 EN 1.1 versjon av CryptoShield 1.0 ransomware er oppdaget ved hjelp av samme .cryptoshield vedlegg om filene Den krypterer. Den ransomware Viruset ble først påvist ved anvendelse av den samme forlengelse, men den nylig modifiserte versjonen omfatter også forbedringer i krypteringsalgoritme, så vel som andre rettelser. Hva er den viktigste endringen er at dette ransomware virus bruker den nyeste RIG-V utnytte kit å forårsake infeksjoner uoppdaget. Hold leser denne artikkelen for å lære hvordan å fjerne dette viruset fra datamaskinen og forsøke å gjenopprette filene dine i tilfelle de har blitt kryptert av det.
EN 1.1 versjon av CryptoShield 1.0 ransomware er oppdaget ved hjelp av samme .cryptoshield vedlegg om filene Den krypterer. Den ransomware Viruset ble først påvist ved anvendelse av den samme forlengelse, men den nylig modifiserte versjonen omfatter også forbedringer i krypteringsalgoritme, så vel som andre rettelser. Hva er den viktigste endringen er at dette ransomware virus bruker den nyeste RIG-V utnytte kit å forårsake infeksjoner uoppdaget. Hold leser denne artikkelen for å lære hvordan å fjerne dette viruset fra datamaskinen og forsøke å gjenopprette filene dine i tilfelle de har blitt kryptert av det.
Mer info på CryptoShield 1.1 Virus
Hensikten med denne ransomware virus er å bruke kryptering for å gjengi filene på datamaskinen ikke lenger i stand til å bli åpnet av brukeren. Viruset utfører også andre ondsinnede aktiviteter på datamaskinen, som berører noen filer i Windows Registry Editor samt starte prosesser i Windows Task Manager for å kryptere data. Den CryptoShield 1.1 ransomware kan også utføre privilegerte kommandoer, slik som vssadmin kommando som sletter skyggekopien sikkerhetskopier på den kompromitterte maskinen.
Men dette er ikke alt. Den CryptoShield 1.1 ransomware er også svært aktive når det gjelder å kryptere filer. For å utføre kryptering, viruset bruker ROT-13-modus for å kryptere filer i AES-256 kryptering. Deretter, viruset legger det særegne .cryptoshield filutvidelse, for eksempel Word File.doc.CRYPTOSHIELD.
Men da, den ransomware viruset legger også en # Gjenoppretting av filer # .txt og # Gjenoppretting av filer # HTML-filer som er det faktiske løsepenger notat. Notatet er svært lik andre ransomware virus som har blitt kjent før, blant hvilke er flere CryptoLocker, XTBL og CryptoWall varianter. Mange ransomware eksperter anser dette viruset en CryptoWall copycat.
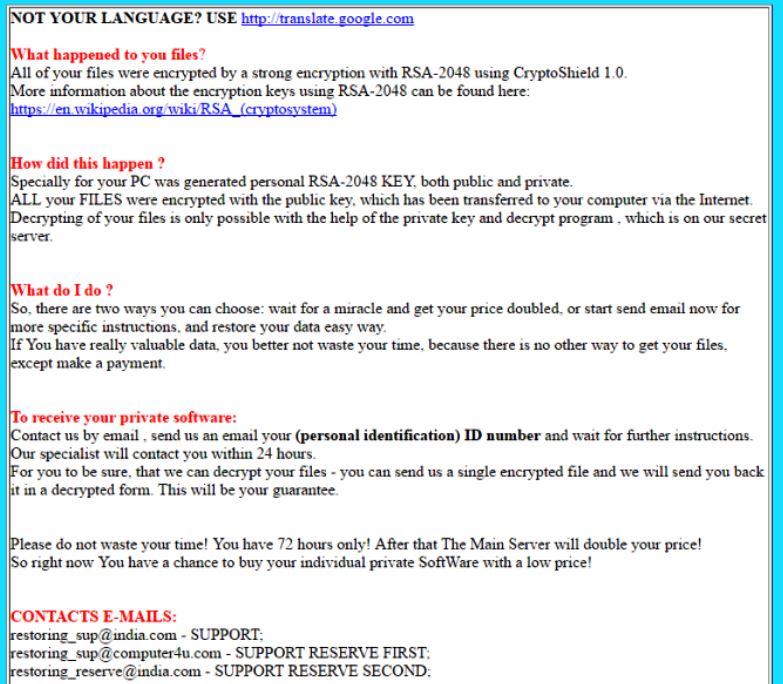
Løsepenger notat av viruset er følgende:
IKKE DITT SPRÅK? BRUK http://translate.google.com
Hva har skjedd med deg filer?
Alle filene ble kryptert med en sterk kryptering med RSA-2048 ved hjelp CryptoShield 1.1
Mer informasjon om krypteringsnøklene ved hjelp av RSA-2048 finner du her: https://en.wikipedia.org/wiki/RSA_(kryptosystem)
Hvordan skjedde dette ?
Spesielt for PCen ble generert personlig RSA-2048 KEY, både offentlig og privat.
Alle filer ble kryptert med den offentlige nøkkelen, som har blitt overført til datamaskinen via Internett.
Dekryptering av filene dine er bare mulig ved hjelp av den private nøkkelen og dekryptere program, som er på vår hemmelighet serveren.
Hva gjør jeg ?
Så, Det er to måter du kan velge: vente på et mirakel og få prisen doblet, eller begynne å sende e-post nå for mer spesifikke instruksjoner, og gjenopprette data enkel måte.
Hvis du har veldig verdifulle data, du bedre ikke kaste bort tiden din, fordi det er ingen annen måte å få filene dine, bortsett foreta en betaling.
For å motta din private programvare:
Kontakt oss via e-post , send oss en e-post til (personlig identifikasjon) ID-nummer og vente på videre instruksjoner.
Vår ekspert vil kontakte deg innen 24 timer.
For at du skal være sikker, at vi kan dekryptere filene dine – du kan sende oss en enkelt kryptert fil, og vi vil sende deg tilbake det i en dekryptert skjema.
Dette vil være din garanti.
Vennligst ikke kaste bort tiden din! Du har 72 bare timer! Etter at hovedserveren vil doble prisen!
Så akkurat nå har du en sjanse til å kjøpe din egen private programvare med en lav pris!
Kontakter E-POST:
[email protected] – BRUKERSTØTTE;
[email protected] – STØTTE RESERVE FØRSTE;
[email protected] – STØTTE RESERVE ANDRE;
ID:
Konklusjon, Fjerning og File Restaurering av CryptoShield 1.1 Virus
Noen ord til slutt, CryptoShield 1.1 ransomware er et virus som har som mål å overbevise deg til å betale en heftig avgift og få filene tilbake. Men, malware analytikere på det sterkeste mot å samarbeide med cyber-kriminelle bak CryptoShield, fordi du ikke kan få filene tilbake og dess du hjelpe cyber-kriminelle i sin ondsinnet aktivitet.
Det er derfor en anti-malware støtte må innhentes ved å fjerne denne malware. Du kan følge våre instruksjoner for fjerning for å bli kvitt dette viruset, og i tillegg til dette, eksperter anbefaler å bruke en avansert anti-malware program som den beste måten å bli kvitt alle de skadelige filer, endrede filer og andre gjenstander laget av CryptoShield 1.1 på datamaskinen.
For å prøve og gjenopprette filene dine, Vi anbefaler deg også å følge rådene vi har skrevet under. Det er flere metode som ikke er garantert å bli en suksess, men du kan prøve, tross alt, i det minste inntil et decryptor frigjøres.
Starter i sikkermodus
for Windows:
1) Holde Windows-tasten og R
2) En kjøre Window vises, i den typen “msconfig” og traff Tast inn
3) Etter vinduet vises gå til kategorien Boot og velg Sikker oppstart
Skjær ut CryptoShield i Task Manager
1) trykk CTRL + ESC + SHIFT samtidig.
2) Finn “prosesser” Kategorien.
3) Finn skadelig prosessen med CryptoShield, og avslutte den oppgave ved å høyreklikke på den og klikke på “Avslutt prosess”
Eliminer CryptoShield er Skadelige Meldingssystem
For de fleste Windows-varianter:
1) Holde -Knappen i Windows og R.
2) i “Løpe” bokstype “regedit” og traff “Tast inn”.
3) Holde CTRL + F nøkler og typen CryptoShield eller filnavnet til ondsinnet kjørbar av viruset som vanligvis ligger i% AppData%, %temp%, %lokal%, %Roaming% eller% System%.
4) Etter å ha plassert ondsinnede registerobjekter, hvorav noen er vanligvis i Run og RunOnce nøklene slette dem ermanently og starte datamaskinen på nytt. Her er hvordan du kan finne og slette nøkler for forskjellige versjoner.
for Windows 7: Åpne Start-menyen og i regedit søketype og type -> åpne det. -> Hold CTRL + F knapper -> Type CryptoShield Virus i søkefeltet.
Vinne 8/10 brukere: Startknapp -> Velg Kjør -> skriv regedit -> Hit Enter -> Trykk CTRL + F-knapper. Skriv CryptoShield i søkefeltet.
Automatisk fjerning av CryptoShield
Gjenopprette filer kryptert ved CryptoShield Ransomware.
Metode 1: Bruke Shadow Explorer. I tilfelle du har aktivert File historie på din Windows-maskin er en ting du kan gjøre er å bruke Shadow Explorer for å få filene tilbake. Dessverre noen ransomware virus kan slette disse skygge volum kopier med en administrativ kommando for å hindre deg fra å gjøre nettopp det.
Metode 2: Hvis du prøver å dekryptere filene dine ved hjelp av tredjeparts dekryptering verktøy. Det er mange antivirusleverandører som har dekryptert flere ransomware virus de siste par årene, og postet decryptors for dem. Sjansene er hvis ransomware virus bruker samme krypteringskoden som brukes av en decryptable virus, du kan få filene tilbake. Men, Dette er heller ikke en garanti, så kan det være lurt å prøve denne metoden med kopier av de originale krypterte filer, fordi hvis et tredjepartsprogram tukler med deres kryptert struktur, kan de bli skadet permanent. Her er leverandører til å se etter:
- Kaspersky.
- Emsisoft.
- Trendmicro.
Metode 3: Bruke Data Recovery verktøy. Denne metoden er foreslått av flere eksperter på området. Den kan brukes til å skanne harddisken er sektorene og dermed rykke de krypterte filene på nytt som om de ble slettet. De fleste ransomware virus vanligvis slette en fil og opprette en kryptert kopi for å hindre at slike programmer for å gjenopprette filene, men ikke alle er dette sofistikerte. Så du kan ha en sjanse til å gjenopprette noen av filene dine med denne metoden. Her er flere data utvinning programmer som du kan prøve og gjenopprette minst noen av filene dine:
