A virus detected to cause infections via multiple methods has been reported to roam around. .heroset Files Virus ransomware may have been via many ransomware variants using different file extensions, but the latest variant of this virus uses the unique ..heroset Files Virus file extension. The worst part of this is that the virus is as vulgar as it’s file extension suggests. Anyone who has been infected with the .heroset Files Virus virus variant of .heroset Files Virus, should not pay the ransom fee and read the information in this article.
More Information about .heroset Files Virus Ransomware
Upon infection the ransomware may create several files on the computer of the user, such as executable files in .exe file format, files that can be opened with Windows Command Prompt, like .bat or .cmd and files that are system and support files for it’s main executable, like .tmp, .dll or other similar.
The files dropped by the new .heroset Files Virus ransomware may exist in several key folders of Windows, primarily in:
- %SystemDrive%
- %User’s Profile%
- %Temp%
- %System32%
- %LocalRow%
- %Roaming%
- %Local%
After the files are dropped, the new .heroset Files Virus ransomware version may begin to employ encryption on the files of the infected computer. It looks for videos, music, databases, pictures, documents and other files that may be associated with programs that are often used on the computer.
After having encrypted the files of the user, .heroset Files Virus begins to employ a very specific encryption algorithm, called Advanced Encryption Standard which alters segments of the code of the files, making them no longer openable. The files may look like the following:
{Filename}.{File Extension}.heroset
After this, .heroset Files Virus ransmware changes the wallpaper of the user and also drops it’s ransom note to notify the user of what has happened.
Razy ransomware may be also rather specific when it comes to defence as well. The ransomware may shut down in case it is ran on a virtual drive instead of on a real Windows. This is done to prevent researchers from tracking it’s activity and to which servers it communicates.
Which Files May Get Affected by Fuck Society Ransomware?
Fuck Society Ransomware serves as a typical file-encoding Trojan. As soon as it gets access to your machine, this crypto-malware will perform a quick scan to find the paths to all of your personal files. The targeted data includes all MS Office documents, your precious photos and videos, your databases, the program files, etc. Only a few files such as the ones related to the core Windows processes may be spared. Once the operation ends, you will notice a threatening lockdown message on your desktop and the default file extension will become ‘.dll’. The cyber criminals give the victims only 5 days pay the ransom of 2 Bitcoins, or else they threaten to delete forever the decryption key. The purpose of this frightening message is to shock the person and make him act irrationally. The victims often feel as the only solution to the issue is to pay the money. In reality, all specialists unanimously recommend not to follow the instructions of the hackers for several different reasons.
How to Delete .heroset Files Virus Ransomware and Decrypt Your Hard Drives for Free?
The main reasons not to pay the ransom are two. First, you may not receive the promised unlocking key even after doing exactly as the hackers demand. They often scam the victims because the Bitcoin platform doesn’t allow refunds and the people have no way to get their money back. The second reason not to finance cyber criminals is that your money will only motivate them to create more aggressive ransomware like Fuck Society. On the other hand, if their attacks are in vain, they may stop spamming the web with such malicious Trojans. These parasites require quite some efforts to be created professionally and spread efficiently.
Once you decide not to pay the ransom, there are several other ways that may help you decrypt your personal files. You should begin the attempts by removing all traces of the malware. If you fail to delete Fuck Society Ransomware properly, it may decrypt your files once again in the future or spread to other connected devices. The manual removal is not the recommended solution since it requires expert-level knowledge in computers. The most reliable tactic is to use dedicated security software that has added Fuck Society Ransomware to its database. Once the scan finishes, you should try some of the programs for restoration of files or the integrated System Restore feature. If you are lucky enough to have a spare copy of your files on some external device, you can import them back to your computer safely.
Preparation before removal of .heroset Files Virus:
1.Make sure to backup your files.
2.Make sure to have this instructions page always open so that you can follow the steps.
3.Be patient as the removal may take some time.
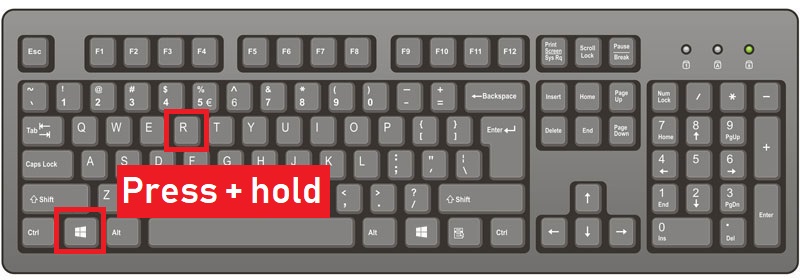
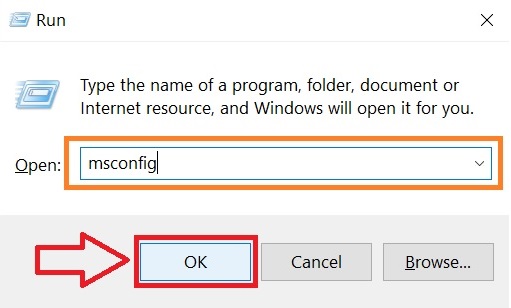
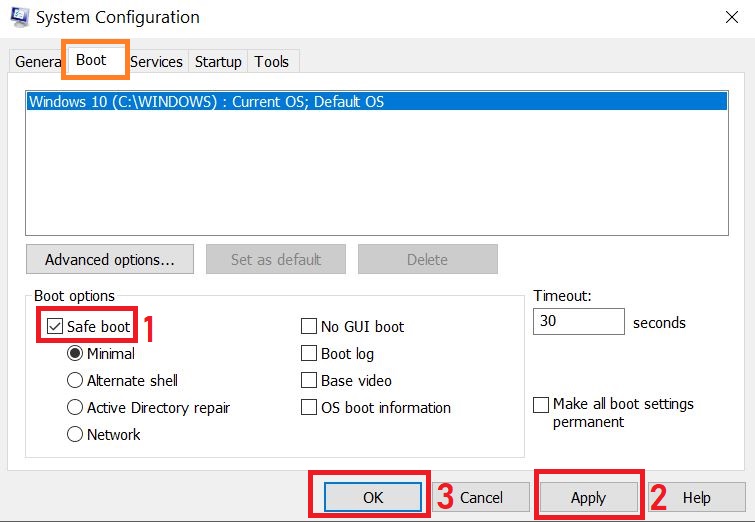
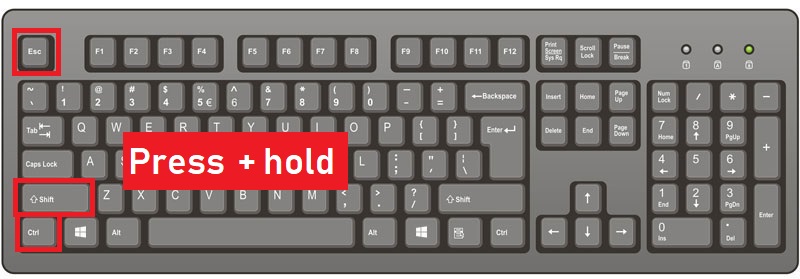
Step 1: Reboot your computer in Safe Mode:
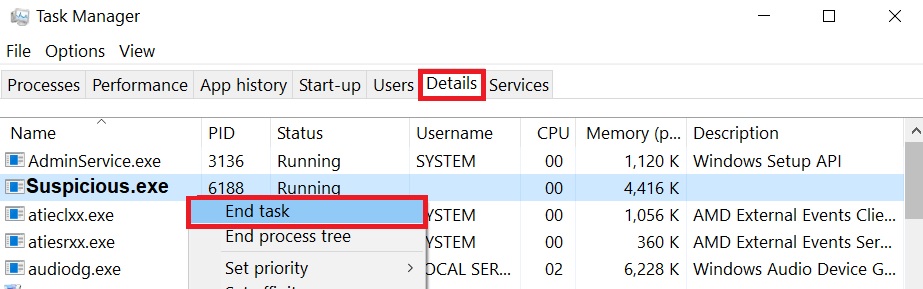
Step 2: Cut out .heroset Files Virus in Task Manager
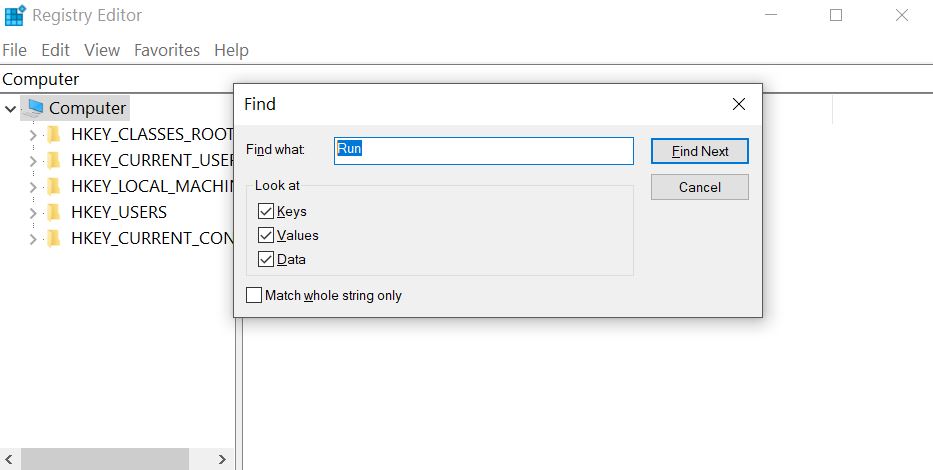
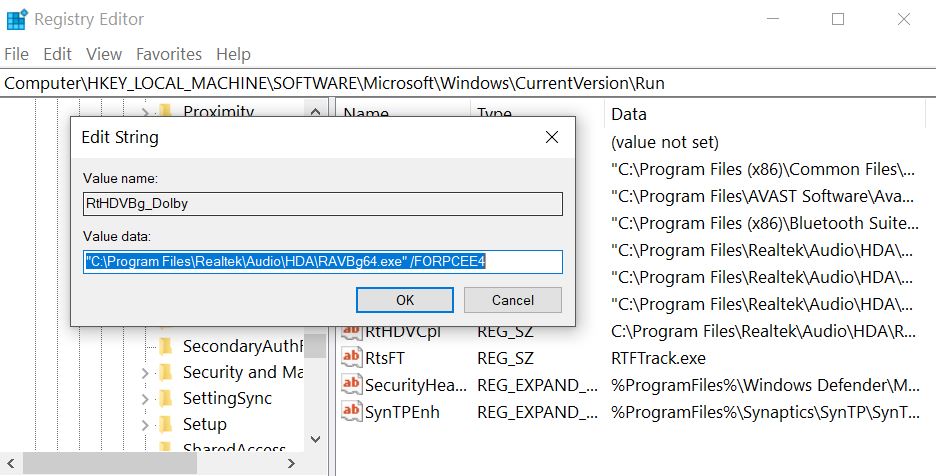
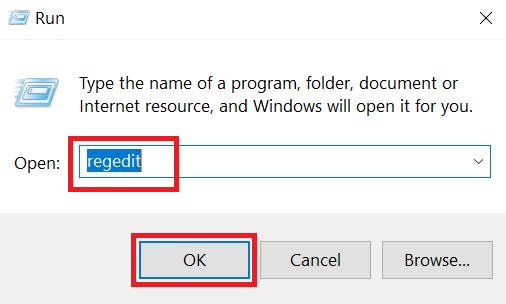
Step 3: Eliminate .heroset Files Virus‘s Malicious Registries.
For most Windows variants:
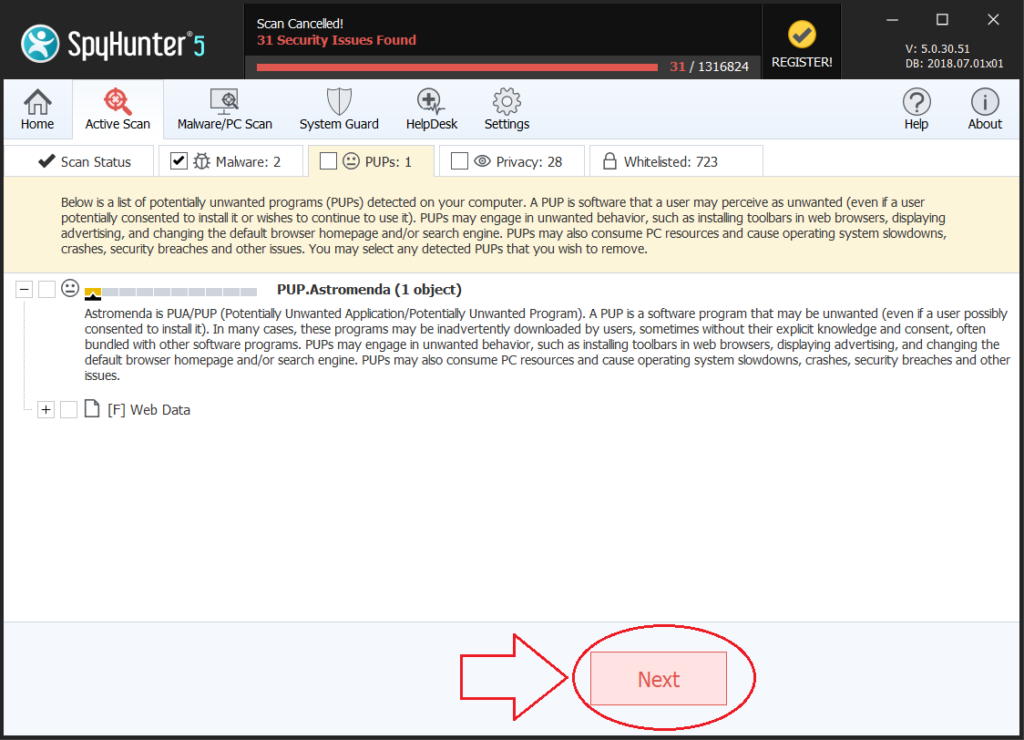
Step 4: Scan for and remove all virus files, related to .heroset Files Virus and secure your system.
If you are in Safe Mode, boot back into normal mode and follow the steps below
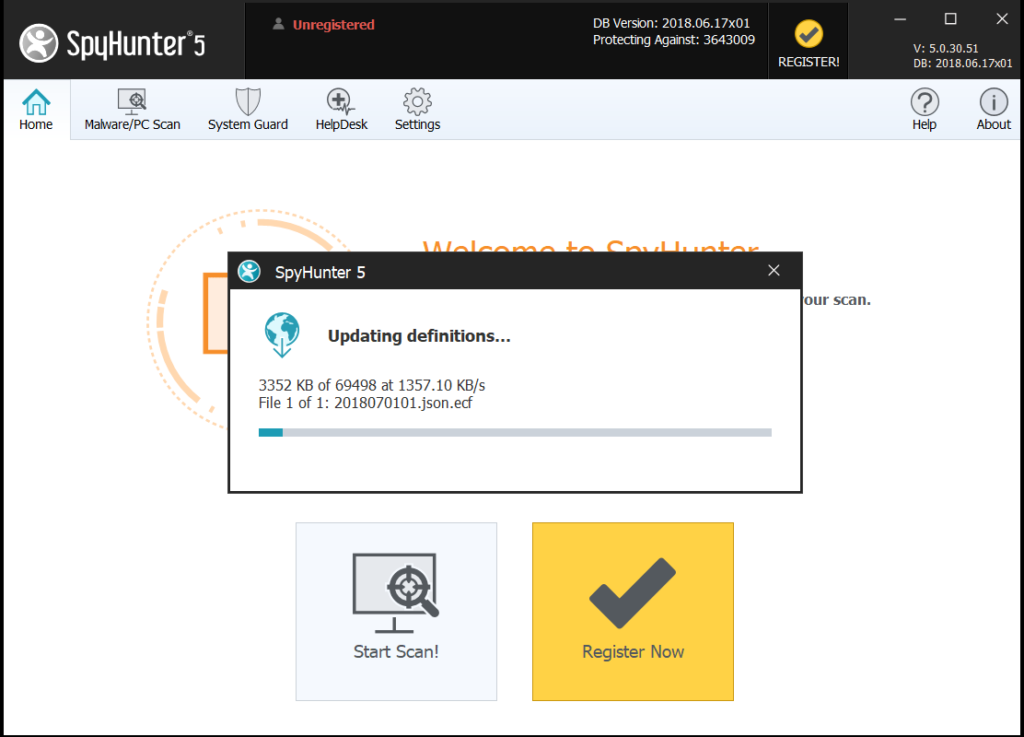
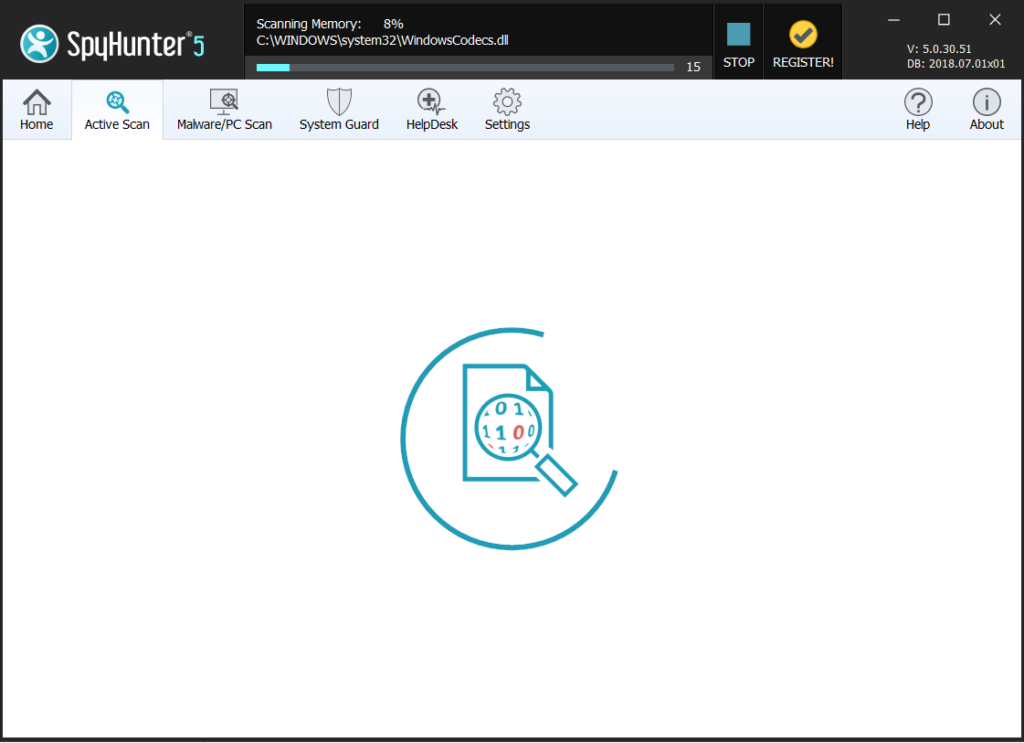
It is advisable to run a free scan before committing to the full version. You should make sure that the malware is detected by SpyHunter first.
Step 5:Recover files encrypted by the .heroset Files Virus Ransomware.
Method 1: Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Most of the currently available decryptors for ransomware viruses can be seen if you visit the NoMoreRansom project – a project that is the result of combined efforts of researchers worldwide to create decryption software for all ransomware viruses. Simply go there by clicking on the following LINK and find your ransomware version decrypter and try it, but always remember to do a BACKUP first.
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files:

sir datab recovery nhi ho rhi hai