This article aims to help you by showing you how to remove the Nnuz ransowmare virus and show other options on how to restore encrypted files by it without having to pay the ransom.
Yet another nameless virus, displaying the Nnuz extension after the files it has encrypted has appeared. The ransomware makes it so that the files which are important on its victims’ computers are locked and the only way to make them usable again is via a unique decryption key. This key is sold for money by the cyber-criminals who usually drop a ransom note to notify victims of the situation. If you are one of the victims of Nnuz ransomware, you should read this article and learn how to delete all associated virus files of this threat and how to restore Nnuz encrypted files.
| Threat Name | Nnuz |
| Category | Ransomware/Cryptovirus. |
| Main Activity | Infects the computer after which encrypts important documents and holds them hostage until a ransom is paid. |
| Signs of Presence | Files are encrypted with a custom file extension and users are extorted to pay ransom to get the data to work again.. |
| Spread | Via malicious e-mail spam and set of infection tools. |
| Detection+Removal | DOWNLOAD REMOVAL TOOL FOR Nnuz
Note!For Mac users, please use the following instructions. |
Nnuz is advanced cryptomalware that uses file-encoding ciphers to make the data of the unsuspecting victim unreadable. The computer security specialists call this type of Trojans ransomware. The purpose of Nnuz is not to ruin the Operating System (OS) of the user or delete his files permanently. Instead, the hackers want to profit financially by their harmful application. The encryption that Nnuz causes is reversible, but you will need a decryption key. The cyber criminals want to sell it to you for a hefty price, which is technically a ransom. Some victims succumb to the pressure and pay the price for the unlocking tool, but you should not be one of them. If you do it, you may lose your cash alongside the files because you can never trust crooks. The suggestion of the specialists is to be careful during your online sessions in order to prevent the infection with Nnuz.
How Did You Get Infected by Nnuz?
Malware research experts have managed to detect the exact distribution tactic of this aggressive Trojan. Just like many other forms of ransomware, Nnuz tries to deceive the user that it is an innocent file. The payload of this cyber threat tries to resemble legitimate program and popular applications. Some people may agree to click on it, assuming nothing bad will happen. If instead of the original version you activate Nnuz, your system may suffer serious damage. The ransomware comes as an ‘.exe’ file as opposed to other file-encoding Trojans that come as MS Office documents. Not only is the icon identical – Nnuz even copies some signatures to confuse some antivirus tools. The payload of this ransomware may arrive to your email address as an attachment. If you click on some corrupt links, you may be transferred towards malicious sites that host the Trojan. Other options for the infection to occur involve spam in the social networks or infected files uploaded to file-sharing platforms. Since the hackers are becoming more ingenious with each day, it is advisable to have powerful security software that can shield you from incoming threats.
Which Files Are the Primary Target of Nnuz?
The developers of ransomware try to lock as many files as possible. The only data they don’t focus is usually related to the Windows processes. If they mess up the registries, .dll files or system files, your whole OS may fail to load. Such an outcome is not desired by the hackers since they will never receive any ransoms. Unfortunately, dozens of other files may be encrypted with an AES-256 ciphers, which are known to be very hard to break. If you don’t interrupt the encryption process while it is still ongoing, you should expect to lose access to all of your documents, multimedia materials, databases, projects, notes and program-related files. The easiest way to recover the lost data is to unlock it with the original decryption key. Unfortunately, it may be easier said than done to get this tool for free. Once the encryption finishes, the only copy of the decryption key will be automatically sent towards the Command and Control (C&C) servers of the hackers. If the computer security experts manage to breach these servers, they may extract the decryption keys database and release it for free. Unfortunate, as of now, their efforts have not been successful.
How to Resolve the Issue When You Have Been Hit Nnuz?
This ransomware is not among those cyber threats, which impact can be stopped when they are deleted. Even if the Trojan and all files associated with its harmful activities are gone, your personal data may remain encrypted. The hackers count on this fact to threaten the victim and extort money from him. The fact that you may lose data, however, doesn’t mean that you have to pay. The one thing you should remain is that the hackers often scam the users and after receiving the money, they don’t send the decrypting software. If this problem occurs, you will not receive a refund because the developers of Nnuz rely on the Bitcoin platform. Instead of losing your cash this way, you should delete the aggressive ransomware with a dedicated anti-malware utility. When the PC is clean, you can download some decrypting software or try to revert your machine to an earlier date via the System Restore feature.
Preparation before removal of Nnuz:
1.Make sure to backup your files.
2.Make sure to have this instructions page always open so that you can follow the steps.
3.Be patient as the removal may take some time.
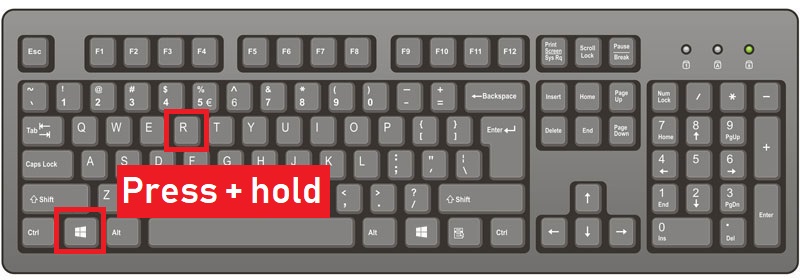
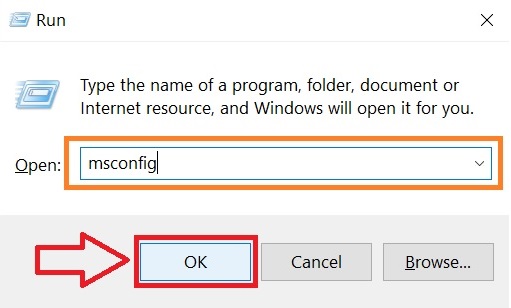
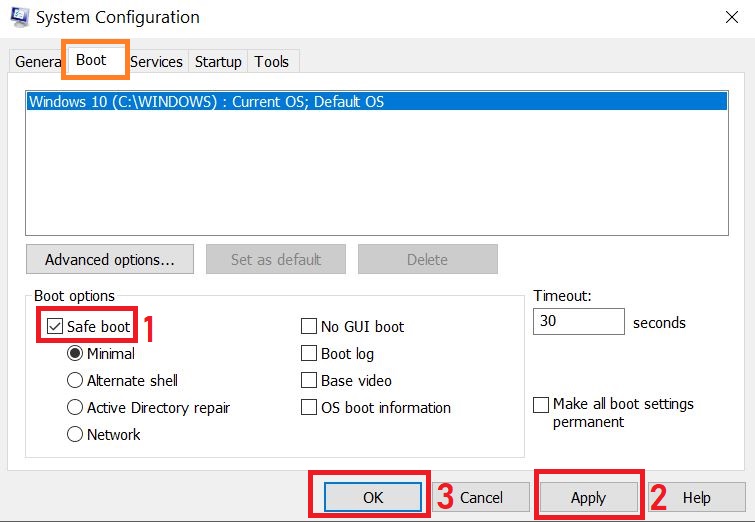
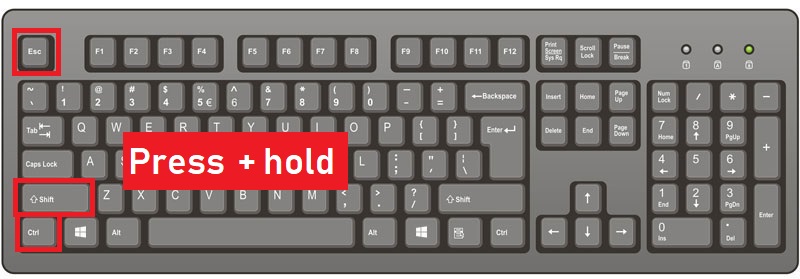
Step 1: Reboot your computer in Safe Mode:
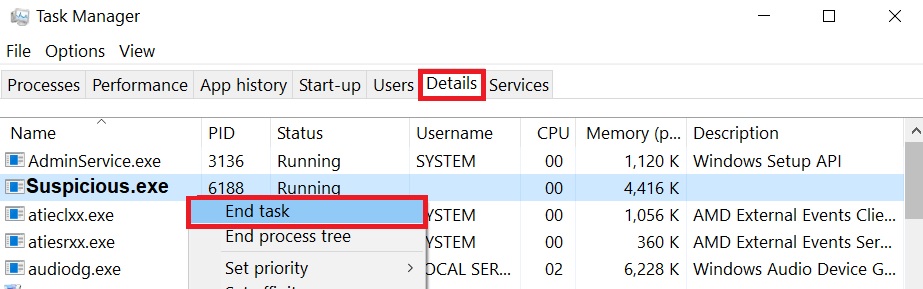
Step 2: Cut out Nnuz in Task Manager
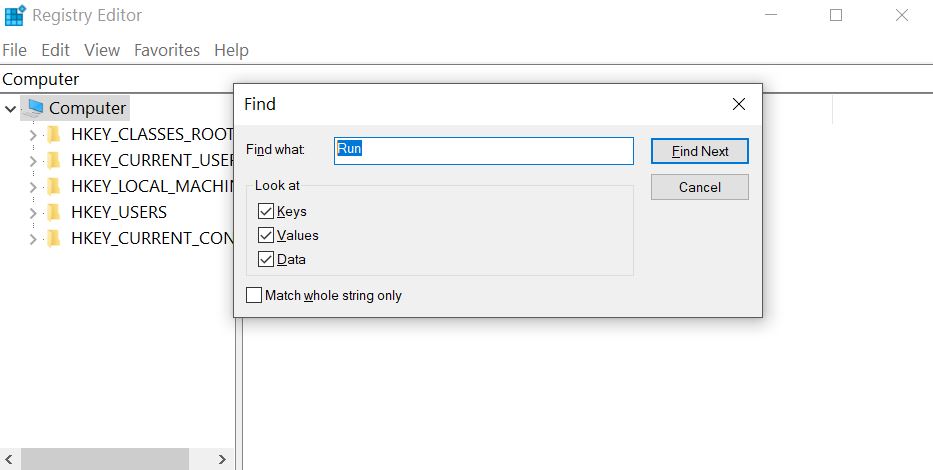
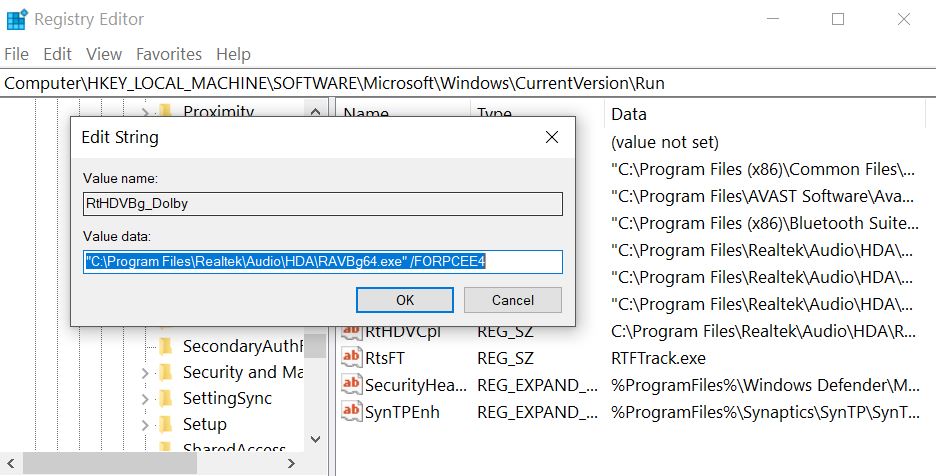
Step 3: Eliminate Nnuz‘s Malicious Registries.
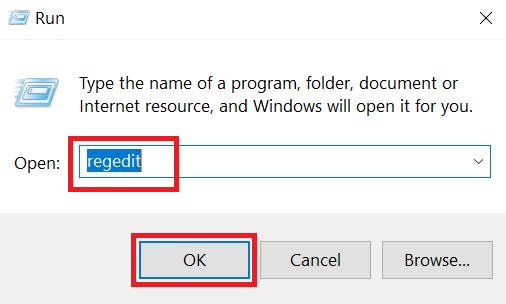
For most Windows variants:
Step 4: Scan for and remove all virus files, related to Nnuz and secure your system.
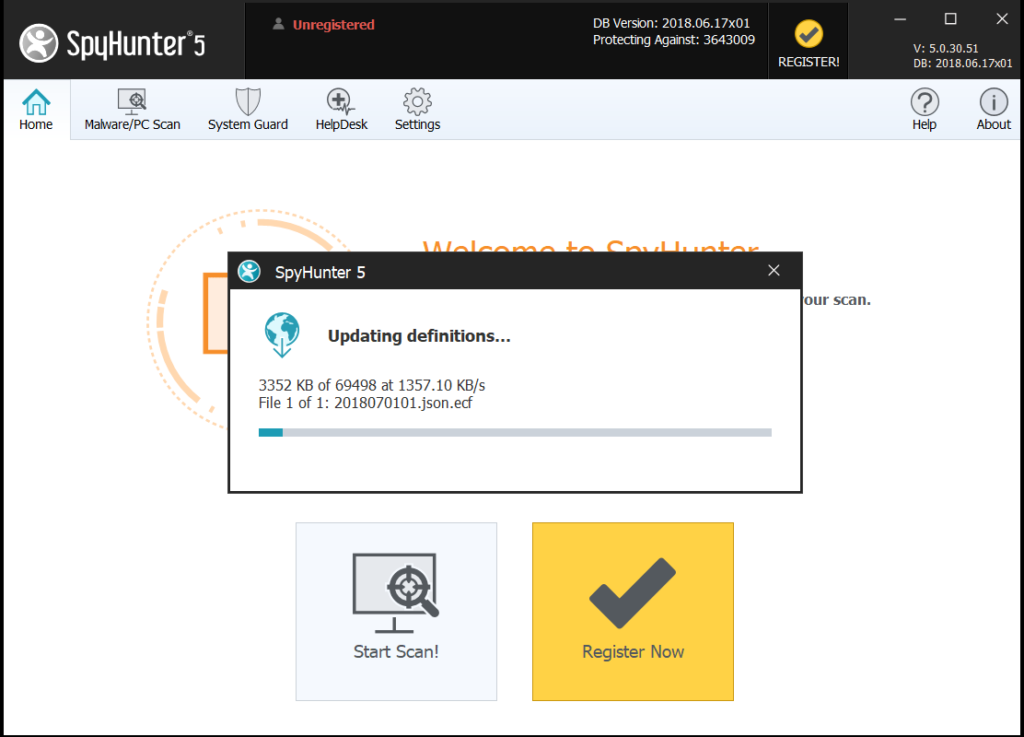
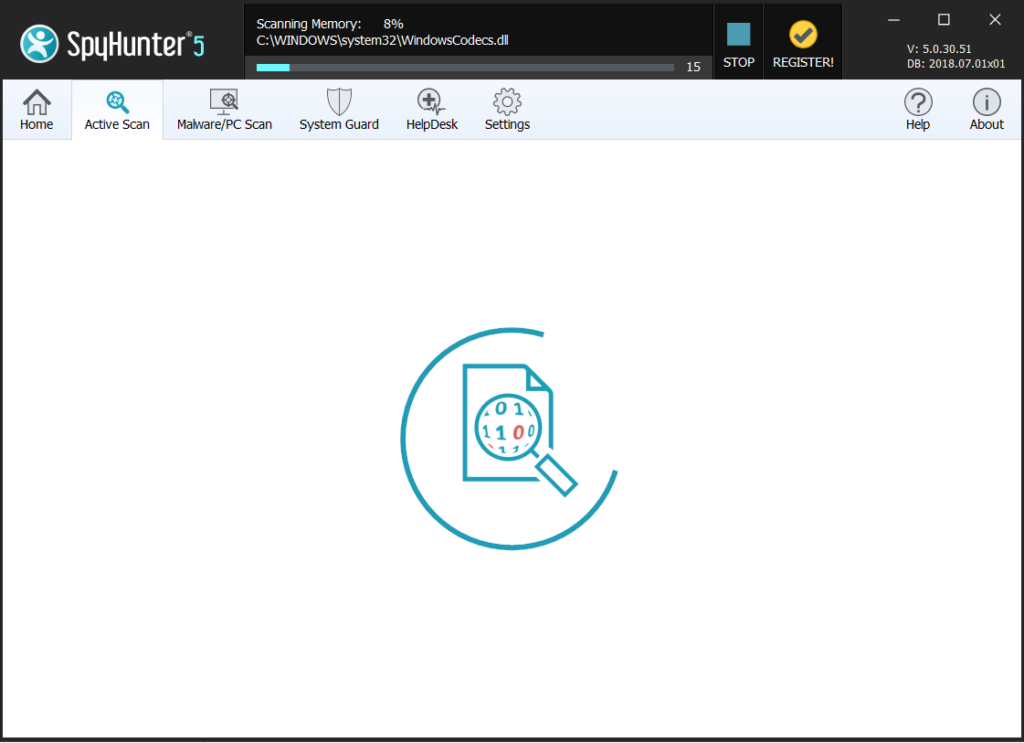
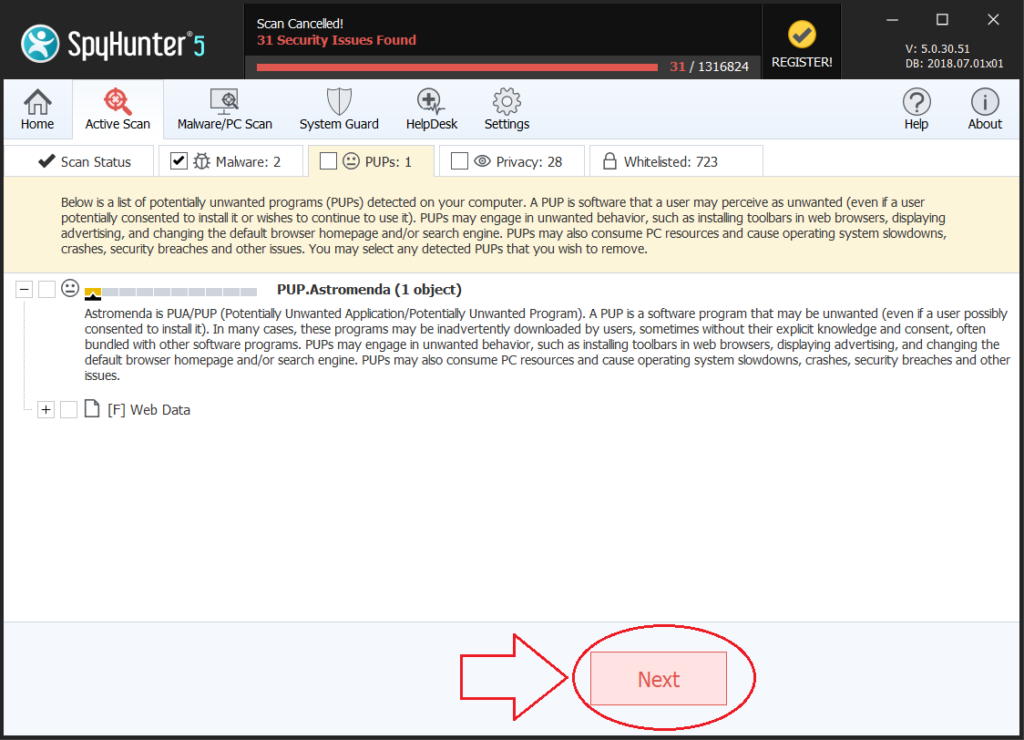
If you are in Safe Mode, boot back into normal mode and follow the steps below
It is advisable to run a free scan before committing to the full version. You should make sure that the malware is detected by SpyHunter first.
Step 5:Recover files encrypted by the Nnuz Ransomware.
Method 1: Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Most of the currently available decryptors for ransomware viruses can be seen if you visit the NoMoreRansom project – a project that is the result of combined efforts of researchers worldwide to create decryption software for all ransomware viruses. Simply go there by clicking on the following LINK and find your ransomware version decrypter and try it, but always remember to do a BACKUP first.
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files: