What is the Llqq ransomware? What are Llqq files? How to open Llqq virus files? How to remove Llqq and restore encrypted data?
A virus that encrypts files adding its own file extension to them and then asks a ransom payoff for the decryption of the files upon contacting the e-mail has been reported to be out in the wild. The virus has been dubbed by malware researchers as the Llqq ransomware and also be what appears to be a part of the notorious Llqq ransom variants. The malware is very specific in it’s methods of encryption, attacking only critical files that are often used. Anyone who was infected by the Llqq ransomware should read this article to learn how to remove Llqq after which decrypt the files for free.
| Threat Name | Llqq |
| Category | Ransomware/Cryptovirus. |
| Main Activity | Infects the computer after which encrypts important documents, photos and other important files and holds them hostage until a ransom is paid. |
| Signs of Presence | Files are encrypted with the Llqq’s own file extension and users are extorted to pay ransom to get the data to work again.. |
| Spread | Via malicious e-mail spam and set of infection tools distributed online. |
| Detection+Removal | DOWNLOAD REMOVAL TOOL FOR Llqq
Note!For Mac users, please use the following instructions. |
Llqq – How Were Your Infected With It
This interesting variant of this malware has the ability to infect user PCs via either a malicious web link or an e-mail attachment that has a malicious character. Not only this, but the malware also has the ability to spread in social media, on suspicious websites and posing as a fake key generator or other fake software posted on download websites.
After you have opened the malicious files belonging to Llqq ransomware, the infection may proceed, depending on how the virus is programmed. This type of malware has a heavily hidden intermediary malicious file that has the ability to be executed without you even noticing it. Once the file has been executed, it begins to immediately either extract the malicious payload files of Llqq or download the payload from a distribution website.
After the payload files have been downloaded, they may be located in one of the below-mentioned directories:
- %Roaming%
- %Common%
- %Startup%
- %AppData%
- %Local%
Then, Llqq allegedly also deletes the shadow copies(Windows Backups) of the infected computer and it may perform that without the you even noticing by executing the vssadmin command in “/quiet” mode, for example:
In addition to this, the Llqq ransomware also has support for widely used file types which if it detects and encrypts immediately. The exact number of file types it may encrypt is huge, but most likely the following often used files are encrypted:
- Videos.
- Microsoft Word Files.
- Microsoft Excel spreadsheets.
- Images.
- Databases.
- Power Point presentations.
After the files that have been enciphered by Llqq ransomware, they can no longer be used. This is because data in those files is replaced with data from the encryption used by it. As a result the virus generates a decryption key that is held by the cyber-crooks who are behind Llqq . The ransomware may perform other activities like leave a ransom notifications asking to contact the e-mail on the files or even change the wallpaper. Either way, you will know, you have been infected.
What to Do If I Am Infected by Llqq Ransomware
In case you have seen your files encrypted with the extension displayed above, malware researchers recommend to seek your own solution and not pay the ransom. Fortunately, for this specific threat, you may just be able to recover your files. This is why it is advisable to first remove the Llqq ransomware from your computer by using the step by step removal instructions below. Be advised that if you want this virus fully erased in a matter of minutes, it is strongly advisable to remove Llqq automatically via an advanced anti-malware program. Such software aims to automatically hunt for and erase absolutely any file in relation to the Llqq from your computer and make it safe and usable again.
Preparation before removal of Llqq:
1.Make sure to backup your files.
2.Make sure to have this instructions page always open so that you can follow the steps.
3.Be patient as the removal may take some time.
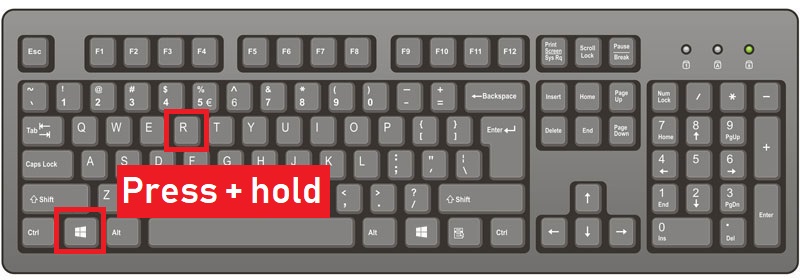
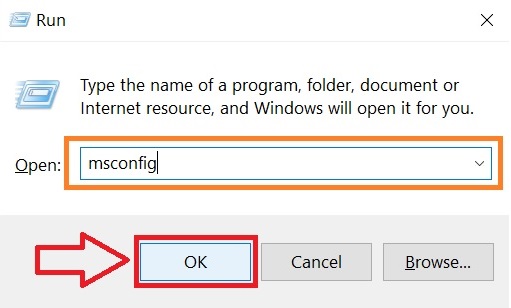
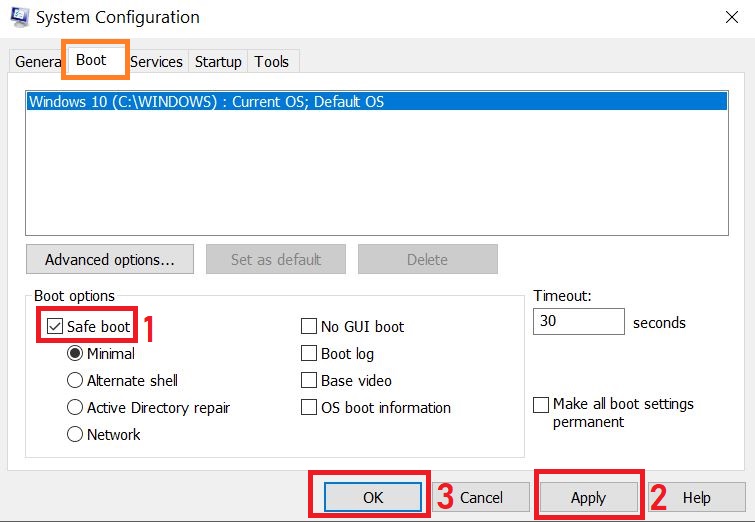
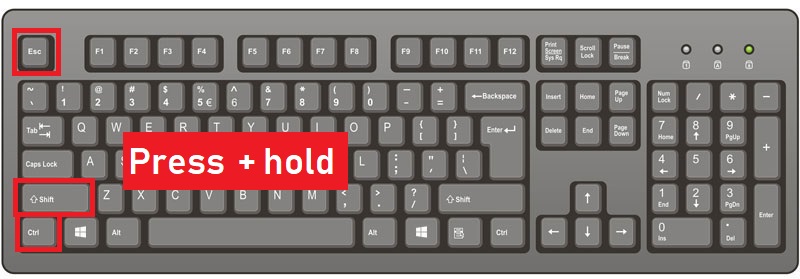
Step 1: Reboot your computer in Safe Mode:
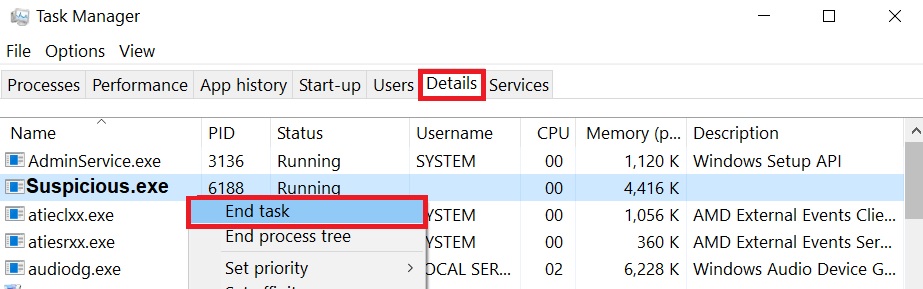
Step 2: Cut out Llqq in Task Manager
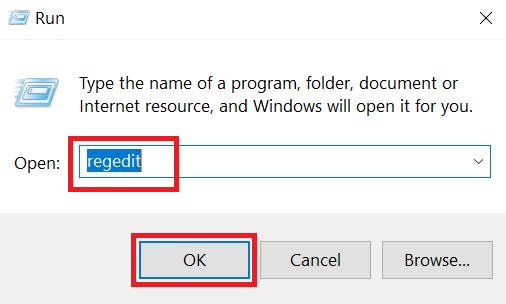
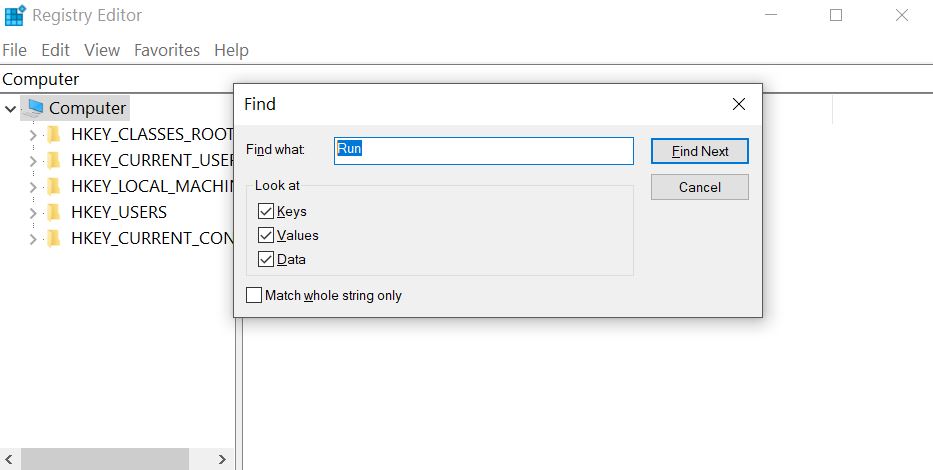
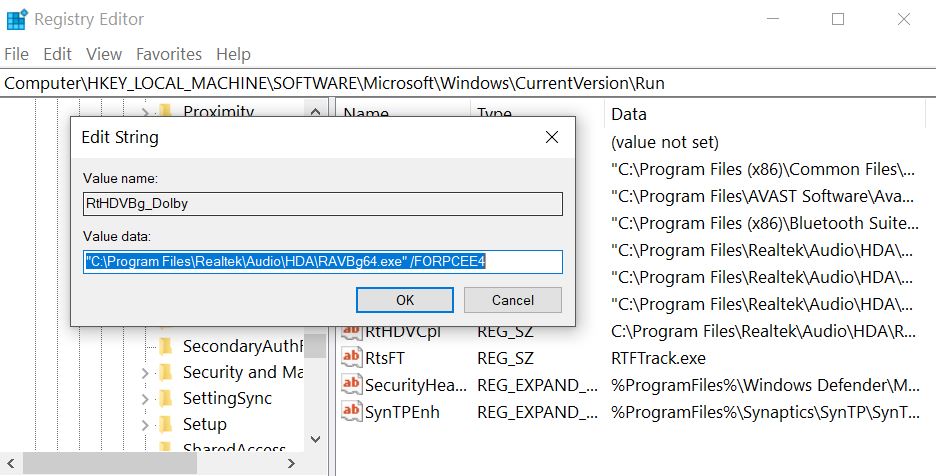
Step 3: Eliminate Llqq‘s Malicious Registries.
