What Is Hog Virus
Hog virus is the name of a ransomware infection, whose main goal is to get users to pay its developers ransom money. This nasty virus aims to get in your computer and encrypt the files you have, adding the Hog file extension to them. The main idea of this is to convince you that you must follow the instructions this virus gives in the DECRYPT-MY-FILES.exe ransom note it drops on your computer after infection. Read this article if you want to learn how you can fully remove Hog virus from your computer and try to restore .hog encrypted files.
| Threat Name | Hog |
| Category | Ransomware/Cryptovirus. |
| Main Activity | Infects the computer after which encrypts important documents and holds them hostage until a ransom is paid. |
| Signs of Presence | Files are encrypted with a custom file extension and users are extorted to pay ransom to get the data to work again.. |
| Spread | Via malicious e-mail spam and set of infection tools. |
| Detection+Removal |
For Windows: DOWNLOAD WINDOWS REMOVAL TOOL FOR Hog For Mac: |
What Will Be the Consequences After Hog Ransomware Enters?
But how does a virus, like Hog find its way on your computer. Well, the answer to that may be in two possible scenarios. One of them is if Hog virus gets sent to you via various different e-mail spam letters. There the infection file may pretend to be a legitimate form of invoice, receipt, ticket or other document. Once downloaded and ran, infection with Hog is immediate.
Another scenario of infection by the Hog virus includes if this nasty threat gets uploaded online, where it may pretend to be a program of some sort, such as:
- Patch.
- Crack.
- Software activator.
- Keygen.
- Update.
- Portable program.
Once Hog virus infects your computer, it may drop several files in the system directories of Windows. These folders are usually:
- %Temp%
- %Local%
- %LocalLow%
- %Roaming%
- %AppData%
The main idea of those files being on your computer is for the virus to be able to successfully run active tasks as administrator. Among the files dropped is the ransom note of Hog ransomware, which has the following message towards victims:
Attention!
Your personal files have been encrypted by the Hog Ransomware.
They have been encrypted using unbreakable AES-256 encryption.
A “.hog” file extension has been appended to the encrypted files.
Please do not remove it, as it is needed to locate and decrypt them.
Attempting to modify the encrypted files can result in irreversible data loss.In order to decrypt your files, you will need to join our Discord server.
Once you hav ejoined, enter your Discord account token in the box below.
Press “Decrypt My Files!” and if you have joined, your files will be decrypted.
Have a nice day!Hide Token
Your token:Discord Server
How do I get my token?
[Decrypt My Files!]
.hog Files
When Hog ransomware is in your computer, its first and most important task is to scan for and encrypt your important data. The malware carefully skips encrypting files in the important folders of Windows while at the same time encrypts all files that you use often. These files are detected based on their file extension (.jpg,.doc, etc.) and are usually the follwoing types:
- Pictures.
- Video files.
- Documents.
- Archives.
- Databases.
- Virtual drive files.
- Virtual image files.
After the virus encrypts files files, it leaves them looking like the image below shows:
What to and Not to Do After You Lose Your Files Due to Hog Ransomware?
To remove Hog virus, we strongly recommend that you follow the removal instructions we have set up beneath this article. They are specifically made to help you detect and get rid of this ransomware step by step. For the most effective removal we urge you to download and run a scan of your computer while using anti-malware software. Cyber-security experts often recommend scanning your computer with such a software, since it will professionally erase all virus files, belonging to this ransomware.
If you want to try and restore .hog files, please see the alternative methods below, if there is no free Hog decryptor available just yet. They may not be a 100% effective, but with their aid, you could restore at least some of your files.
To REMOVE and TRY TO RESTORE files, please follow the instructions underneath
Preparation before removal of Hog:
1.Make sure to backup your files.
2.Make sure to have this instructions page always open so that you can follow the steps.
3.Be patient as the removal may take some time.
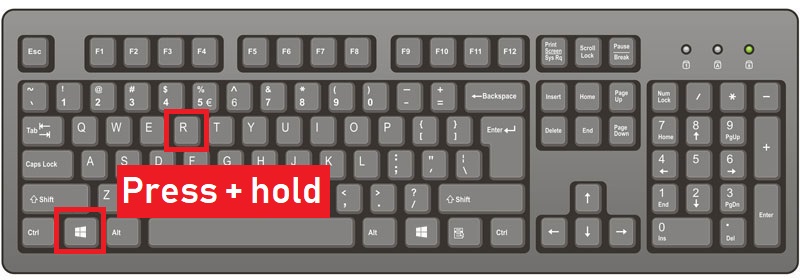
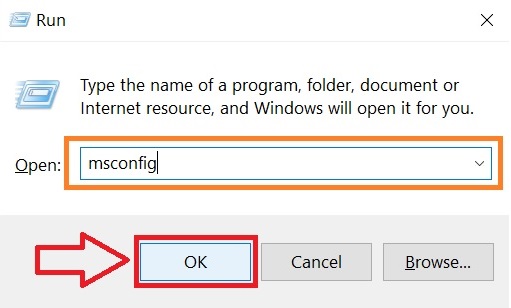
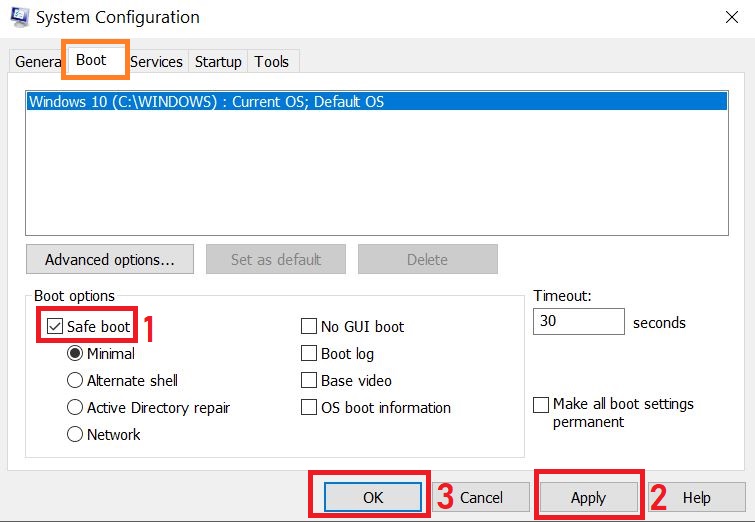
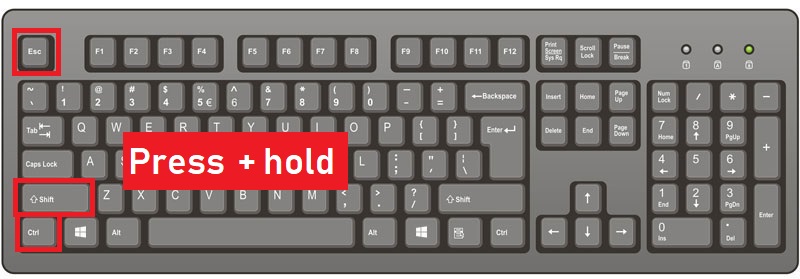
Step 1: Reboot your computer in Safe Mode:
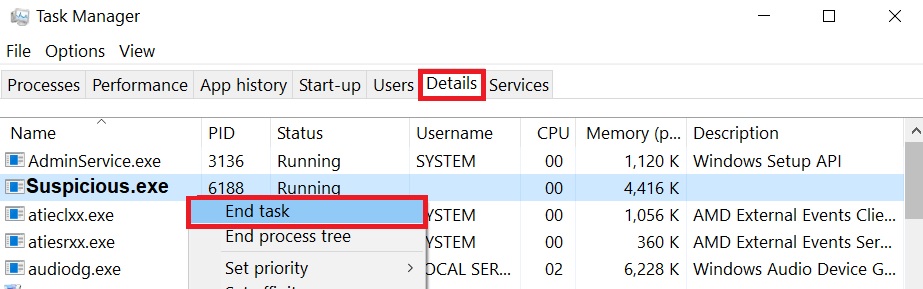
Step 2: Cut out Hog in Task Manager
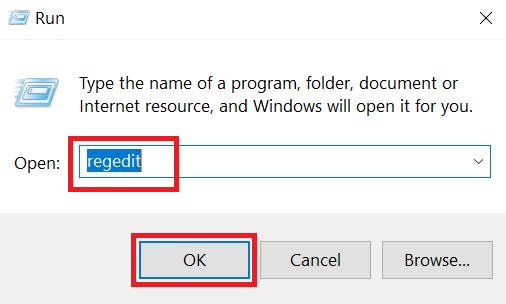
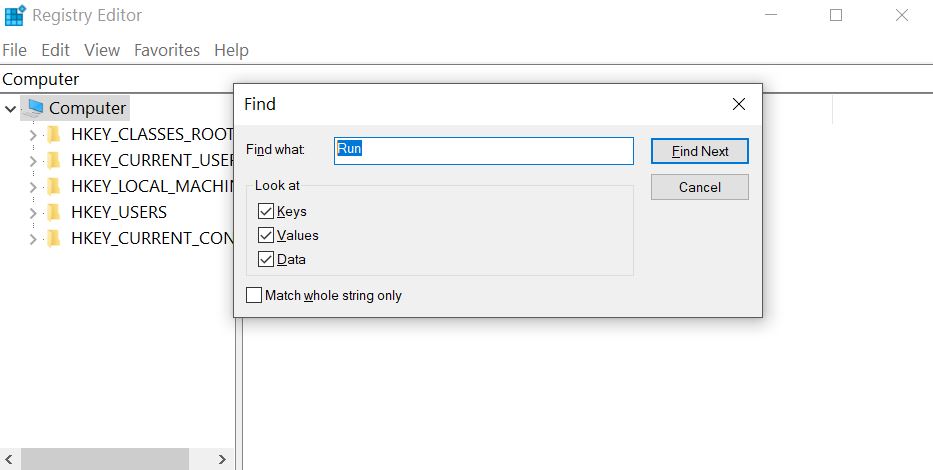
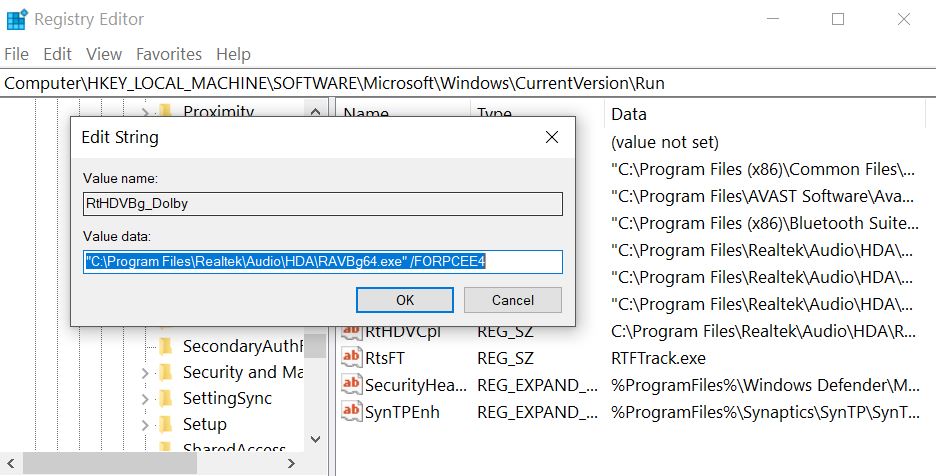
Step 3: Eliminate Hog‘s Malicious Registries.
For most Windows variants:
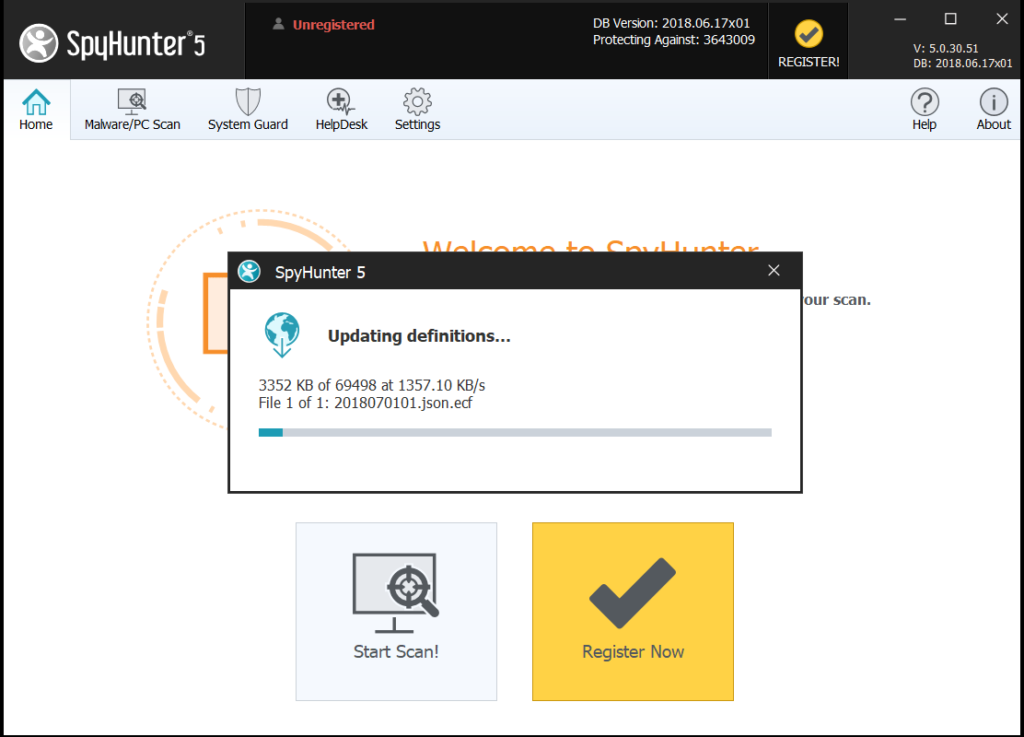
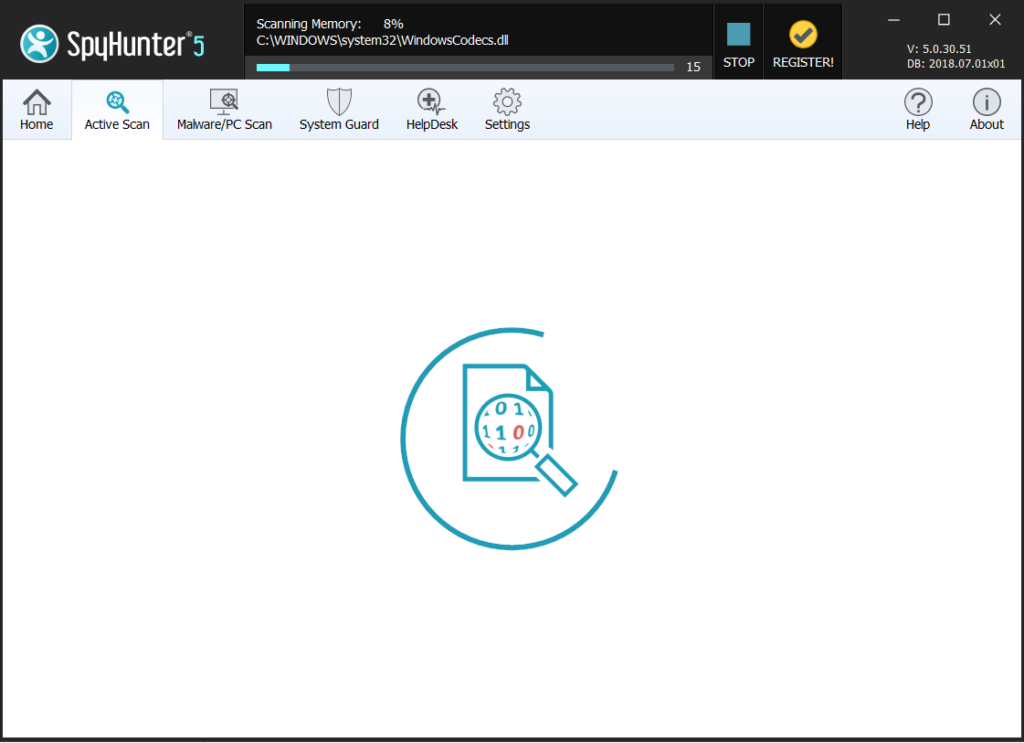
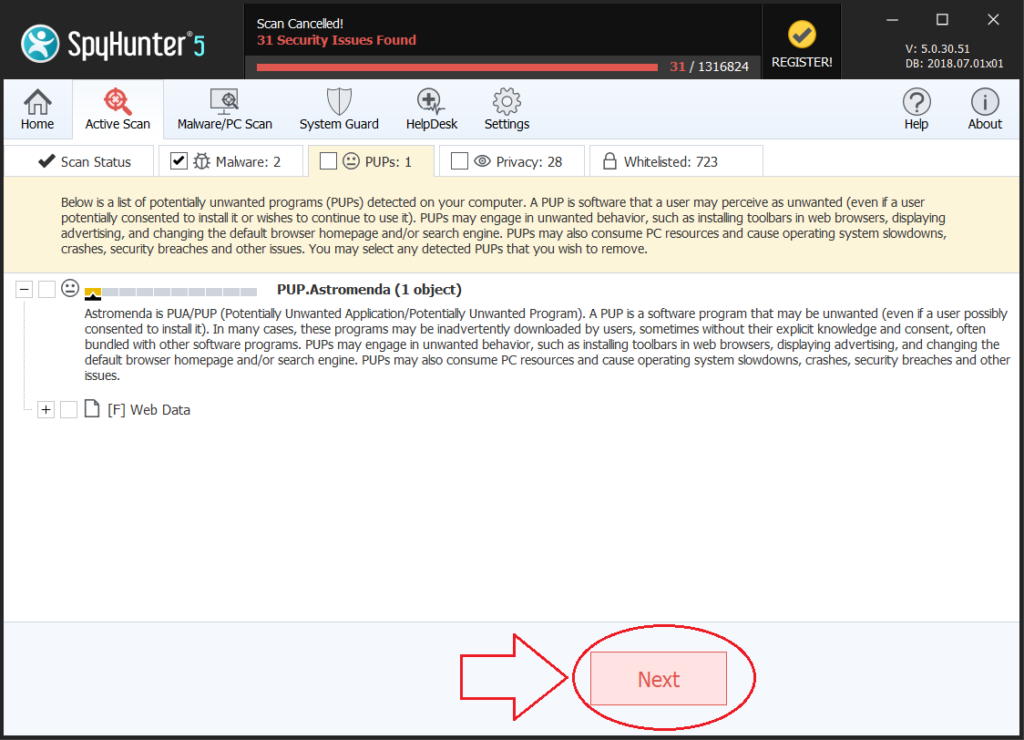
Step 4: Scan for and remove all virus files, related to Hog and secure your system.
If you are in Safe Mode, boot back into normal mode and follow the steps below
It is advisable to run a free scan before committing to the full version. You should make sure that the malware is detected by SpyHunter first.
Step 5:Recover files encrypted by the Hog Ransomware.
Method 1: Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Most of the currently available decryptors for ransomware viruses can be seen if you visit the NoMoreRansom project – a project that is the result of combined efforts of researchers worldwide to create decryption software for all ransomware viruses. Simply go there by clicking on the following LINK and find your ransomware version decrypter and try it, but always remember to do a BACKUP first.
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files: