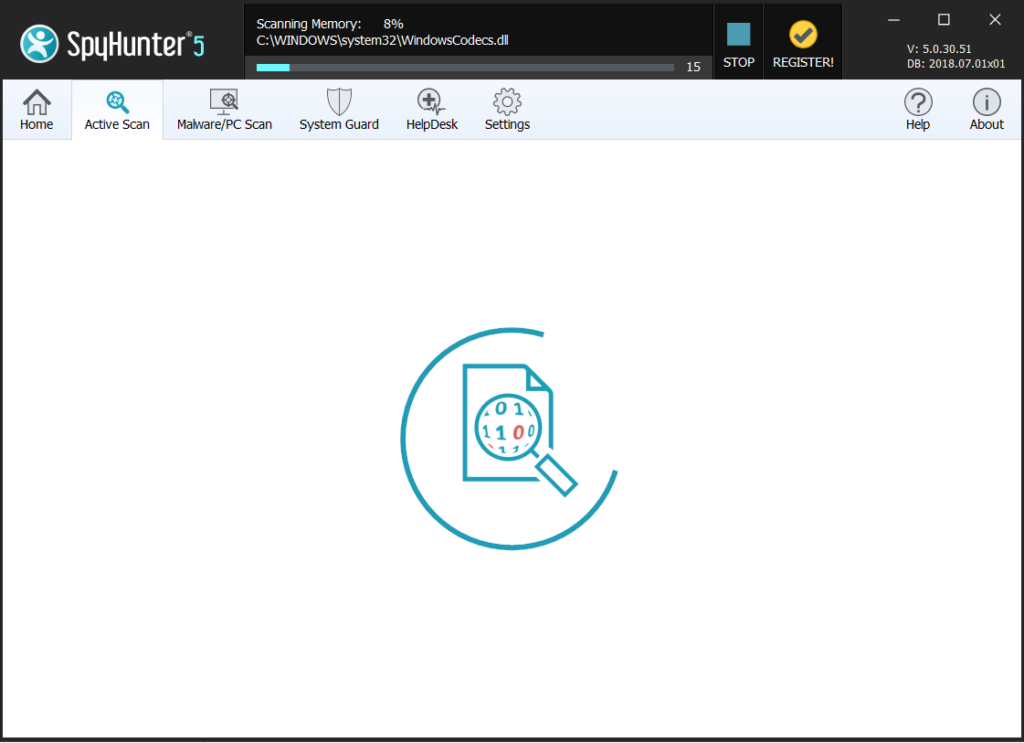
Step4: If the program does not start to scan automatically, click on the “Scan Computer Now” button.
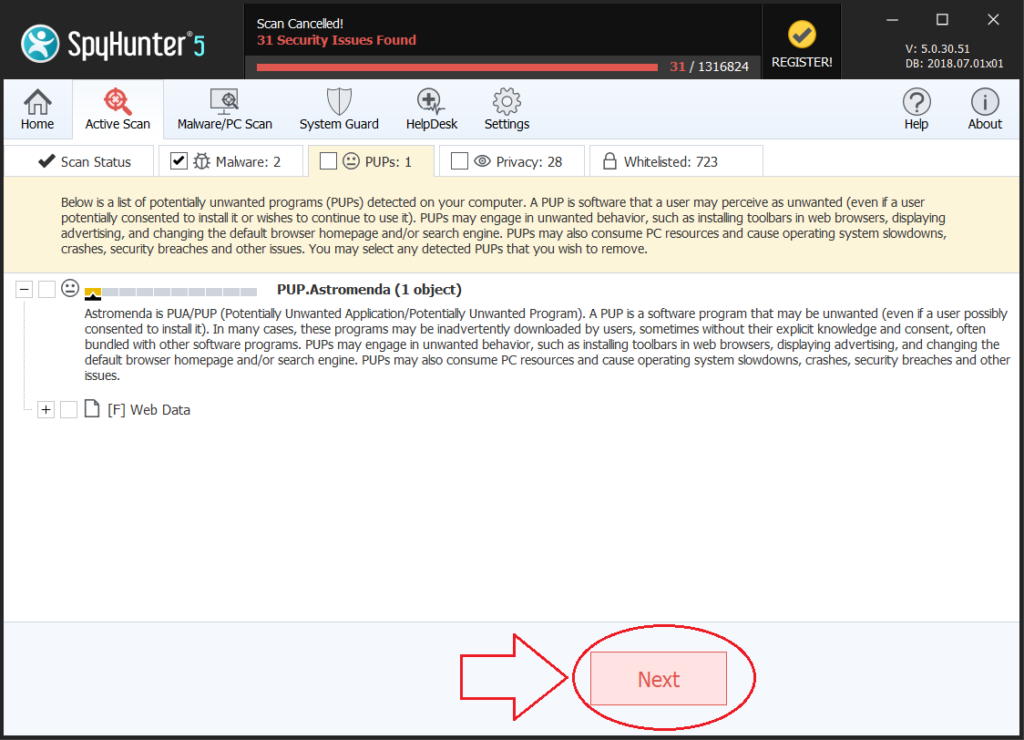
Step5: After SpyHunter has completed with your system`s scan, click on the “Next” button to clear it.
Step6: Once your computer is clean, it is advisable to restart it.
Recover files encrypted by the Ryuk Ransomware Ransomware.
Method 1: Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Here are the vendors to look for:
- Kaspersky.
- Emsisoft.
- TrendMicro.
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files: