Dette er et blogindlæg, skabt til at informere dig, hvad der er er .gerosan filer og hvordan du fjerner den .gerosan malware fra din computer, plus hvordan du kan forsøge at få .gerosan filer til at åbne.
En ransomware virus, bruger .gerosan filtypenavn blev opdaget af forskere til at tilhøre STOP / DjVu ransomware familie af virus. Infektionen vigtigste mål er at gøre de filer på din computer system ikke længere være i stand til at blive åbnet. Derefter, virussen efterlader en _readme.txt løsesum notat fil, hvor hackerne bag den oplyse og afpresse ejeren af computeren offer, at de skal betale løsepenge for at få deres krypterede filer til at arbejde igen. Hvis din computer er blevet inficeret af den .gerosan fil forlængelse ransomware, vi på det kraftigste foreslå dig at læse denne artikel grundigt.
| Trussel Navn | .gerosan filer Ransomware |
| Kategori | Ransomware / Cryptovirus. |
| Main Activity | Inficerer computeren efter som krypterer vigtige dokumenter og holder dem som gidsler, indtil en løsesum er betalt. |
| Tegn på Presence | Filerne krypteres med .gerosan udvidelse og brugere er afpresset til at betale løsepenge for at få data til at arbejde igen.. |
| Sprede | Via ondsindet e-mail-spam og sæt infektion værktøjer. |
| Påvisning + udsendelse | DOWNLOAD Removal Tool TIL .gerosan filer Ransomware |
| File gendannelse | Hent Data Recovery Software, for at se, hvor mange filer krypteret af .gerosan filer Ransomware ransomware du vil være i stand til at inddrive. |
Den .gerosan filer Ransomware virus er blevet spottet ved hjælp af sin egen filtype. Den .gerosan filer Ransomware virus kommunikerer også via TOR hvorigennem det sender et Decrypter efter løsesummen er blevet betalt. Hvis du er et offer for den nye .gerosan filer Ransomware virus vi råde dig til at læse denne artikel og lære at fjerne virus filer og forsøge at afkode krypterede objekter.
.gerosan Filer Ransomware Virus - hvad betyder det gøre
At være en variant af den ransomware familie, der findes i en masse virus familier, den .gerosan filer Ransomware ransomware er blevet rapporteret til at droppe en eller flere eksekverbare filer i %AppData% Windows-mappen.
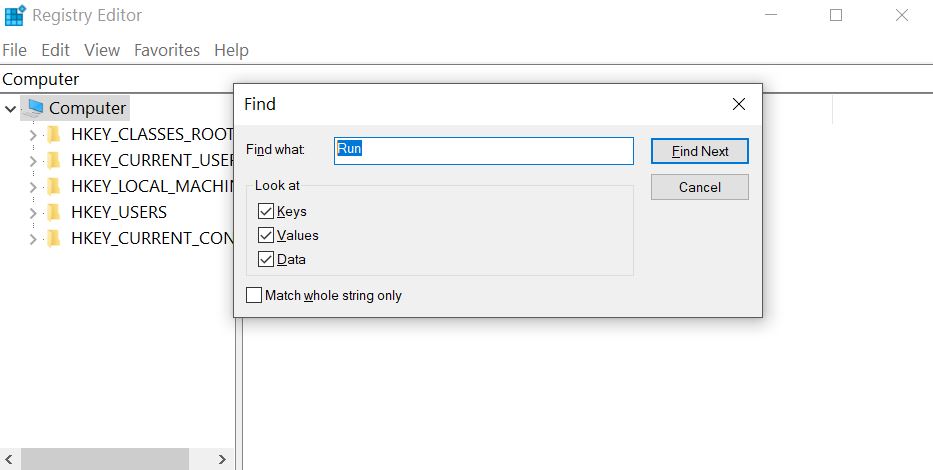
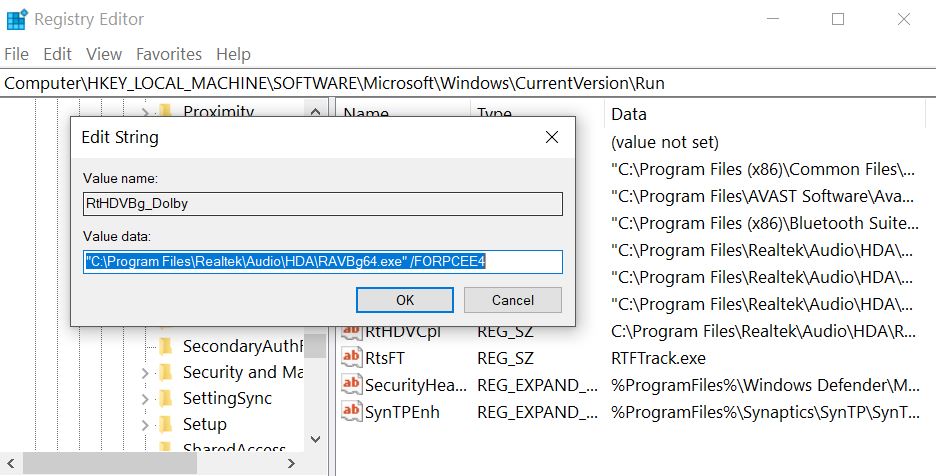
Efter at gøre så, den .gerosan filer Ransomware virus kan ændre Windows registreringsdatabasen de, mere specifikt Shell sub-nøgle med følgende placering:
- HKLM / Software / Microsoft / Windows NT / CurrentVersion / Winlogon / Shell
Derefter, den .gerosan filer Ransomware virus kan også ændre nøglen Kør i registreringsdatabasen for at køre den eksekverbare fil(med) i% AppData% mappe. Det centrale er med følgende sti:
- HKLM / Software / Microsoft / Windows / CurrentVersion / Run /
Dette kan resultere i virus-filen opstart ved siden af Windows opstart processen.
.gerosan filer Ransomware også falder en løsesum notat fil med en løsesum budskab og placerer den et sted let at finde. Derefter, den .gerosan filer Ransomware virus kan angribe filer med følgende filtyper at kryptere dem:
- Videoer.
- Billeder.
- Dokumenter.
- lydfiler.
- Arkiv.
Efter .gerosan Filer Ransomware krypterer filerne, virussen efterlader filerne ikke længere i stand til at blive åbnet og sandsynligvis tilføjer en brugerdefineret fil extenson til dem.
.gerosan Filer Ransomware Ransomware - Hvordan klarede jeg mig inficeret
Infektionsprocessen af .gerosan filer Ransomware foregår primært via spammed e-mails, der har vildledende budskaber indlejret i dem. Sådanne meddelelser kan foregive at blive sendt fra tjenester som PayPal, UPS, FedEx og andre. De kan indeholde vedhæftede filer, der foregiver at være fakturaer og andre falske type filer. Andre social engineering teknikker omfatter:
- Falske knapper og billeder, som om de e-mails sendes fra en social media websted, ligesom LinkedIn.
- Falske PayPal links.
- Links til Google Drive og falske e-mails, der ser det samme, som hvis de sendes fra Google.
Andre infektion værktøjer kan også omfatte brugen af torrent websteder og andre tredjeparts websteder til at uploade falske opdateringer, falske installatører samt andre svigagtige eksekverbare.
Hvilke filer kan blive Påvirket af .gerosan filer Ransomware Ransomware?
.gerosan filer Ransomware Ransomware fungerer som en typisk fil-koder Trojan. Så snart det bliver adgang til din maskine, denne cryptomalware vil udføre en hurtig scanning for at finde stierne til alle dine personlige filer. Den målrettede data omfatter alle MS Office-dokumenter, dine dyrebare fotos og videoer, dine databaser, programfilerne, etc. Kun et par filer som dem relateret til kernen Windows processer kan skånet. Når operationen ender, du vil bemærke en truende lockdown besked på skrivebordet og standard filtypen det vil blive ’.dll’. De cyberkriminelle giver ofrene kun flere dage betale løsesum af Bitcoins, ellers de truer med at slette evigt dekrypteringsnøgle. Formålet med denne skræmmende budskab er at chokere den person og gøre ham handle irrationelt. Ofrene føler sig ofte som den eneste løsning på problemet er at betale pengene. I virkeligheden, alle specialister anbefale enstemmigt ikke at følge instrukserne fra hackere til flere forskellige årsager.Hvordan kan beskytte dig mod .gerosan filer Ransomware Ransomware?
Denne ransomware kan forårsage store og ofte uoprettelige skader på de berørte maskiner. Heldigvis, du kan forhindre smitte, så længe du er på vagt i løbet af dine online-sessioner. Denne trojanske er ikke kendt for at bruge nogle unikke metoder til at infiltrere forsvaret af din computer. Den mest sandsynlige årsag til .gerosan filer Ransomware Ransomware at indtaste er via spam e-mails. Du kan modtage en besked med en chokerende indhold, opmuntre dig til at enten klikke på et ondsindet link eller downloade en kompromitteret fil. Hackerne har et helt arsenal af værktøjer til at manipulere dig til at gøre det. For eksempel, de kan hævde at repræsentere en international bank eller nogle populære rederi. Hvis de adresse du uden at nævne dit navn, e-mailen er sandsynligvis et fupnummer, og du bør ignorere det. Desværre, hvis du blot klikke eller downloade inficerede fil, din handling vil højst sandsynligt være nok til at aktivere de skadelige koder af .gerosan filer Ransomware Ransomware. I dette tilfælde, kun en troværdig sikkerhedsløsning kan være i stand til at forhindre den forestående skade.
Sådan Slet .gerosan filer Ransomware Ransomware og dekryptere dine filer gratis?
De væsentligste årsager til ikke at betale løsesummen er to. Første, kan du ikke modtage den lovede oplåsning nøglen, selv efter at gøre præcis som efterspørgslen hackere. De har ofte fidus ofrene fordi Bitcoin platformen tillader ikke restitutioner, og folk har ingen måde at få deres penge tilbage. Den anden grund til ikke at finansiere cyberkriminelle er, at dine penge kun vil motivere dem til at skabe mere aggressiv ransomware ligesom .gerosan filer Ransomware. På den anden side, hvis deres angreb er forgæves, de kan stoppe spamming internettet med sådanne ondsindede trojanske heste. Disse parasitter kræver en hel del bestræbelser på at blive skabt professionelt og spredes effektivt.
Når du beslutter ikke at betale løsepenge, der er flere andre måder, der kan hjælpe dig med at dekryptere dine personlige filer. Du bør begynde forsøg ved at fjerne alle spor af malware. Hvis du undlader at slette .gerosan filer Ransomware Ransomware korrekt, det kan dekryptere dine filer igen i fremtiden, eller spredes til andre tilsluttede enheder. Den manuelle fjernelse er ikke den anbefalede løsning, da det kræver ekspert-niveau viden i computere. Den mest pålidelige taktik er at bruge dedikeret sikkerhedssoftware, der har tilføjet F.gerosan filer Ransomware Ransomware til sin database. Når scanningen er færdig, bør du prøve nogle af de programmer til restaurering af filer eller den integrerede funktionen Systemgendannelse. Hvis du er heldig nok til at have et ekstra kopi af dine filer på nogle eksterne enhed, du kan importere dem tilbage til din computer sikkert.
Removal instruktioner til .gerosan filer Ransomware
Hvis du ønsker at fjerne .gerosan filer Ransomware, Vi anbefaler, at du først sikkerhedskopiere dine data, just in case noget går galt. Derefter, du kan følge manuel eller automatisk fjernelse instruktioner nedenfor, afhængigt af, hvilken type trin passer dig mere. Hvis du mangler erfaring og tillid til, at du vil fjerne .gerosan filer Ransomware manuelt, så skal du gøre, hvad de fleste eksperter ville og spare tid ved at downloade og køre en scanning med en avanceret anti-malware-software. Sådanne programmer er skabt til hurtigt at identificere og fjerne trusler og programmer med indgribende adfærd, ligesom .gerosan filer Ransomware, plus de også til formål at sikre, at dit system er beskyttet mod fremtidige indbrud samt.
Klargøring før fjernelse af .gerosan filer Ransomware:
1.Sørg for at sikkerhedskopiere dine filer.
2.Sørg for at have denne vejledning side altid åben, så du kan følge trinene.
3.Vær tålmodig, da fjernelsen kan tage lidt tid.
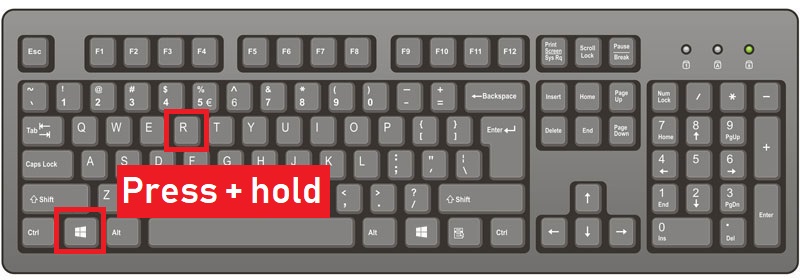
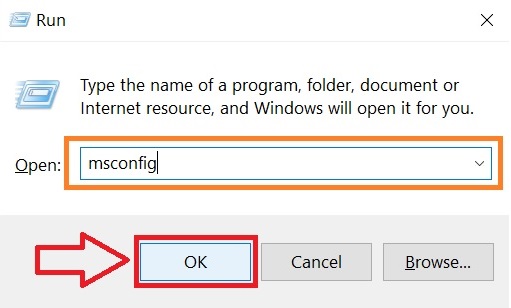
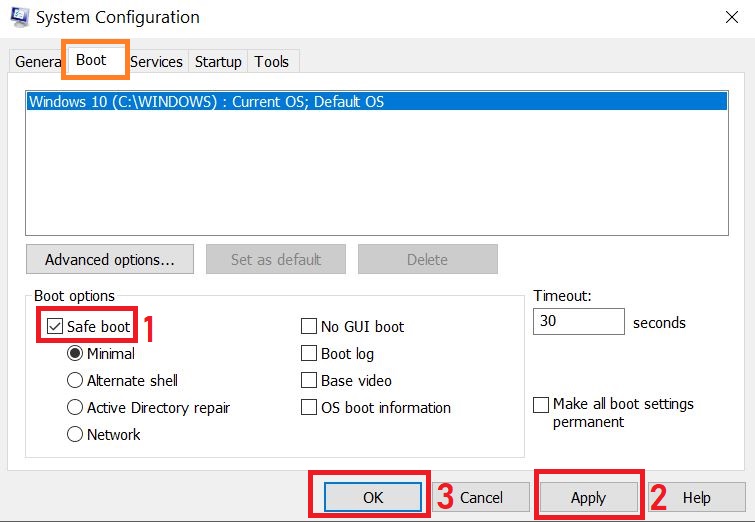
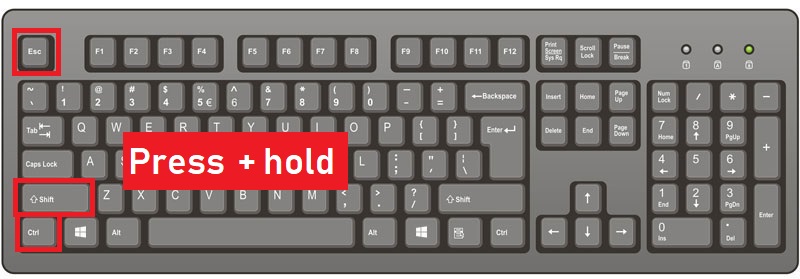
Step 1: Genstart computeren i fejlsikret tilstand:
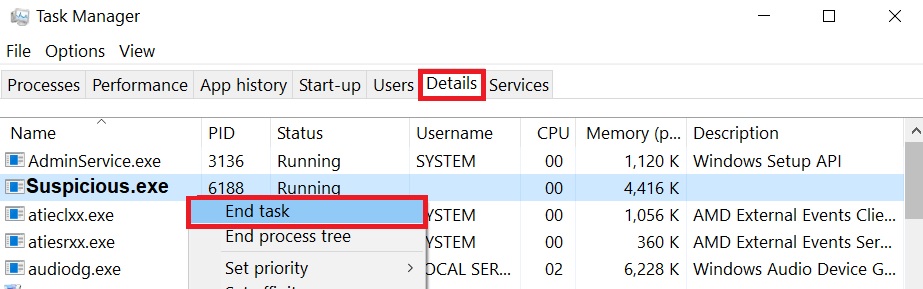
Step 2: Klip .gerosan Filer Ransomware i Task Manager
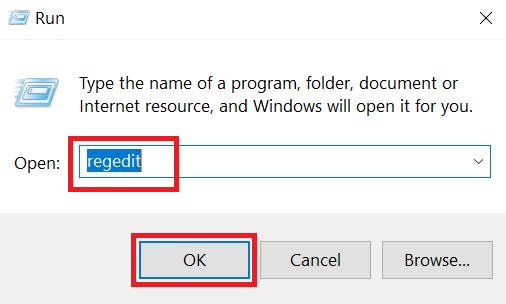
Step 3: Eliminer .gerosan filer ransomware s Ondsindede Registre.
For de fleste Windows-varianter:
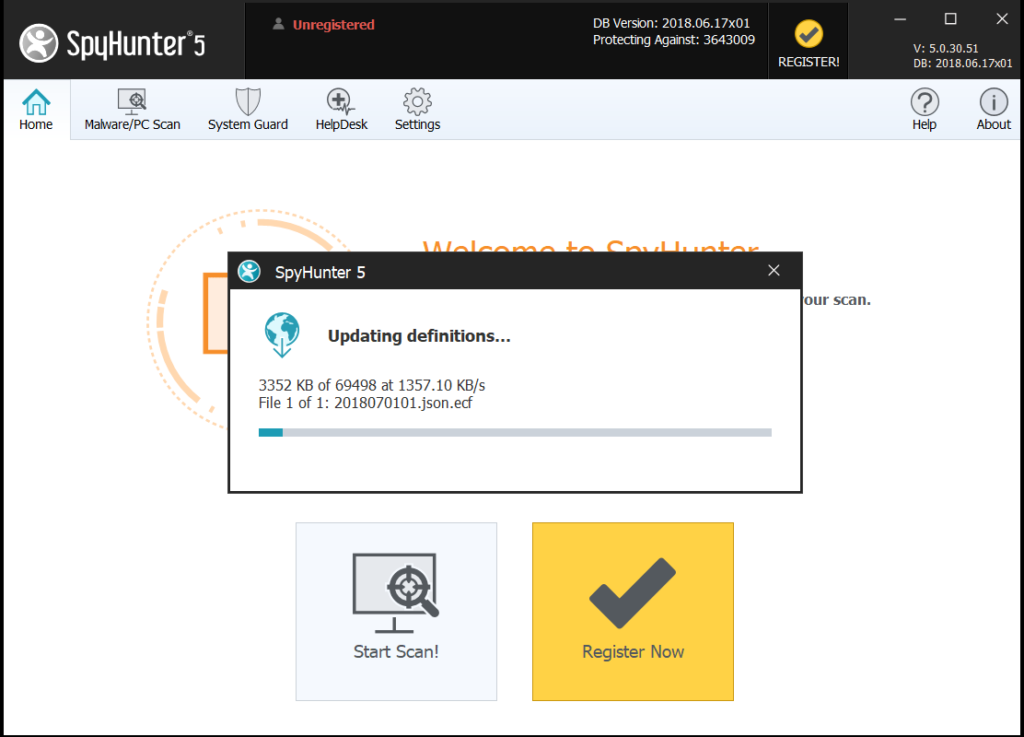
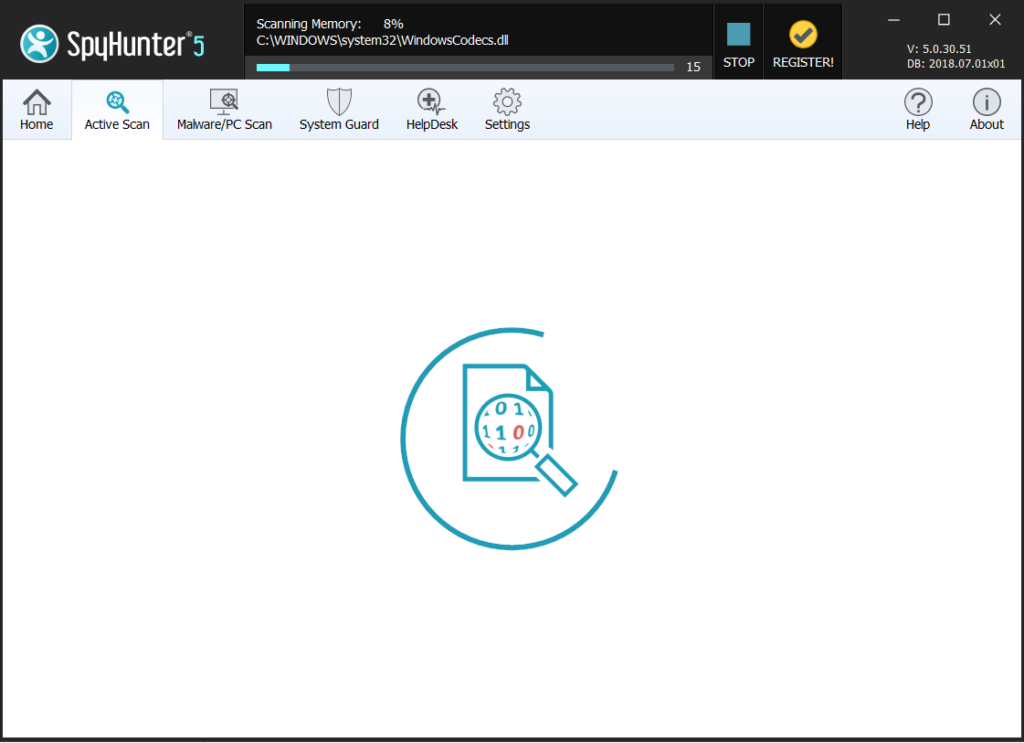
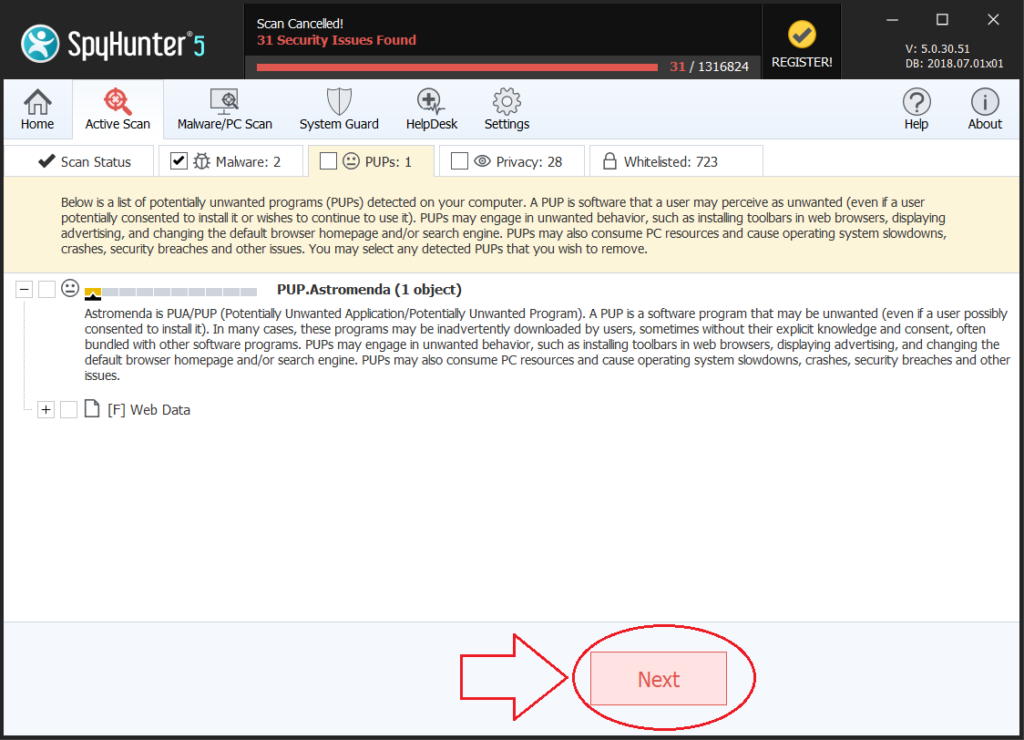
Step 4: Scan efter og fjerne alle virus filer, relateret til .gerosan filer Ransomware og sikre dit system.
Hvis du er i Sikker tilstand, starte tilbage til normal tilstand og følge nedenstående trin
Det er tilrådeligt at køre en gratis scanning, før der indgås den fulde version. Du skal sørge for, at malware er opdaget af SpyHunter først.
Step 5:Genoprette filer krypteret med .gerosan filer Ransomware Ransomware.
Metode 1: Brug Shadow Explorer. Hvis du har aktiveret Filhistorik på din Windows maskine én ting du kan gøre er at bruge Shadow Explorer til at få dine filer tilbage. Desværre er nogle ransomware vira kan slette disse skygge volumen kopier med en administrativ kommando til at forhindre dig i at gøre netop det.
Metode 2: Hvis du forsøger at dekryptere dine filer ved hjælp af tredjeparts dekryptering værktøjer. Der er mange antivirus udbydere, der har dekrypteret flere ransomware vira de sidste par år, og bogført decryptors for dem. Chancerne er, hvis din ransomware virus bruger den samme kryptering kode, der bruges af en dekrypteres virus, du kan få filerne tilbage. Dog, dette er heller ikke en garanti, så du måske ønsker at prøve denne metode med kopier af de originale krypterede filer, fordi hvis en tredjepart program piller ved deres krypterede struktur, de kan blive beskadiget permanent. De fleste af de i øjeblikket tilgængelige decryptors for ransomware vira kan ses, hvis du besøger NoMoreRansom projekt – et projekt, der er resultatet af en samlet indsats fra forskere fra hele verden for at skabe dekryptering software til alle ransomware virus. Du skal blot gå der ved at klikke på følgende LINK og find din ransomware-version Decrypter og prøv det, men altid huske at gøre en BACKUP først.
Metode 3: Brug af Data Recovery værktøjer. Denne metode er foreslået af flere eksperter på området. Det kan bruges til at scanne din harddisk 's sektorer og dermed forvrænge de krypterede filer på ny, som om de blev slettet. De fleste ransomware virus normalt slette en fil og oprette en krypteret kopi at forhindre sådanne programmer for at genoprette filer, men ikke alle er dette sofistikerede. Så du kan have en chance for at genskabe nogle af dine filer med denne metode. Her er flere data recovery programmer, som du kan prøve og genoprette det mindste nogle af dine filer: