Dette indlæg er lavet for at vise dig, hvordan du kan fjerne det .boston filer virus af STOP ransomware og hvordan du kan gendanne filer, krypteret med den ekstra .boston filtypenavn.
Endnu en variant af STOP ransomware er blevet påvist i naturen, denne gang ved hjælp udvidelse af .boston fil. den ransomware, ligesom andre varianter af STOP til formål at kryptere filerne på computerne inficeret med det med de vigtigste idé at få ofrene til at betale løsepenge for at få filerne til at være operationelt igen. Virussen giver en frist på 24 timer for løsepenge, der skal betales i cryptocurrencies og hvis det ikke er opfyldt, prisstigningerne. Hvis din computer er blevet inficeret af den .boston filer virus, foreslår vi, at du læser denne artikel for at lære mere om, hvad den gør, hvordan den breder sig, og hvordan du kan fjerne det og forsøge at gendanne dine filer.
| Trussel Navn | .boston filer Ransomware |
| Kategori | ransomware-virus. |
| Main Activity | Variant af STOP ransomware virus. Inficerer computeren efter som krypterer vigtige dokumenter og holder dem som gidsler, indtil en løsesum er betalt. |
| Tegn på Presence | Filer er krypteret med en .boston filtypen og løsepenge note tabes med løsepenge instruktioner. |
| Sprede | Via ondsindet e-mail-spam og sæt infektion værktøjer. |
| Påvisning + udsendelse | DOWNLOAD Removal Tool TIL .boston Filer Ransomware |
| File gendannelse | Hent Data Recovery Software, for at se, hvor mange filer krypteret med .boston Filer Ransomware ransomware vil du være i stand til at inddrive. |
STOP virus er blevet spottet i en ny variant, denne gang ved hjælp af .boston filtypenavn. Det er relateret til den foregående .udgift og .Grove dem. Den nye STOP ransomware kommunikerer også via e-mail, hvorigennem det sender et Decrypter efter løsesummen er blevet betalt. Hvis du er et offer for den nye STOP ransomware ved hjælp af .boston endelse, vi råde dig til at læse denne artikel og lære at fjerne virus filer og forsøge at afkode .stun krypterede objekter.
.boston Ransom Virus - hvad betyder det gøre
At være en variant af STOP-ransomware familie, som eksisterer i hundredvis af varianter, hvoraf mange er dekrypteres, .boston ransomware er blevet rapporteret til at droppe en eller flere eksekverbare filer i %AppData% Windows-mappen.
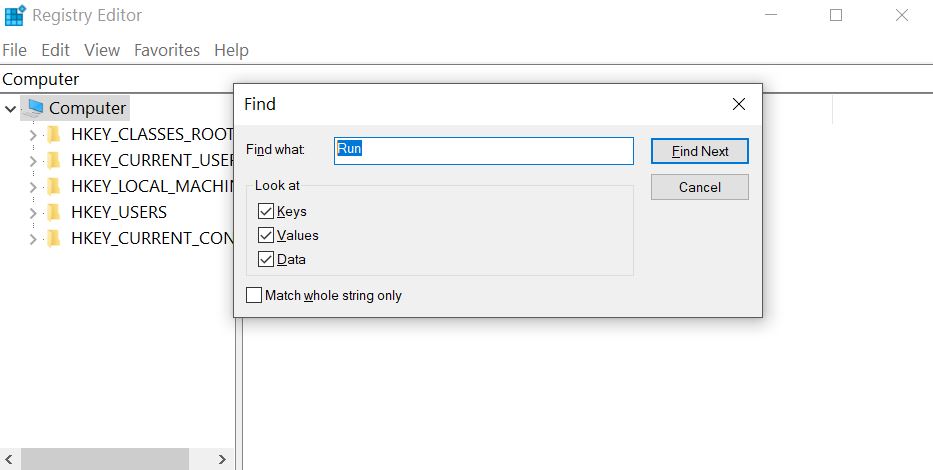
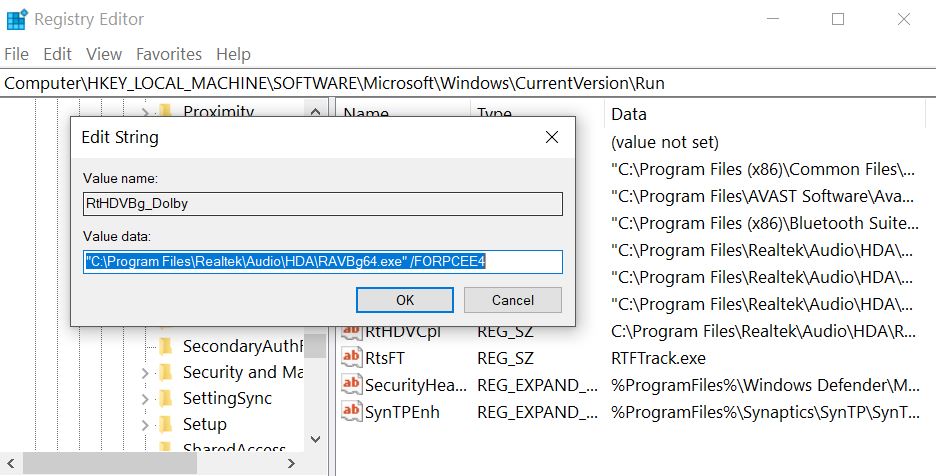
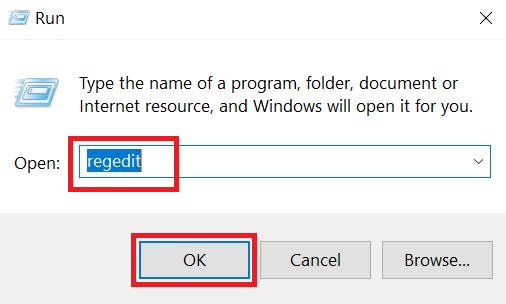
Efter at gøre så, virus kan ændre Windows registreringsdatabasen de, mere specifikt Shell sub-nøgle med følgende placering:
- HKLM / Software / Microsoft / Windows NT / CurrentVersion / Winlogon / Shell
Derefter, den .boston virus kan også ændre nøglen Kør i registreringsdatabasen for at køre den eksekverbare fil(med) i% AppData% mappe. Det centrale er med følgende sti:
- HKLM / Software / Microsoft / Windows / CurrentVersion / Run /
Dette kan resultere i virus-filen opstart ved siden af Windows opstart processen.
STOP ransomware falder også en løsesum notat fil med en løsesum budskab og placerer den et sted let at finde. Derefter, .boston ransomware virus kan vedhæfte filer med en udvidelse af samme navn.
Efter krypteringen af STOP-ransomware har afsluttet, virus kan også slette VSS (øjebliksbilleder) på den inficerede computer for at forhindre ofre fra genoprette deres filer via disse sikkerhedskopier.
STOP .boston Ransomware - Hvordan klarede jeg mig inficeret
Infektionsprocessen af STOP ransomware udføres primært via spammed e-mails, der har vildledende beskeder indlejret i dem. Sådanne meddelelser kan foregive at blive sendt fra tjenester som PayPal, USPS, FedEx og andre. De kan indeholde vedhæftede filer, der foregiver at være fakturaer og andre falske type filer. Andre social engineering teknikker omfatter:
- Falske knapper og billeder, som om de e-mails sendes fra en social media websted, ligesom LinkedIn.
- Falske PayPal links.
- Links til Google Drive og falske e-mails, der ser det samme, som hvis de sendes fra Google.
Andre infektion værktøjer kan også omfatte brugen af torrent websteder og andre tredjeparts websteder til at uploade falske opdateringer, falske installatører samt andre svigagtige eksekverbare.
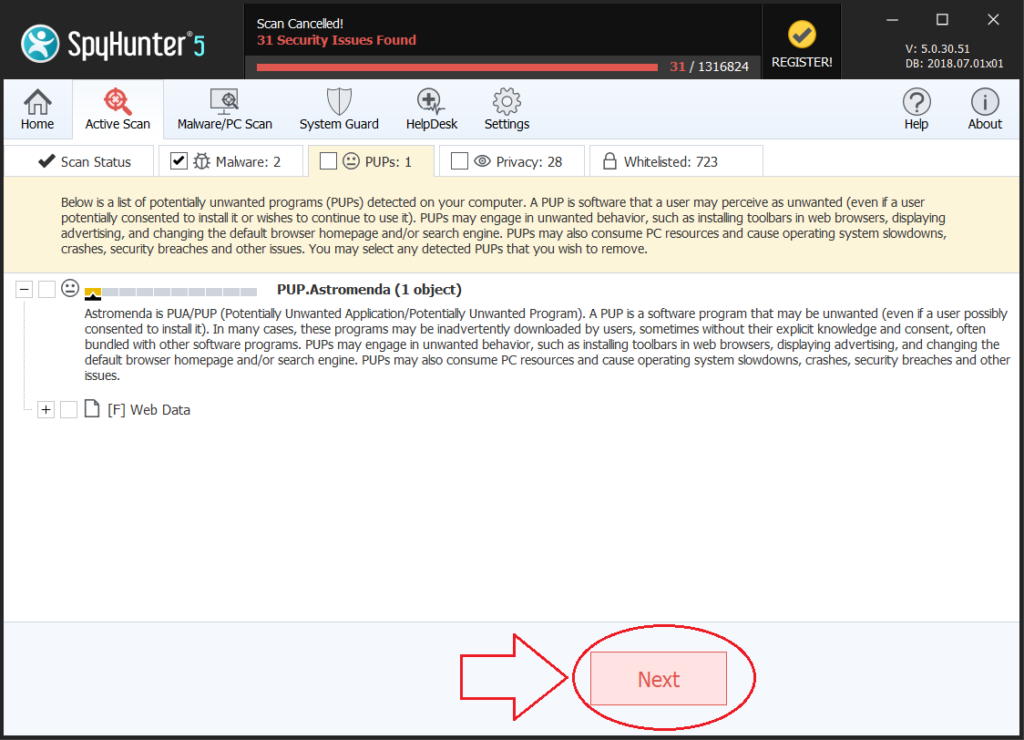
Fjern STOP .boston Ransomware og Get krypterede filer Tilbage
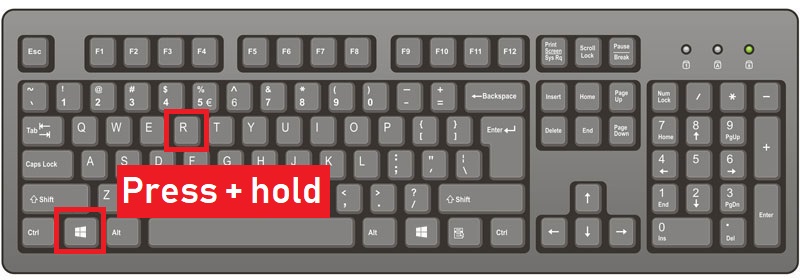
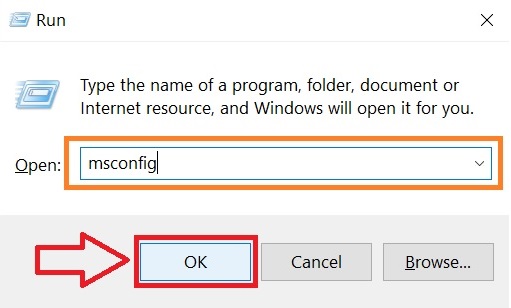
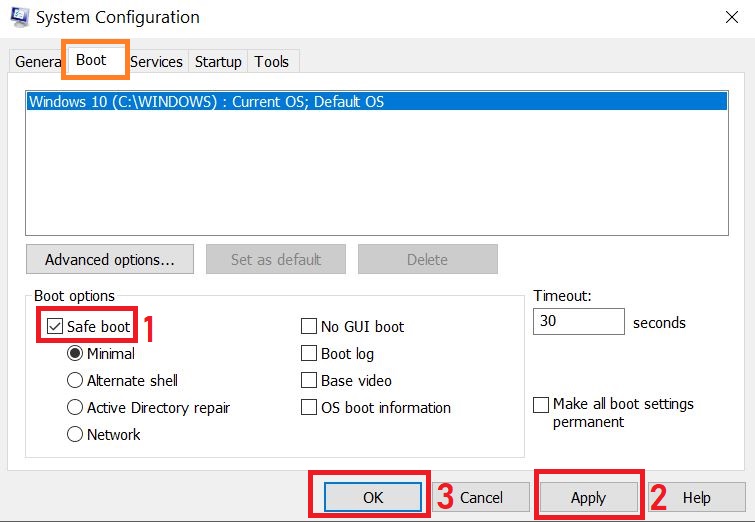
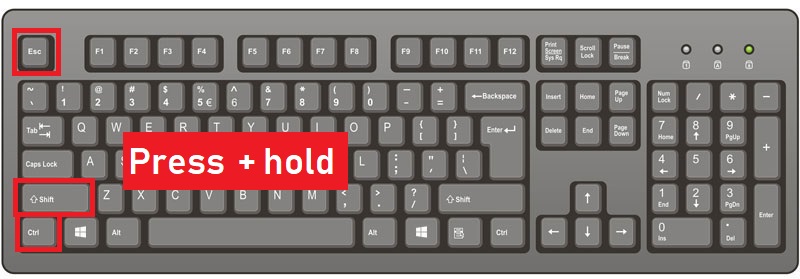
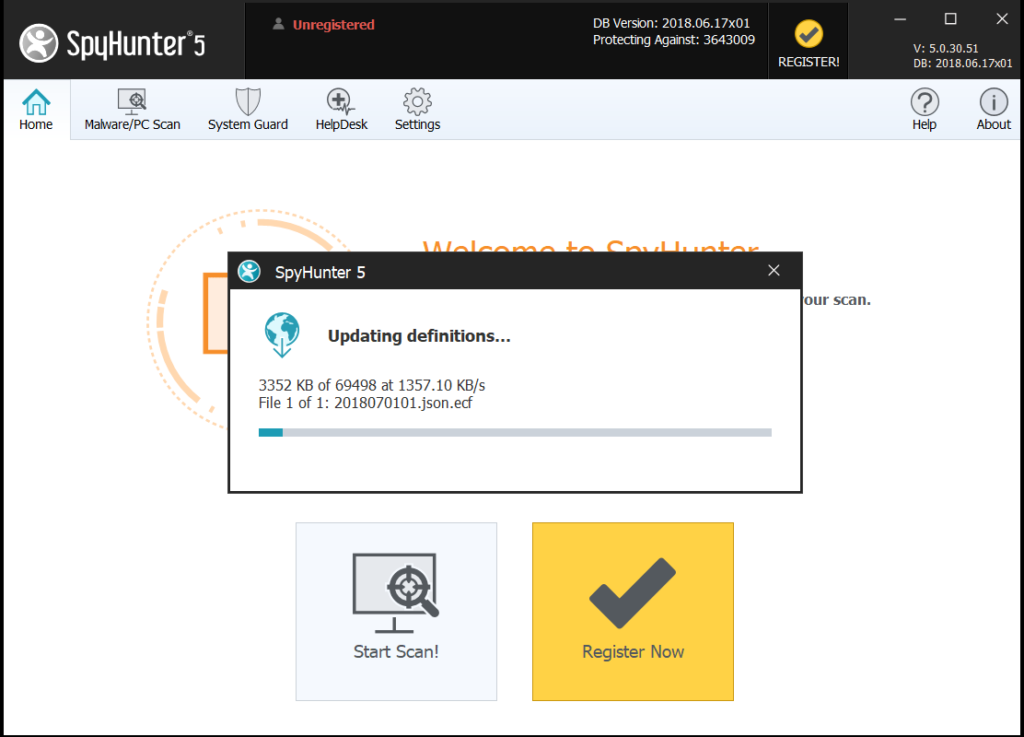
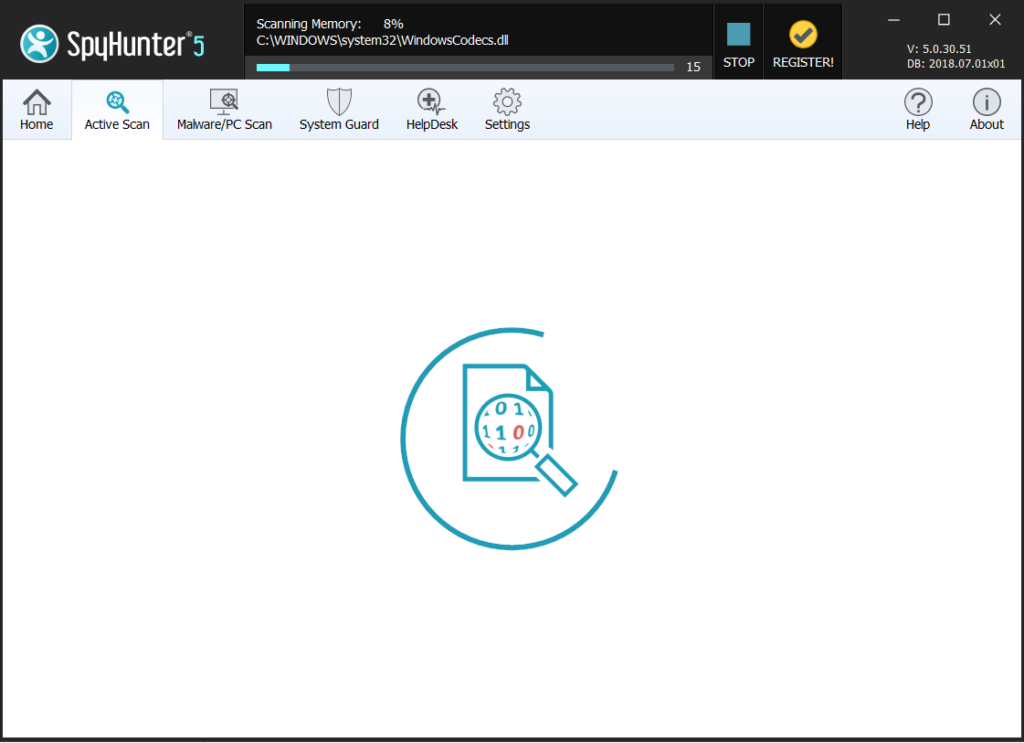
Til fjernelse af den .boston variant af STOP ransomware, anbefalinger er at fokusere på følgende fjernelse instruktioner nedenfor og starte computeren i fejlsikret tilstand. I tilfælde manuel fjernelse i nedenstående instruktioner ikke arbejde for dig, sikkerhedseksperter anbefaler at downloade et stærkt anti-malware værktøj, der vil hurtigt fjerne .boston ransomware og beskytte din computer i fremtiden også. Hvis du ønsker at gendanne filer krypteret af STOP, vi har tilbudt flere forslag nedenfor, der kan være i stand til at hjælpe med dette emne.
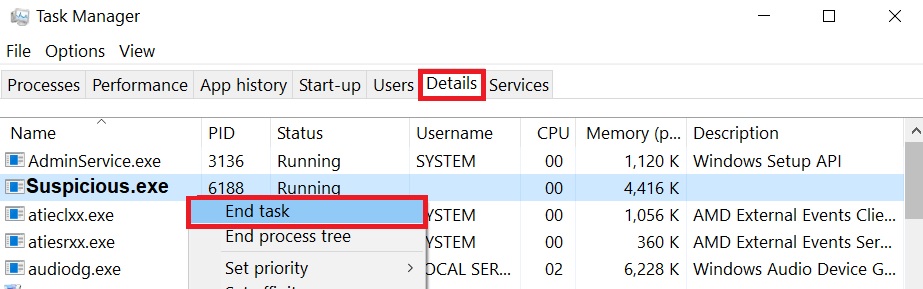
Klargøring før fjernelse af .boston filer Ransomware: 1.Sørg for at sikkerhedskopiere dine filer. 2.Sørg for at have denne vejledning side altid åben, så du kan følge trinene. 3.Vær tålmodig, da fjernelsen kan tage lidt tid. Step 1: Genstart computeren i fejlsikret tilstand: Step 2: Klip .boston Filer Ransomware i Task Manager