This post’s purpose is to show to you what is the rundll32 virus popping up on your computer and show you ways via which you can remove it from your computer.
Several viruses, using the rundll32 system process were the reason of multiple reports by victims that they detected the file as a virus. The original rundll32 file belongs to Windows, however if you receive malware detections, chances are that your computer has either a virus or a Trojan type of malware in it and it needs to be removed right away, since all your passwords and information may be at stake.
| Threat Name | Rundll32 Virus |
| Category | Trojan Horse. |
| Main Activity | Slithers onto your computer and may steal information from it. A heuristic detection for most conventional trojan horses. |
| Signs of Presence | Slow PC, changed settings, error messages, suspicious PC behavior. Logins from unknown sources on your online accounts. |
| Spread | Via malicious e-mail spam and set of infection tools. |
| Detection+Removal | DOWNLOAD REMOVAL TOOL FOR Rundll32 Virus
Note!For Mac users, please use the following instructions. |
What Harm Can Rundll32 Virus Trojan Do to My PC?
In this digital age, Trojan horses can be very significant not only to your computer, but to you as well. Since most users keep their important files on computers, all of their crucial information becomes at risk. This means that your personal ID number or other financial data that you may have used on a computer infected by _ Trojan can be compromised and used for malicious purposes. This is the primary reason why this threat should be dealt with immediately.
The reason why Trojans, like the Rundll32 Virus Trojan are a significant threat, is that it has multiple different malicious functions that are utilized on your computer. The features of a Trojan may vary, depending on what type it is, but it is safe to assume that the _ Trojan can do the following on your PC:
- Steal the passwords from the computer and obtain the keystrokes from it via Keyloggers.
- Destroy data on your computer, like delete files. This may even result in damaging your Windows.
- Remotely monitor your activity. This means that whatever you do and see on your screen, the hacker who infected you can also see.
- Disable your Windows operating system via a DDoS attack (Denial of Service).
- Use your system’s resources (CPU and Video Card) to mine cryptocurrencies, like BitCoin.
- Harvest system data and login information automatically from your web browsers.
- Install other viruses on your computer which may cause even more damage.
- Display fake tech support screens that can lure you into a scam.
How to Spot and Fully Eliminate the Rundll32 Virus Trojan?
The primary method which you can use to detect a Trojan is to analyze hidden processes on your computer. This is achievable by downloading process monitoring apps, like Process Explorer. However, you will have to have a trained eye on how to detect the malicious processes and how to remove those without damaging your computer. This is why, as a swift solution, a Trojan-specific removal tool should be used, according to security experts. Such removal software will automatically scan for Trojans like Rundll32 Virus and get rid of them quickly and safely while protecting your computer against threats in the fut
Booting in Safe Mode
For Windows:
1) Hold Windows Key and R
2) A run Window will appear, in it type “msconfig” and hit Enter
3) After the Window appears go to the Boot tab and select Safe Boot
Cut out Rundll32 Virus in Task Manager
1) Press CTRL+ESC+SHIFT at the same time.
2) Locate the “Processes” tab.
3) Locate the malicious process of Rundll32 Virus, and end it’s task by right-clicking on it and clicking on “End Process”
Eliminate Rundll32 Virus‘s Malicious Registries
For most Windows variants:
1) Hold Windows Button and R.
2) In the “Run” box type “Regedit” and hit “Enter”.
3) Hold CTRL+F keys and type Rundll32 Virus or the file name of the malicious executable of the virus which is usually located in %AppData%, %Temp%, %Local%, %Roaming% or %SystemDrive%.
4) After having located malicious registry objects, some of which are usually in the Run and RunOnce subkeys delete them ermanently and restart your computer. Here is how to find and delete keys for different versions.
For Windows 7: Open the Start Menu and in the search type and type regedit –> Open it. –> Hold CTRL + F buttons –> Type Rundll32 Virus Virus in the search field.
Win 8/10 users: Start Button –> Choose Run –> type regedit –> Hit Enter -> Press CTRL + F buttons. Type Rundll32 Virus in the search field.
Automatic Removal of Rundll32 Virus
Step 1:Click on the button to download SpyHunter’s installer.
It is advisable to run a scan before committing to purchase the full version. You should make sure that the malware is detected by SpyHunter first.
Step 2: Guide yourself by the download instructions provided for each browser.
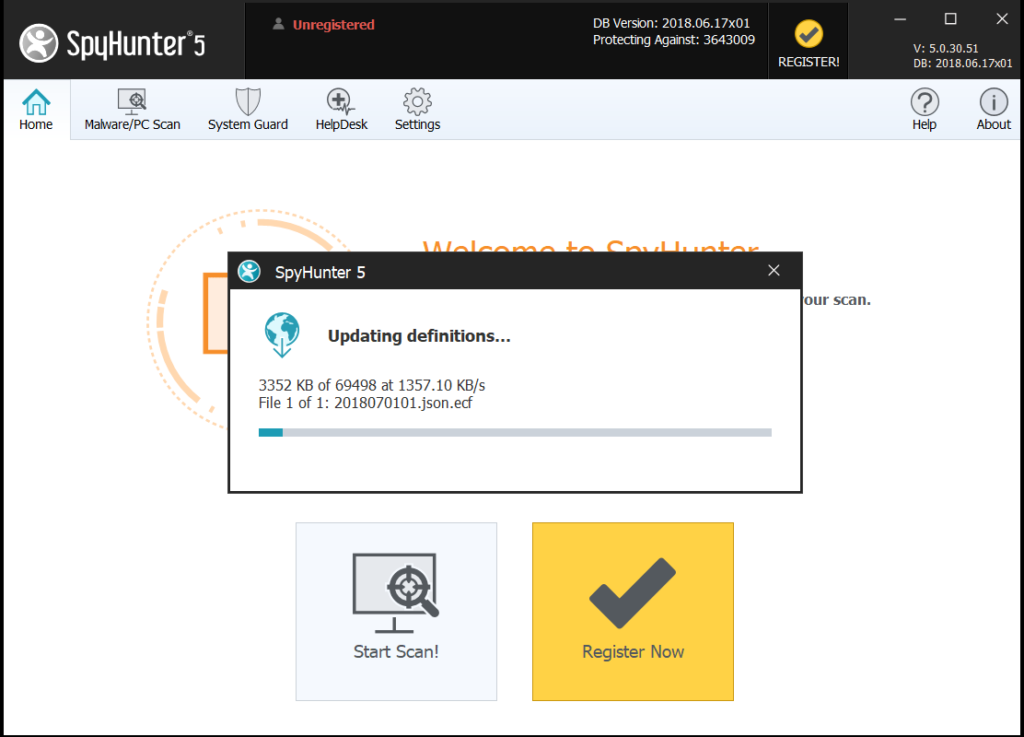
Step 3: After you have installed SpyHunter, wait for the program to update.
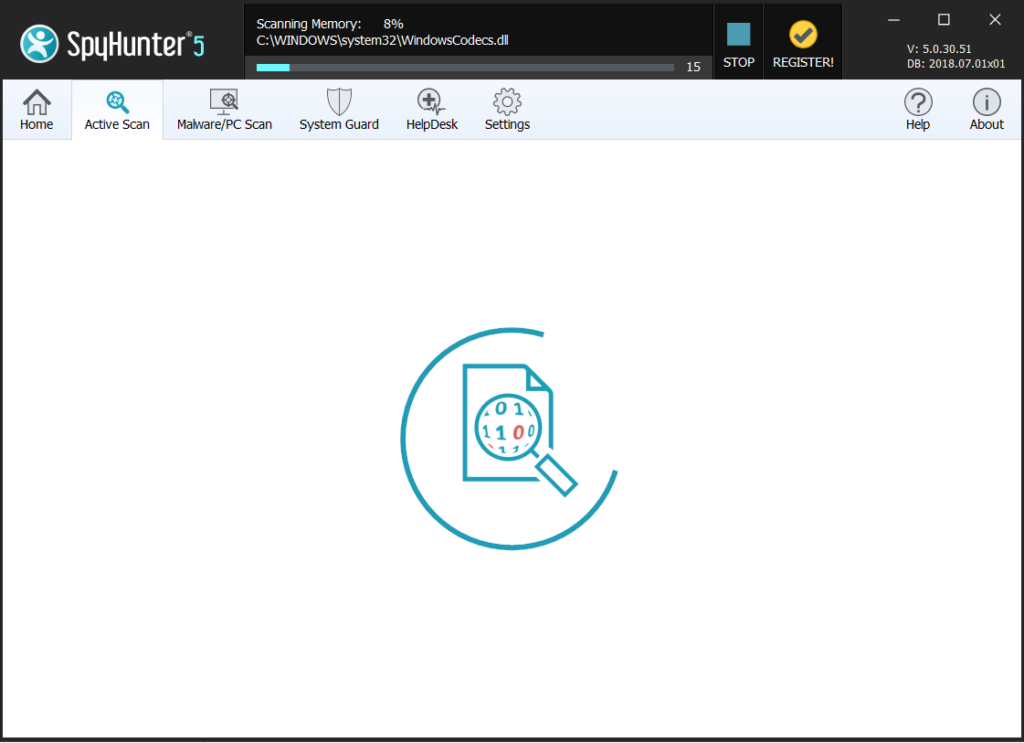
Step4: If the program does not start to scan automatically, click on the “Scan Computer Now” button.
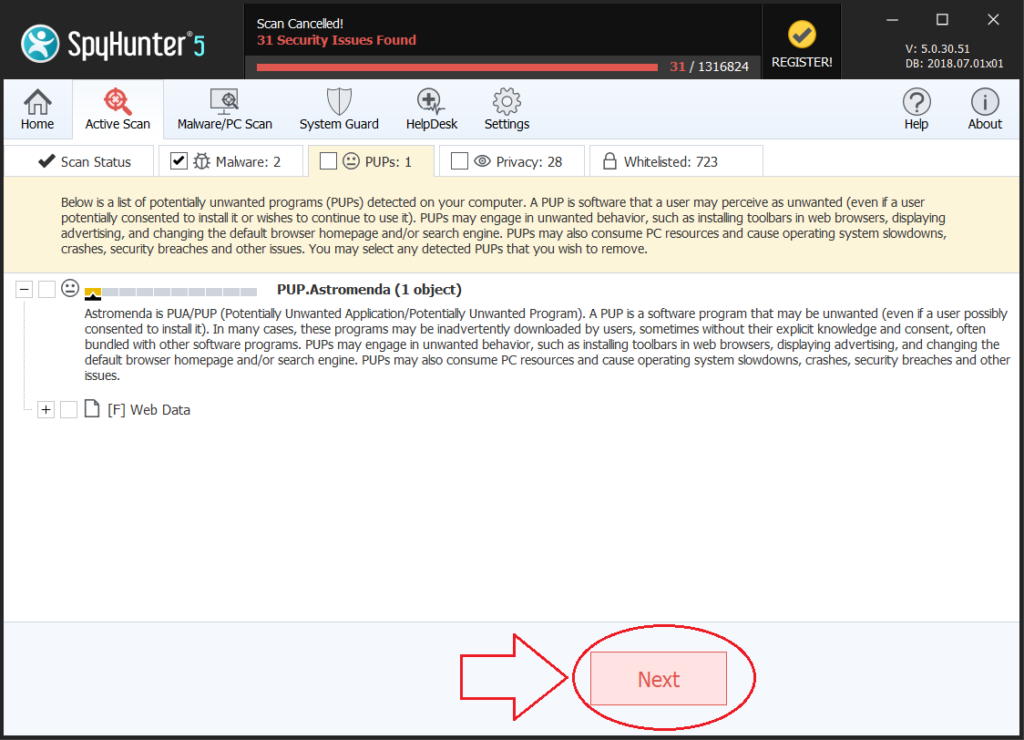
Step5: After SpyHunter has completed with your system`s scan, click on the “Next” button to clear it.
Step6: Once your computer is clean, it is advisable to restart it.