For most Windows variants:
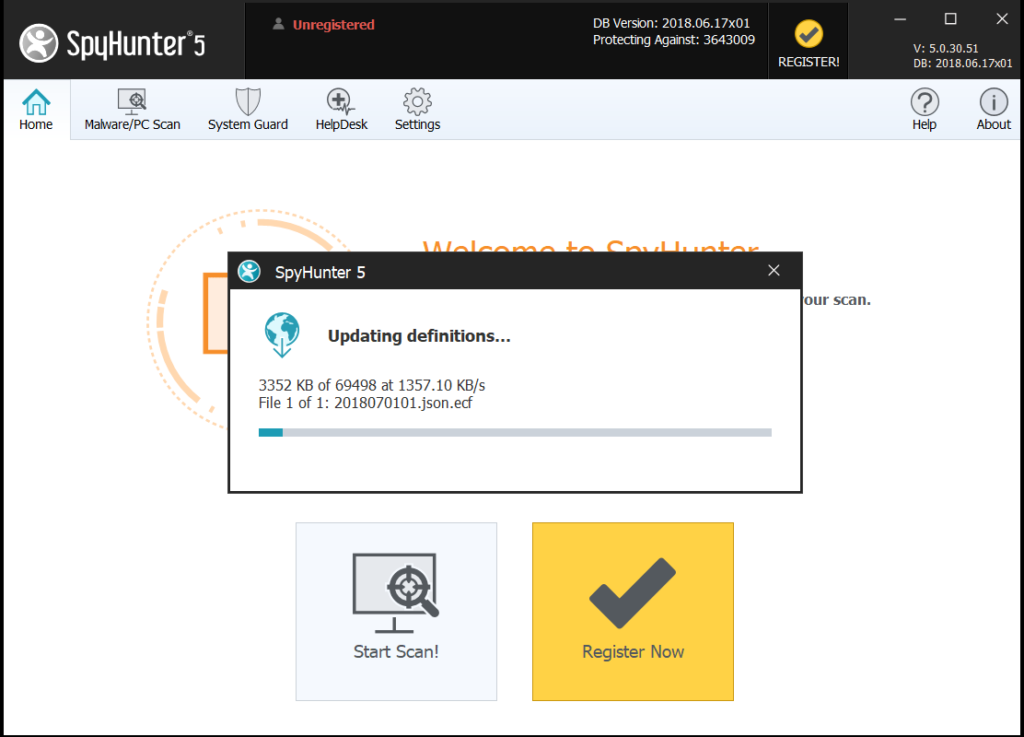
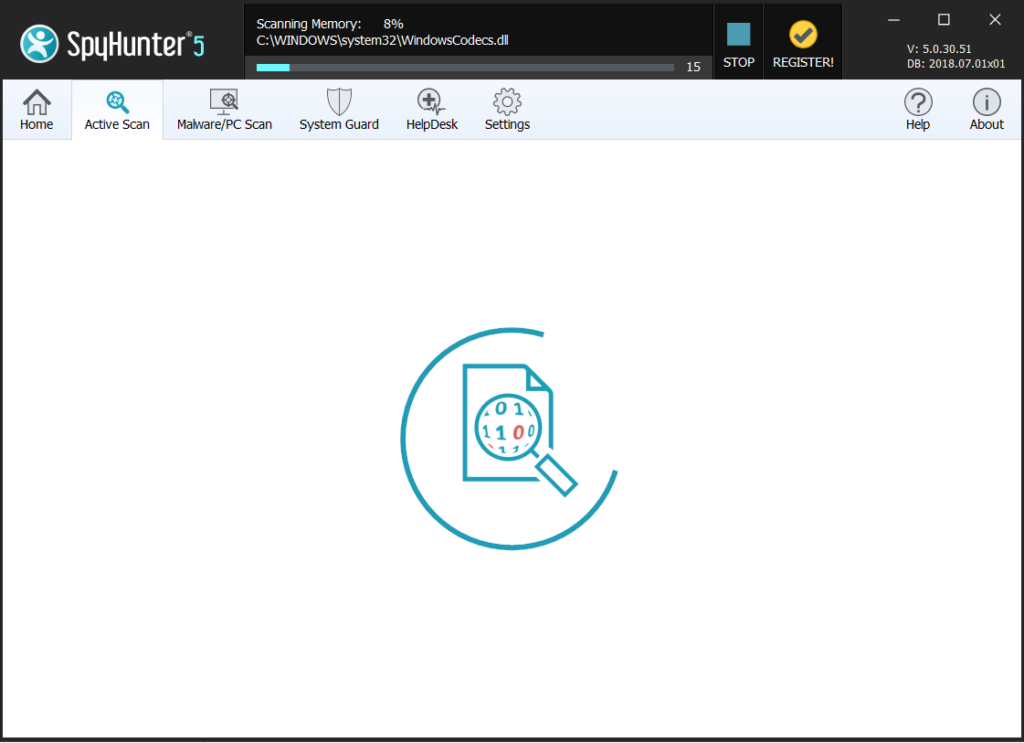
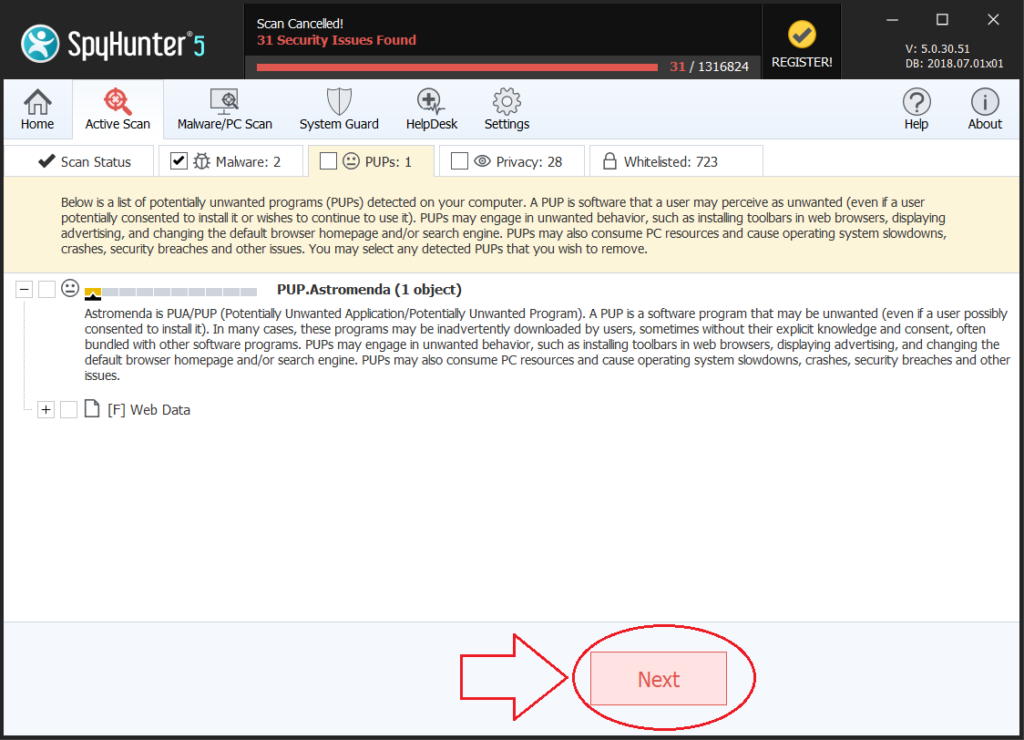
Step 4: Scan for and remove all virus files, related to Llqq and secure your system.
If you are in Safe Mode, boot back into normal mode and follow the steps below
It is advisable to run a free scan before committing to the full version. You should make sure that the malware is detected by SpyHunter first.
Step 5:Recover files encrypted by the Llqq Ransomware.
Method 1: Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Most of the currently available decryptors for ransomware viruses can be seen if you visit the NoMoreRansom project – a project that is the result of combined efforts of researchers worldwide to create decryption software for all ransomware viruses. Simply go there by clicking on the following LINK and find your ransomware version decrypter and try it, but always remember to do a BACKUP first.
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files: