Os pesquisadores de segurança identificaram um novo vírus ransomware KillDisk que se baseia o malware originais distribuídos pelos hackers Telebots coletivas. Para remover as ameaças existentes e proteger seu computador contra malware continue lendo nosso guia de remoção.
Sobre o KillDisk Ransomware
O ransomware KillDisk é um vírus muito perigoso, que tem suas origens da malwares KillDisk usado pelos hackers Telebots coletivas. O ransomware é criado usando a linguagem de programação Python e usa a API Telegram para se comunicar com os operadores remotos. Durante a análise do vírus, foi descoberto que as amostras de vírus individuais contêm tokens. Isto significa que cada hospedeiro infectado usa sua própria conta Telegram para se comunicar com os hackers.
O ransomware KillDisk usa um mecanismo de criptografia muito perigoso para comprometer os arquivos afetados. Ele tem como alvo os arquivos de dados de usuários mais usados. O vírus pode afetar até mesmo arquivos localizados em compartilhamentos de rede montados, dispositivos removíveis e todas as partições locais. Além disso, cada arquivo individual é criptografada com a sua própria chave privada e, em seguida, é adicionada uma outra camada de criptografia.
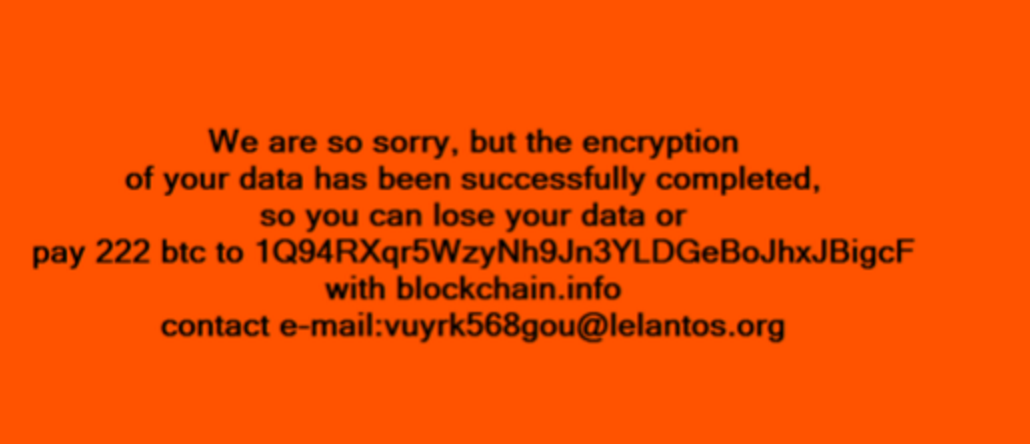
Os proprietários de dispositivos são mostrados a seguinte nota ransomware:
Nós sentimos muito, mas a criptografia
de seus dados foi concluída com sucesso,
assim você pode perder seus dados ou
pagar 222 BTC para Q194RXqr5WzyNh9Jn3YLDGeBoJxJBigcF
com informações blockchain
email de contato: [email protected]
Quando o vírus é instalado no sistema de destino também se registra como um serviço do sistema e pode terminar vários processos.
Como é que a infectar computadores KillDisk ransomware
Os alvos ransomware KillDisk vítimas principalmente industriais e de alto perfil. Alguns dos relatórios indicam que os operadores criminais do vírus alvo plantas, principalmente de produtos químicos localizada na Europa.
O malware é distribuído principalmente através de exploits de software e ataques de hackers diretos.
Como remover o KillDisk ransomware e recuperar arquivos afetados
Você pode usar uma solução anti-spyware confiável para remover infecções ativas e proteger o seu computador .
