Ce billet de blog a été fait dans le but de vous montrer ce qui est le virus .muslatRansomware et expliquer comment vous pouvez supprimer ce ransomware de votre ordinateur et comment vous pouvez récupérer des fichiers, crypté par cette infection, sans avoir à payer la rançon.
Le virus .muslat Ransomware, qui est considéré comme une variante d'Hermès ransomware a été signalé pour infecter les ordinateurs dans une vague massive d'e-mails de spam. L'objectif principal du virus ransomware est d'infecter les ordinateurs tout en restant non détecté. Le virus de ransomware alors les fichiers encrypte sur les ordinateurs qui ont été infectés par elle afin qu'elle puisse alors déposer est de rançon, qui vise à convaincre les victimes en leur faisant payer une rançon pour obtenir les fichiers de travailler à nouveau. Si votre ordinateur a été infecté par .muslat Ransomware, nous vous recommandons de lire cet article car il vous aidera à supprimer ce virus ransomware de votre ordinateur de façon efficace et vous montrer comment vous pouvez essayer de récupérer des fichiers, crypté par cette ransomware.
| Nom de la menace | .muslat Fichiers Ransomware |
| Catégorie | Ransomware / Cryptovirus. |
| Activité principale | Infecte l'ordinateur après quoi les documents importants et encrypte les tient en otage jusqu'à ce qu'une rançon soit payée. |
| Les signes de présence | Les fichiers sont chiffrés avec l'extension .muslat et via le cryptage AES 256 bits et les utilisateurs sont extorqué à payer une rançon pour obtenir les données de travailler à nouveau. |
| Propager | Via e-mail spam malveillant et un ensemble d'outils d'infection. |
| Détection + suppression | OUTIL DE RETRAIT POUR TÉLÉCHARGER .muslat Fichiers Ransomware |
| Récupération de fichier | Télécharger le logiciel de récupération de données, pour voir combien de fichiers cryptés par .muslat fichiers Ransomware ransomware vous serez en mesure de récupérer. |
Le virus .muslat fichiers Ransomware a été repéré à l'aide du son extension de fichier. Le virus .muslat fichiers Ransomware communique également via TOR à travers lequel il envoie un décrypteur après la rançon a été payée. Si vous êtes victime du nouveau virus .muslat fichiers Ransomware nous vous conseillons de lire cet article et d'apprendre comment supprimer les fichiers de virus et essayer de décoder les objets cryptés.
.Virus muslat fichiers Ransomware - Qu'est-ce que fait-elle
Être une variante de la famille ransomware, qui existe dans un grand nombre de familles de virus, les fichiers .muslat Ransomware ransomware a été signalé à déposer un ou plusieurs fichiers exécutables dans le %Données d'application% répertoire windows.
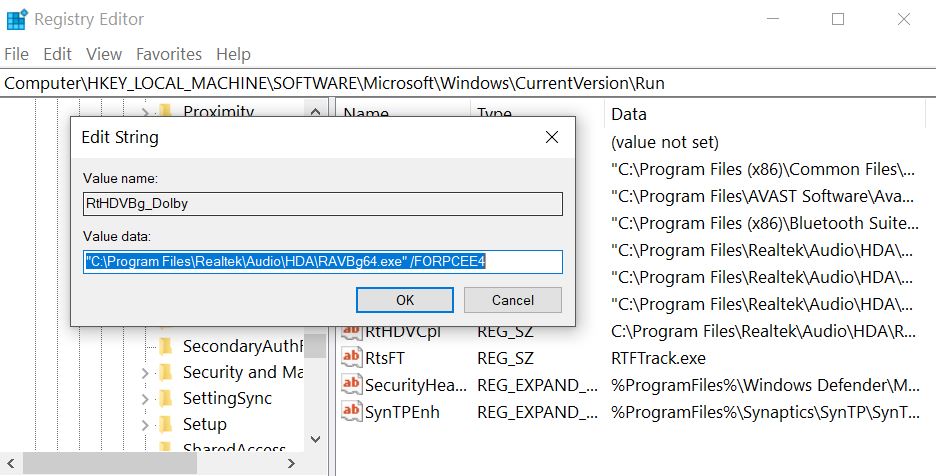
Après cela, le virus .muslat fichiers Ransomware peut modifier les entrées de registre Windows, plus particulièrement la sous-clé Shell avec l'emplacement suivant:
- HKLM / Software / Microsoft / Windows NT / CurrentVersion / Winlogon / Shell
Puis, le .muslat Fichiers Ransomware virus peut également modifier la clé de Registre Run pour exécuter le fichier exécutable(avec) dans le répertoire% AppData%. La clé est le chemin suivant:
- HKLM / Software / Microsoft / Windows / CurrentVersion / Run /
Cela peut entraîner le démarrage de virus de fichier à côté du processus de démarrage Windows.
.muslat Fichiers Ransomware gouttes également un fichier de rançon avec un message de rançon et place un emplacement facile à trouver. Puis, le .muslat Fichiers Ransomware le virus peut attaquer des fichiers avec les types de fichiers suivants pour les chiffrer:
- Vidéos.
- Images.
- documents.
- Fichiers audio.
- Archives.
Après .muslat fichiers Ransomware les fichiers encrypte, le virus quitte les fichiers ne peuvent plus être ouverts et probablement un fichier joint personnalisé pour les extension venant.
.muslat fichiers Ransomware Ransomware - Comment ai-je Infected
Le processus d'infection .muslat Fichiers Ransomware est menée principalement par des e-mails de spam qui ont des messages trompeurs incorporés dans les. Ces messages peuvent prétendre être envoyés de services tels que PayPal, UPS, FedEx et d'autres. Ils peuvent contenir des pièces jointes qui font semblant d'être des factures et d'autres types de faux de fichiers. D'autres techniques d'ingénierie sociale comprennent:
- faux boutons et des images comme si les e-mails sont envoyés à partir d'un site de médias sociaux, comme LinkedIn.
- Liens PayPal Fraudulent.
- Liens vers et Google Drive e-mails faux qui ressemblent les mêmes que si elles sont envoyées à partir de Google.
D'autres outils d'infection peuvent également inclure l'utilisation des sites torrent et d'autres sites tiers pour télécharger des mises à jour fausses, installateurs faux, ainsi que d'autres executables frauduleux.
Quels fichiers peut obtenir touchés par .muslat fichiers Ransomware Ransomware?
.muslat fichiers Ransomware Ransomware sert de fichier typique codant pour cheval de Troie. Dès qu'il a accès à votre machine, cette cryptomalware effectuera une analyse rapide pour trouver les chemins d'accès à tous vos fichiers personnels. Les données ciblées comprend tous les documents MS Office, vos précieuses photos et vidéos, vos bases de données, les fichiers de programme, etc. Seuls quelques fichiers tels que ceux liés au processus principaux de Windows peuvent être épargnées. Une fois que les extrémités de fonctionnement, vous remarquerez un message de verrouillage menaçant sur votre bureau et l'extension de fichier par défaut deviendra « .dll ». Les cyber-criminels donnent aux victimes que plusieurs jours paient la rançon de Bitcoins, ou bien ils menacent de supprimer définitivement la clé de déchiffrement. Le but de ce message effrayant est de choquer la personne et lui faire agir irrationnellement. Les victimes se sentent souvent comme la seule solution à la question est de payer l'argent. En réalité, tous les spécialistes recommandent à l'unanimité de ne pas suivre les instructions des pirates informatiques pour plusieurs raisons différentes.Comment se protéger de .muslat fichiers Ransomware Ransomware?
Cette ransomware peut causer des dommages énormes et souvent irréversibles aux machines affectées. Heureusement, vous pouvez empêcher l'infection aussi longtemps que vous êtes vigilant lors de vos sessions en ligne. Ce cheval de Troie ne sait pas utiliser des méthodes uniques pour infiltrer les défenses de votre ordinateur. La cause la plus probable de .muslat fichiers Ransomware Ransomware pour entrer est par e-mails de spam. Vous pouvez recevoir un message avec un contenu choquant, vous encourager à soit cliquer sur un lien malveillant ou télécharger un fichier corrompu. Les pirates disposent d'un arsenal d'outils pour vous manipuler en faisant. Par exemple, ils peuvent prétendre représenter une banque internationale ou d'une compagnie maritime populaire. S'ils vous traitent sans mentionner votre nom, l'e-mail est probablement une arnaque et vous devriez l'ignorer. Malheureusement, si vous suffit de cliquer ou télécharger le fichier infecté, votre action sera probablement suffisant pour activer les codes nocifs des fichiers .muslat Ransomware Ransomware. Dans ce cas, seule une solution de sécurité crédible peut être en mesure de prévenir les dommages à venir.
Comment supprimer des fichiers .muslat Ransomware Ransomware et Décrypter vos fichiers gratuitement?
Les principales raisons de ne pas payer la rançon sont deux. Première, vous ne pouvez pas recevoir la clé de déverrouillage promis même après avoir fait exactement comme la demande des pirates. Souvent, ils arnaque les victimes parce que la plate-forme Bitcoin ne permet pas le remboursement et le peuple n'a aucun moyen de récupérer leur argent. La deuxième raison de ne pas financer les cyber-criminels est que votre argent ne les inciter à créer ransomware plus agressif comme .muslat fichiers Ransomware. D'autre part, si leurs attaques sont en vain, ils peuvent cesser de spamming le web avec ces chevaux de Troie malveillants. Ces parasites ont besoin tout à fait des efforts pour créer de façon professionnelle et de transmission interhumaine efficace.
Une fois que vous décidez de ne pas payer la rançon, il existe plusieurs autres façons qui peuvent vous aider à décrypter vos fichiers personnels. Vous devriez commencer les tentatives en supprimant toute trace du malware. Si vous ne parvenez pas à supprimer .muslat fichiers Ransomware Ransomware correctement, il peut décrypter à nouveau vos fichiers dans l'avenir ou se propager à d'autres appareils connectés. La suppression manuelle n'est pas la solution recommandée car elle nécessite des connaissances de niveau expert en informatique. La tactique la plus fiable est d'utiliser un logiciel de sécurité dédié qui a ajouté F.muslat fichiers Ransomware Ransomware à sa base de données. Une fois que l'analyse se termine, vous devriez essayer quelques-uns des programmes de restauration des fichiers ou le système intégré fonctionnalité de restauration. Si vous êtes assez chanceux d'avoir une copie de secours de vos fichiers sur un périphérique externe, vous pouvez les importer sur votre ordinateur en toute sécurité.
Instructions pour la suppression de fichiers .muslat Ransomware
Si vous voulez supprimer des fichiers .muslat Ransomware, nous vous recommandons fortement de première sauvegarde vos données, quelque chose juste au cas où va mal. Puis, vous pouvez suivre les instructions de suppression manuelle ou automatique ci-dessous, selon le type de mesures que vous convient plus. Si vous manque l'expérience et la confiance que vous allez supprimer manuellement .muslat fichiers Ransomware, alors vous devriez faire ce que la plupart des experts et de vous faire gagner du temps en téléchargeant et en exécutant un scan avec un logiciel anti-malware avancée. De tels programmes sont créés pour identifier rapidement et éliminer les menaces et les programmes ayant un comportement intrusif, comme .muslat fichiers Ransomware, plus ils visent également à assurer que votre système est protégé contre les intrusions futures et.
Préparation avant le retrait des fichiers .muslat Ransomware:
1.Assurez-vous de sauvegarder vos fichiers.
2.Assurez-vous d'avoir cette page d'instructions toujours ouverte afin que vous puissiez suivre les étapes.
3.Soyez patient que le retrait peut prendre un certain temps.
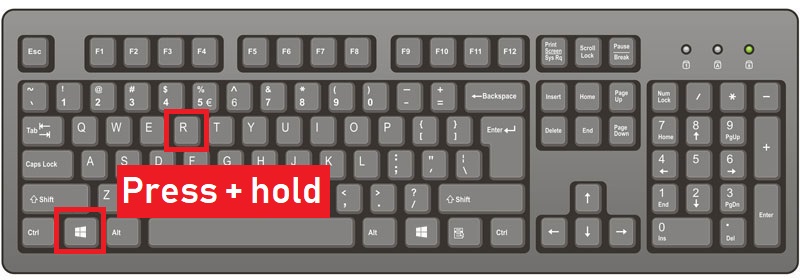
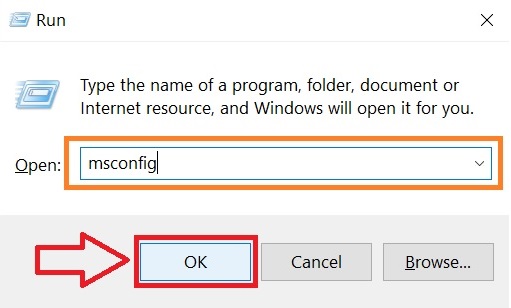
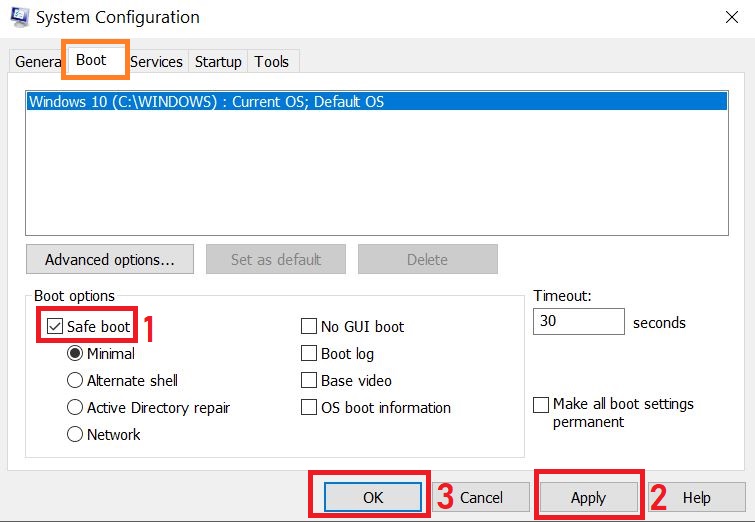
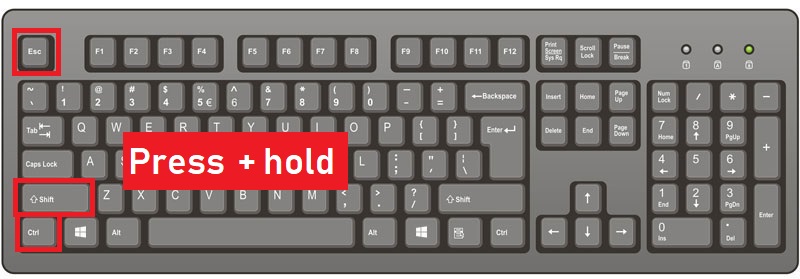
Étape 1: Redémarrez votre ordinateur en mode sans échec:
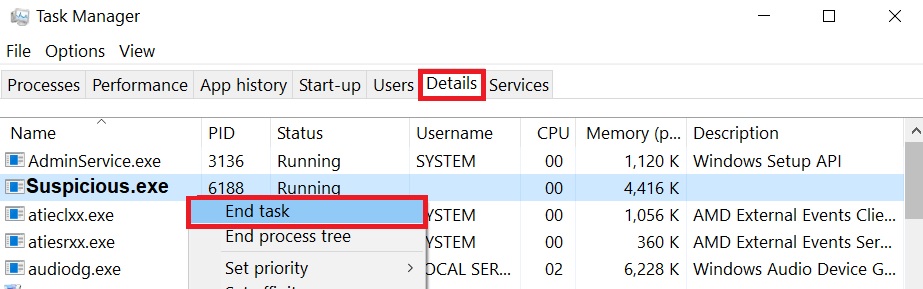
Étape 2: Découpez les fichiers .muslat Ransomware dans le Gestionnaire des tâches
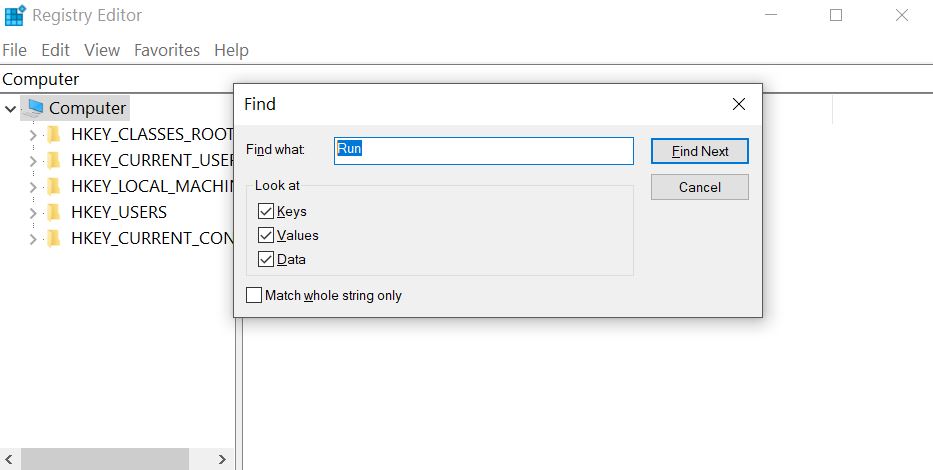
Étape 3: Éliminer .muslat Registries malicieuses fichiers Ransomware.
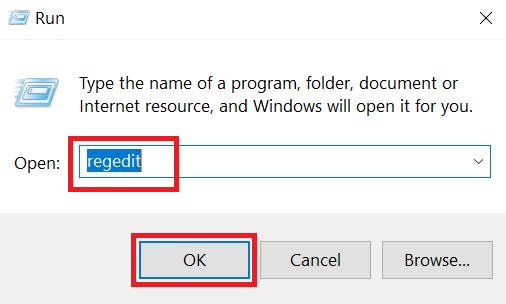
Pour la plupart des variantes de Windows:
Étape 4: Rechercher et supprimer tous les fichiers de virus, liés à .muslat fichiers Ransomware et sécuriser votre système.
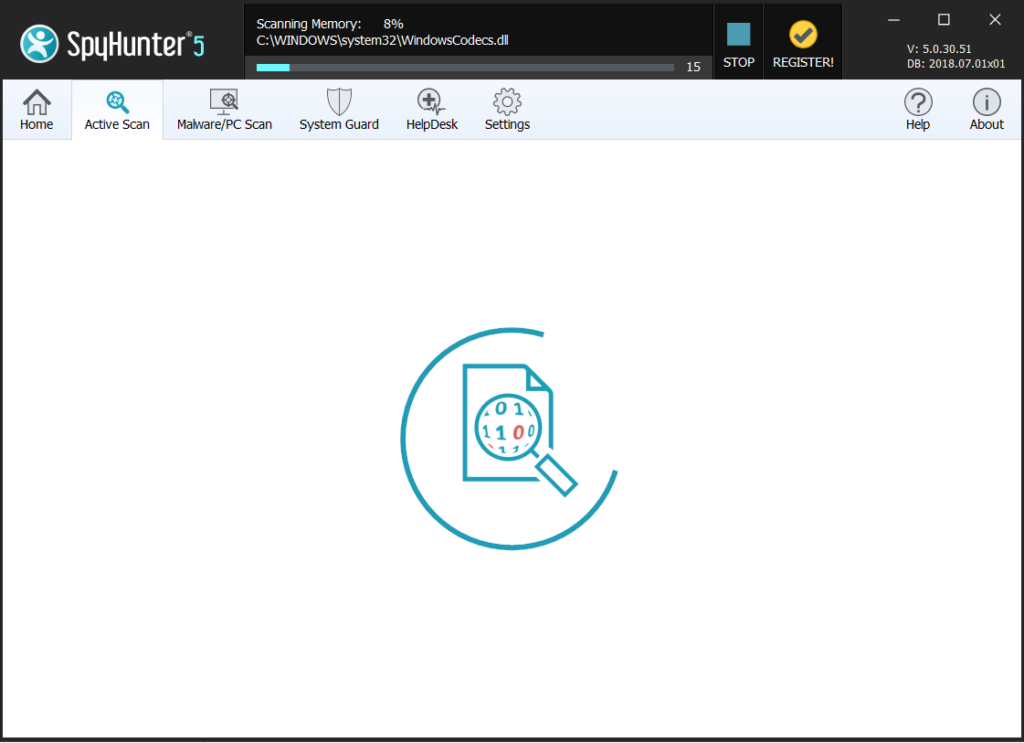
Si vous êtes mode sans échec, démarrer en mode normal et suivez les étapes ci-dessous
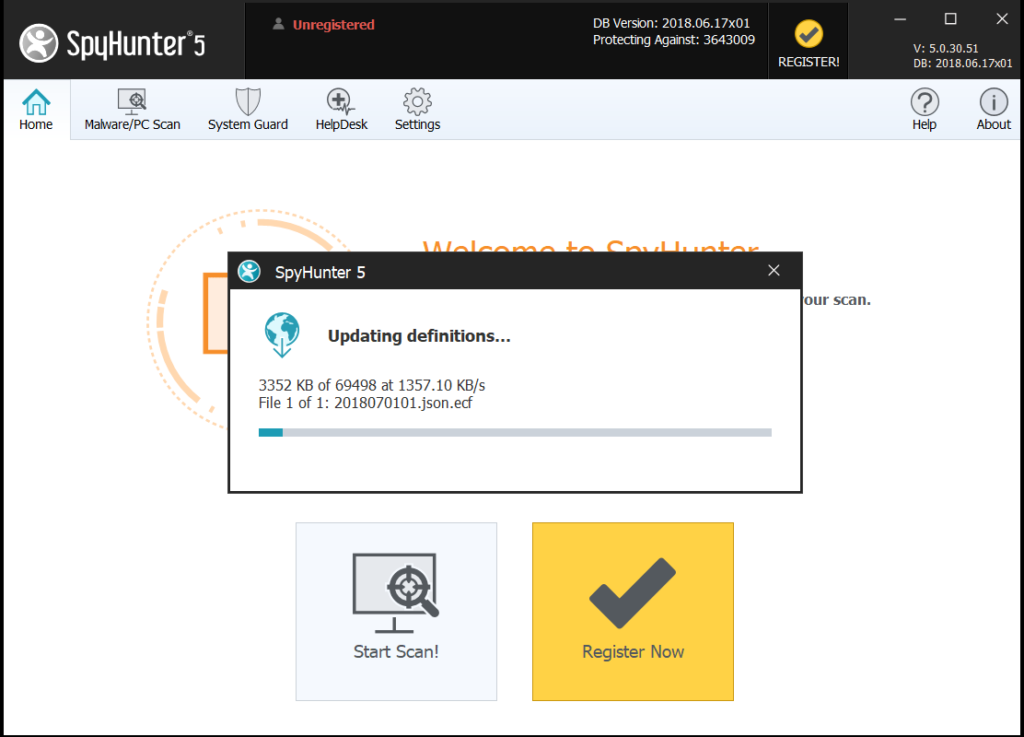
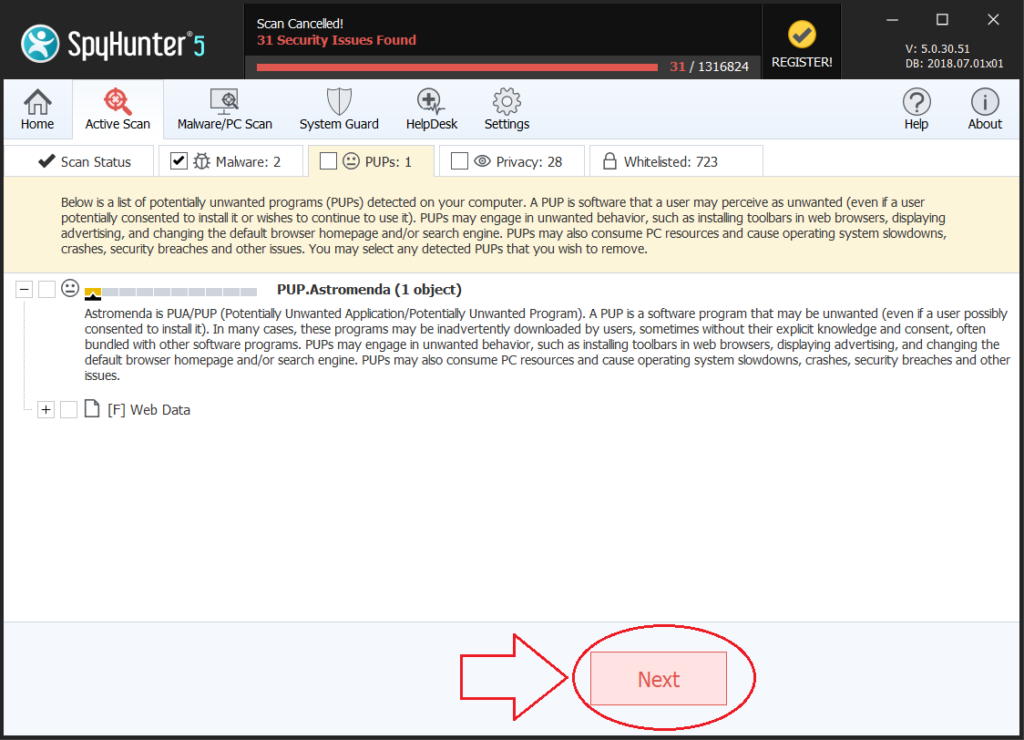
Il est conseillé de lancer un balayage gratuit avant de vous engager à la version complète. Vous devez vous assurer que le malware est détecté par SpyHunter premier.
Étape 5:Récupérer des fichiers cryptés par le .muslat Fichiers Ransomware Ransomware.
Méthode 1: En utilisant l'Explorateur Ombre. Si vous avez activé l'historique du fichier sur votre machine Windows une chose que vous pouvez faire est d'utiliser l'ombre Explorer pour récupérer vos fichiers. Malheureusement, certains virus peuvent ransomware supprimer les copies de volume d'ombre avec une commande administrative pour vous empêcher de faire tout cela.
Méthode 2: Si vous essayez de décrypter vos fichiers à l'aide des outils de décryptage tiers. Il existe de nombreux fournisseurs d'antivirus qui ont déchiffré plusieurs ransomware virus les deux dernières années et affiché decryptor pour eux. Les chances sont si votre virus ransomware utilise le même code de cryptage utilisé par un virus déchiffrable, vous pouvez obtenir les fichiers de retour. Cependant, c'est pas non plus une garantie, de sorte que vous pourriez vouloir essayer cette méthode avec des copies des fichiers cryptés originaux, parce que si un programme tiers falsifie leur structure cryptée, ils peuvent être endommagés de façon permanente. La plupart des virus pour ransomware decryptor actuellement disponibles peut être vu si vous visitez le projet NoMoreRansom – un projet qui est le fruit des efforts conjugués des chercheurs du monde entier pour créer des logiciels de décryptage pour tous les virus ransomware. Il suffit d'aller là-bas en cliquant sur les points suivants LIEN et trouver votre version ransomware decrypter et essayer, mais rappelez-vous toujours de faire un premier BACKUP.
Méthode 3: L'utilisation d'outils de récupération de données. Cette méthode est suggérée par plusieurs experts dans le domaine. Il peut être utilisé pour analyser votre secteurs de disque dur et donc brouiller les fichiers cryptés à nouveau comme ils ont été supprimés. La plupart des virus de ransomware supprimer généralement un fichier et créer une copie cryptée afin d'éviter de tels programmes pour restaurer les fichiers, mais tous ne sont pas ce sophistiqué. Ainsi, vous pouvez avoir une chance de restaurer certains de vos fichiers avec cette méthode. Voici plusieurs programmes de récupération de données que vous pouvez essayer de restaurer au moins certains de vos fichiers: