 En blog indlæg, oprettet for at hjælpe dig, hvis dine filer er blevet krypteret ved Dharma ransomware bruger .skrive filtypen ved at vise, hvordan du fjerner den fra din computer og hvordan du kan gendanne disse filer.
En blog indlæg, oprettet for at hjælpe dig, hvis dine filer er blevet krypteret ved Dharma ransomware bruger .skrive filtypen ved at vise, hvordan du fjerner den fra din computer og hvordan du kan gendanne disse filer.
Ny variant af den berygtede Dharma ransomware virus er blevet frigivet, efter den ældre .java fil forlængelse variant af virussen. Den malware har den ene og eneste formål at kryptere filerne på din inficerede computer og tilføje den .write filsuffiks til dem. Efter dette, Dharma er .write variant falder bag en løsesum notat med instruktioner til ofrene om, hvordan man betale en heftig løsesum gebyr for at gøre de cyber-kriminelle dekryptere deres filer. Dharma er en af de nyeste malware varianter med højeste sats af infektioner, så angreb er ved at stige. Hvis din computer er blevet inficeret med den nyeste .write variant af malware, Vi blev genoptaget, at du læser dette blogindlæg, da det indeholder en vejledning i at kunne fjerne denne variant af Dharma og hvordan man kan forsøge at inddrive så mange filer, som du kan uden at betale løsesum i Bitcoin.
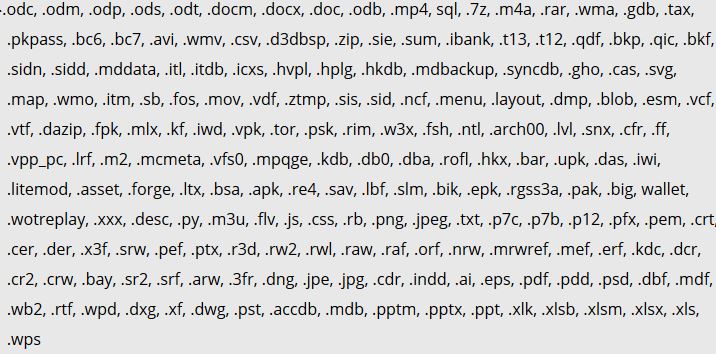
| Trussel Navn | .skrive filer Virus |
| Kategori | ransomware-virus. |
| Main Activity | Inficerer computeren efter som krypterer vigtige dokumenter og holder dem som gidsler, indtil en løsesum er betalt. |
| Tegn på Presence | Filer er krypteret med den .SKRIVE filtypenavn. |
| Sprede | Via ondsindet e-mail-spam og sæt infektion værktøjer. |
| Påvisning + udsendelse | DOWNLOAD Removal Tool TIL .write filer Virus |
| File gendannelse | Hent Data Recovery Software, for at se, hvor mange filer krypteret af .write filer Virus ransomware du vil være i stand til at inddrive. |
Hvilken type malware Er .write filer Virus Ransomware
Ransomware generelt har været en stigende tendens med infektion og særlig effektiv. Det beder primært på de brugere, der ikke har en backup af deres vigtige filer. Den .write filer Virus Ransomware krypterer dine vigtige dokumenter, musik, videoer, billeder, arkiver og andre data, hvilket gør dem ikke længere er effektiv. Filerne kan ikke åbnes efter at de er blevet angrebet af den .write filer Virus Ransomware, og de har en brugerdefineret forlængelse tilføjet efter deres filnavn - en tilfældig A-Z 0-9 breve.
Faktisk, infektioner med ransomware, ligesom .write filer Virus er blevet så massive, at du kan være sikker på, at i det øjeblik nogen et eller andet sted i verden er enten åbne en mistænkelig spammet vedhæftet fil, tro det er legit eller klikke på et ondsindet link.
Men det ransomware kan også spredes helt automatisk, svarende til den tidligere Dharma virus, som blev spredt via e-mail spam infektion, forårsager data fra tusindvis af computere computere skal krypteres. Skaberne af ransomware, der er involveret i denne handling, som om de har intet at tabe og ikke rode rundt. De har investeret meget i deres angreb og organiseret dem, så så mange uerfarne brugere som muligt bliver ofre.
Den Dharma-virus er blevet spottet i en ny variant, denne gang ved hjælp af .skrive filtypen, helt uden forbindelse til den tidligere .dharma og .wallet dem. Den nye Dharma ransomware kommunikerer også via e-mail, hvorigennem det sender et decryptor efter løsesummen er blevet betalt. Hvis du er et offer for den nye Dharma ransomware ved hjælp af .write filtypenavn, vi råde dig til at læse denne artikel og lære at fjerne virus filer og forsøge at afkode .skrive krypterede objekter.
.skrive Ransom Virus - hvad betyder det gøre
At være en variant af Crysis ransomware familie, som eksisterer i hundredvis af varianter, hvoraf mange er dekrypteres, Dharma .ARENA ransomware er blevet rapporteret til at droppe en eller flere eksekverbare filer i Windows-mappen% AppData%.
Efter at gøre så, virus kan ændre Windows registreringsdatabasen de, mere specifikt Shell sub-nøgle med følgende placering:
- HKLM / Software / Microsoft / Windows NT / CurrentVersion / Winlogon / Shell
Derefter, virus kan også ændre nøglen Kør i registreringsdatabasen for at køre den eksekverbare fil(med) i% AppData% mappe. Det centrale er med følgende sti:
- HKLM / Software / Microsoft / Windows / CurrentVersion / Run /
Dette kan resultere i virus-filen opstart ved siden af Windows opstart processen.
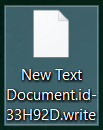
Den Dharma ransomware falder også en løsesum notat fil med en løsesum budskab og placerer den et sted let at finde. Derefter, Dharma ransomware virus kan angribe filer med følgende filtyper at kryptere dem:
Efter Dharma krypterer filerne, virussen efterlader filerne ikke længere i stand til at blive åbnet og tilføjer filtypen .ID-{victimID}.[e-mail].skrive til hver krypteret fil.
Efter krypteringen af Dharma ransomware har afsluttet, virus kan også slette VSS (øjebliksbilleder) på den inficerede computer for at forhindre ofre fra genoprette deres filer via disse sikkerhedskopier.
Dharma .write Ransomware - Hvordan klarede jeg mig inficeret
Infektionsprocessen Dharma ransomware udføres primært via spammed e-mails, der har vildledende beskeder indlejret i dem. Sådanne meddelelser kan foregive at blive sendt fra tjenester som PayPal, USPS, FedEx og andre. De kan indeholde vedhæftede filer, der foregiver at være fakturaer og andre falske type filer. Andre social engineering teknikker omfatter:
- Falske knapper og billeder, som om de e-mails sendes fra en social media websted, ligesom LinkedIn.
- Falske PayPal links.
- Links til Google Drive og falske e-mails, der ser det samme, som hvis de sendes fra Google.
Andre infektion værktøjer kan også omfatte brugen af torrent websteder og andre tredjeparts websteder til at uploade falske opdateringer, falske installatører samt andre svigagtige eksekverbare.
Fjern Dharma .write Ransomware og Get krypterede filer Tilbage
Til fjernelse af den .skrive variant af Dharma ransomware, anbefalinger er at fokusere på følgende fjernelse instruktioner nedenfor og starte computeren i fejlsikret tilstand. I tilfælde manuel fjernelse i nedenstående instruktioner ikke arbejde for dig, sikkerhedseksperter anbefaler at downloade et stærkt anti-malware værktøj, der vil hurtigt fjerne Dharma .ARENA ransomware og beskytte din computer i fremtiden også. Hvis du ønsker at gendanne filer krypteret af Dharma, vi har tilbudt flere forslag nedenfor, der kan være i stand til at hjælpe med dette emne.
Opstart i fejlsikret tilstand
Til Windows:
1) Holde Windows Key og R
2) En run vindue vises, i det typen “msconfig” og ramte Gå ind
3) Efter vises gå til fanen Boot og vælg Sikker start
Klip .write Filer Virus i Task Manager
1) Trykke CTRL + ESC + SHIFT på samme tid.
2) Find den “Processer” fane.
3) Find den ondsindede processen med .write filer Virus, og ender det opgave ved at højreklikke på den og klikke på “Afslut proces”
Eliminer .write filer Virus Ondsindede Registre
For de fleste Windows-varianter:
1) Holde Windows-knap og R.
2) i “Løb” box type “Regedit” og ramte “Gå ind”.
3) Holde CTRL + F nøgler og typen .write filer Virus eller filnavnet på det skadelige eksekverbare af virus, som normalt er placeret i% AppData%, %Midlertidig%, %Lokal%, %Roaming% eller% SystemDrive%.
4) Efter at have placeret ondsindede registreringsdatabasen objekter, hvoraf nogle er normalt i Run og RunOnce undernøgler slette dem ermanently og genstart computeren. Her er hvordan man kan finde og slette nøgler til forskellige versioner.
Til Windows 7: Åbn menuen Start, og i søgningen type og skriv regedit -> Åbn den. -> Hold CTRL + F-knapper -> Type .write filer virus Virus i søgefeltet.
Vinde 8/10 brugere: Knappen Start -> Vælg Kør -> skriv regedit -> Hit Enter -> Tryk på CTRL + F-knapper. Skriv .write filer Virus i søgefeltet.
Automatisk fjernelse af .write filer Virus
Sådan gendannes filer, Krypteret ved .write filer Virus Ransomware.
Metode 1: Brug Shadow Explorer. Hvis du har aktiveret Filhistorik på din Windows maskine én ting du kan gøre er at bruge Shadow Explorer til at få dine filer tilbage. Desværre er nogle ransomware vira kan slette disse skygge volumen kopier med en administrativ kommando til at forhindre dig i at gøre netop det.
Metode 2: Hvis du forsøger at dekryptere dine filer ved hjælp af tredjeparts dekryptering værktøjer. Der er mange antivirus udbydere, der har dekrypteret flere ransomware vira de sidste par år, og bogført decryptors for dem. Chancerne er, hvis din ransomware virus bruger den samme kryptering kode, der bruges af en dekrypteres virus, du kan få filerne tilbage. Dog, dette er heller ikke en garanti, så du måske ønsker at prøve denne metode med kopier af de originale krypterede filer, fordi hvis en tredjepart program piller ved deres krypterede struktur, de kan blive beskadiget permanent. Her er de leverandører til at søge:
- Kaspersky.
- Emsisoft.
- TrendMicro.
Metode 3: Brug af Data Recovery værktøjer. Denne metode er foreslået af flere eksperter på området. Det kan bruges til at scanne din harddisk 's sektorer og dermed forvrænge de krypterede filer på ny, som om de blev slettet. De fleste ransomware virus normalt slette en fil og oprette en krypteret kopi at forhindre sådanne programmer for at genoprette filer, men ikke alle er dette sofistikerede. Så du kan have en chance for at genskabe nogle af dine filer med denne metode. Her er flere data recovery programmer, som du kan prøve og genoprette det mindste nogle af dine filer: