Både enkeltpersoner og virksomheder løbende blive ramt af cyber kriminelle og deres grusomme opfindelser. Som mange sikkerhedsmæssige rapporter 2014 og den første halvdel af 2015 angiver - angreb numre er hurtigt stigende på verdensplan, nå nye, utroligt toppe. Mange spørgsmål vedrørende privatlivets fred og sikkerhed er stadig ubesvaret, eller i bedre sager - delvist besvaret.
Afhængigt af om du er ejer af en virksomhed, en individuel bruger, eller en medarbejder i korporative verden, den taktik er udøvet af cyberforbrydere kan variere. Er jeg et offer for en målrettet angreb, eller en massiv én? Er formålet med angrebet klar, eller er det endnu at blive opdaget? Hvilken slags oplysninger blev stjålet fra mig? Er folk i min kontaktliste også truet?
Som vi kan se, spørgsmålene på vej ud af ondsindede hensigter kan formere sig hurtigt, samt de måder, der bruges af virtuelle lovovertrædere på pro rata-basis. I en nøddeskal, at øge kvaliteten af sikkerhed, man har til at blive informeret om mange veje malware kan følge tilbage til sin computer. Og jo mere man ved, jo sværere vil de blive ofre for online trusler.
I det aspekt af 2015, Vi har identificeret ti typer angreb. Vi har samlet nylig aktive malware stykker, og vi har listet dem efter deres sværhedsgrad. Med udgangspunkt i de mest ondsindede dem.
→NB! Før du fortsætter, Det er vigtigt at bemærke, at de trusler, vi er ved at liste er indbyrdes forbundne, til et punkt, hvor det kan få ganske vanskelig at kategorisere et stykke malware som én bestemt type.
ransomware
Ransomware først kom ind i online-plads i 1989 når AIDS Trojan a.k.a. PC Cyborg designet af Joseph Popp blev indført. AIDS Trojan er den første fil-kryptering trussel til at kryptere brugerens filer på harddisken og kræve penge for at låse dem. Siden da, ransomware har udviklet sig så meget, at en enkelt ransomware stykke - Cryptowall, har kostet verdensøkonomien $18 millioner i mindre end et år. For at sige det med andre ord, Cryptowall skabere har tjent millioner af dollars, mens afpresse penge fra private og virksomheder.
Andre bemærkelsesværdige ransomware trusler, der med succes har ’røvet’ brugere i løbet af det seneste år er:
- CryptoLocker
- Troldesh
- Bit Cryptor
- Tox Ransomware
- Alpha Crypt
- Los Pollos Hermanos
- locker
At bo beskyttet mod ransomware, brugere bør:
- Aktiver automatiserede patches til det operationelle system, og webbrowsere.
- Begræns til at downloade software fra sikre udbydere.
- Bloker pop-up vinduer.
- Åbn ikke e-mails sendt fra ukendte afsendere.
Exploit Kits
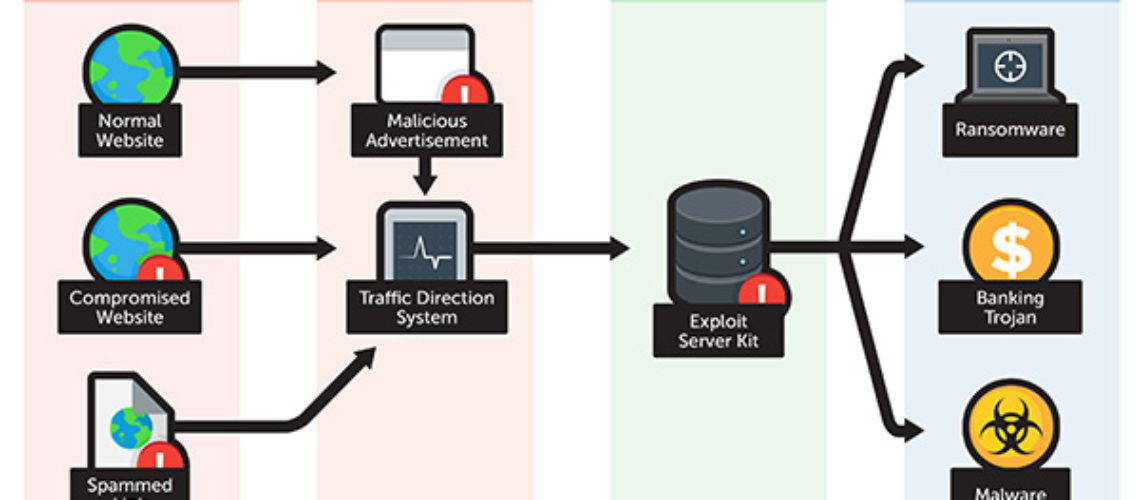
Da 2012, når den berygtede Blackhole EK blev påvist i naturen, udnytter kits har også skabt en hensynsfuld mængde af infektioner og betragtes en alvorlig cyber trussel. Selvom forskellige udnytte kits kan implementere forskellige forurening taktik, historien normalt går som det følger:
- 1. Den bruger besøger en kompromitteret hjemmeside, der er blevet angrebet af cyberkriminelle.
- 2. Brugeren oplever en række omdirigeringer og ender på en server hosting EK.
- 3. Den EK indsamler oplysninger om ofrets system, og bestemmer hvordan vi kommer videre med nyttelasten.
- 4. Hvis proceduren er vellykket, nyttelasten - malware, bank Trojan eller Ransomware - downloades til brugerens pc.
Bemærkelsesværdige eksempler på udnytte kits, der for nylig er blevet opdaget er:
- Nuklear udnytte kit
- RIG Exploit Kit (nylig brugt til at aflevere CryptoWall)
- Hanjuan udnytte kit (også kendt som Timba Trojan og Fobber)
- Angler udnytte kit
Eftersom nyere udnytter kits observeres at udnytte svagheder fortrinsvis i Internet Explorer, Adobe Flash, og Adobe Reader, brugere skal opdatere dem jævnligt og muliggøre automatiserede pletter hvor det er muligt.
Banking trojanere
To store finansielle stealers blev elimineret tilbage i 2014 - Gameover Zeus stadig aktiv i 2017 og Shylock. Dog, i stedet for at blive chokeret over deres udryddelse, cyberkriminelle hurtigt flyttet frem og introducerede Dyreza og Dridex til den finansielle verden.
Den Dridex Trojan, også kendt som Feodo, Bugat eller Geodo, løbende angrebet bankorganisationer. På et tidspunkt, den ondsindede trojanske var at udnytte makroer i Microsoft Office-pakken. Selvom makroer er normalt som standard deaktiveret af virksomheder, cyberkriminelle forsøger stadig at lokke arbejdsgiverne i at give dem mulighed.
En anden ond bank Trojan døbt Vawtrak, Neverquest eller Snifula, blev også spottet. Når Vawtrak er aktiveret, den vinder adgang til offerets bankkonti og stjæler hans loginoplysninger. Vawtrak blev distribueret via:
- Drive-by downloads udført efter åbning af en spam email vedhæftet fil.
- Malware Downloader.
- udnytte kit.
→Som allerede synlige, ondsindede angreb bliver mere sofistikeret med tiden, gennemførelsen af de vigtigste funktioner i mange-faced malware.
Indsamling af malware, orm
Duqu 2.0 er blevet identificeret som den mest sofistikerede stykke malware nogensinde set. Korrektion - en samling af malware. Duqu 2.0 er en forbindelse efterfølgeren af Duqu orm, der sidestiller funktionerne i en trojansk hest og en computer orm. I bund og grund, Duqu er en sofistikeret cyber spionage værktøj, der endda lykkedes at gå på kompromis med Kaspersky Labs sikkerhed.
Kasperskys forskere har afsløret, at målene i Duqu 2.0 primært knyttet til forhandlingerne om Irans nukleare deal. Flere it-sikkerhedsfirmaer blev også målrettet, såvel som vestlige, Asiatisk og i Mellemøsten organisationer. Det er sikkert at antage, at udformningen af Duqu 2.0 (og lignende malware stykker) er ikke en joke til dens skabere.
PoS (Salgsstedet) Malware
Malware målrettet betalingssystemer behandlingssystemer er ikke nyt for os. Dog, der er en stigning i PoS malware varianter. En ældre stykke PoS Malware først udgivet i oktober 2013 - NewPoSThings - endnu en gang blevet opdaget. Dens seneste angreb, i april 2015, indikerede, at malware var rettet mod 64-bit maskiner med høj versionsnumre.
Anden PoS malware stykke påvist i 2015 er Punkey, indstillet til at udsende en ganske aggressiv point-of-sale operation at udtrække personlige oplysninger. Regelmæssige ofre for PoS malware er virksomheder - restauranter, kasinoer, feriesteder, hoteller. Ethvert sted, der kræver eller tilbyder betaling med kreditkort kan blive et mål.
Social engineering angreb
I sikkerhed, social engineering er nogen psykologisk manipulation, hvilket resulterer i at gøre folk udføre bestemte handlinger eller give væk følsomme oplysninger. Hvad adskiller social engineering fra en almindelig con er det faktum, at det normalt er en lille uønsket af en mere omfattende ordning. I 2015, Vi har allerede observeret flere angreb, der er ansat eller anden form for social engineering. Mærkeligt nok, cybercrooks henvender sig ofte til sociale medier til at udnytte social engineering. F.eks, en nylig Facebook fidus lovede brugere 300 iPhones til gengæld for at klikke på Ligesom knap.
Social engineering angreb udført på internettet kan opdeles i fire kategorier:
- Phishing - med henblik på at opnå personlige oplysninger.
- pretexting – fokuseret på at gøre en god undskyldning, en smart scenarie, som senere vil blive brugt i forsøget på at samle kompromitterede brugernes personlige oplysninger.
- baiting - svarende til phishing, med den forskel, at en præmie element bliver tilbudt til offeret.
- For hvad, for hvem - relateret til phishing og baiting. En service er offeredd i stedet for et element.
Falske Tech Support Services
Det virker som om falsk teknisk support hjemmesider og linier aldrig sover. Flere og flere svigagtige tjenester rapporteres på daglig basis. Som en kendsgerning, fortæller en reel støtte linje fra en falsk er ikke en vanskelig opgave. Dog, slyngler tendens til at udnytte den uagtsomhed af gennemsnitlige brugere. Plus, falske support svindel normalt kommer bundtet med ad-understøttet software, sigter mod udbredte browsere.
Når den fidus er aktiveret, brugeren vil begynde at se pop-up vinduer hævder, at hans pc er blevet ramt af flere trusler. Sådanne pop-ups altid give et telefonnummer, der skal kaldes. Et eksempel på sådan et tal er 1-855-791-2391. At bo sikkert, brugere er stærkt anbefales ikke at ringe til det viste nummer, men at arbejde hen imod at scanne deres systemer. Hvis en sådan opkald påbegyndes, kan opnås fjernadgang til systemet, og forskellige legitimationsoplysninger (herunder bankvirksomhed) kan høstes.
Rogue antivirussoftware
Rogue AV software er software, der promoveres som et nyttigt anti-malware én. I stedet for at gøre, hvad det er annonceret at gøre - beskytte systemet mod malware, rogue AV program vil gøre præcis det modsatte. Det vil bremse pc, kompromittere brugerens sikkerhed online, og gøre systemet mere sårbart over for malware-angreb.
Et eksempel på en populær rogue er Antivirus Pro 2017. Det er fra samme familie som Antivirus Pro 2015 og Defender Pro 2015.
Når det er installeret, slyngelstater antivirus værktøj starten vil begynde at udføre en falsk systemscanning. Mens scanning af systemet, flere spørgsmål vil blive fundet. For at genvinde kontrollen over sin computer, kører en ægte AV stykke er en god idé.
Potentielt uønskede programmer
Potentielt uønskede programmer og ad-understøttet software anses ikke for ondsindet, men de ofte åbne porten til ondsindede online trusler. PUP sandsynligvis har indtastet i systemet sammen med en anden gratis app downloades fra internettet. Den beskrevne fremgangsmåde er lovlig, selvom det kan synes lyssky. Det kaldes bundling og bruges primært til at tjene penge på forskellige platforme og dækker økonomiske tab.
Adware
Vores forskning viser, at hundredvis af PUP og ad-støttede browser add-ons er frigivet på daglig basis. For at være beskyttet mod den irriterende tredjepart indtrængen, brugere bør være meget opmærksomme på, hvad de henter. Læs altid EULA (Slutbrugeraftale), aftale om download, og Privatlivspolitik. Going for den avancerede software installeret, som giver dig mulighed for at se og fravælge nogen ekstra programmer er også afgørende.
*Artikel Kilder:
https://blog.malwarebytes.org/intelligence/2013/02/tools-of-the-trade-exploit-kits/
http://www.infosecurity-magazine.com/news/financial-trojans-set-to-roar-back/
http://www.trendmicro.com/vinfo/us/security/news/vulnerabilities-and-exploits/exploit-kits-past-present-and-future
http://cfoc.org/
http://sensorstechforum.com/
*Image Source:
http://www.trendmicro.com/