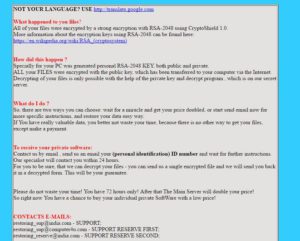
 A virus using the .cryptoshield file extension and imitating CryptoWall has appeared out into the open, infecting multiple computer systems and encrypting their files with RSA-2048 encryption algorithm. This type of ransomware threat also drops a note # RESTORING FILES #.html where it thoroughly requests the vicitms to pay a hefty ransom fee, by contacting an e-mail address. If you have been infected by CryptoShield ransomware, recommendations are to remove it immediately. Keep reading this article to learn how to remove .CryptoShield file virus and try to get your files encrypted by it back.
A virus using the .cryptoshield file extension and imitating CryptoWall has appeared out into the open, infecting multiple computer systems and encrypting their files with RSA-2048 encryption algorithm. This type of ransomware threat also drops a note # RESTORING FILES #.html where it thoroughly requests the vicitms to pay a hefty ransom fee, by contacting an e-mail address. If you have been infected by CryptoShield ransomware, recommendations are to remove it immediately. Keep reading this article to learn how to remove .CryptoShield file virus and try to get your files encrypted by it back.
What Does CryptoShield Ransomware Do
CryptoShield Ransomware is a file virus that performs multiple modifications on the computers it infects and renders the files on those computers no longer able to be opened. As soon as it infects a computer, CryptoShield may drop malicious files in the following locations:
%AppData%\Roaming\
The files may be named SmartScreen.exe and a randomly named .tmp type of file.
The CryptoShield ransomware may also perfrom other modifications on the infected machine, such as interfering with the following Windows Registry Sub-key:
What the virus does is that it may create a value to run the “SmartScreen.exe” file every time Windows has started.
But CryptoShield ransomware does not end the terror there. The virus also executes command prompt as an administrator and performs the following commands
net stop vss
bcedit /set {value} Recoveryenabled No
bcedit /set {value} Bootstatuspolicy ignoreallfailures
The CryptoShield ransomware does this to successfully delete any backups and make sure the user cannot stop the encryption.
When it begins to encrypt files, the CryptoShield Ransomware may also perform multiple other activities, amongst which are to cause an error message, prior to encrypting the files. The encryption process leaves the following file types unable to be accessed, a research blog(https://id-ransomware.blogspot.bg/) reports:
The virus also connects to the host 45.76.81.110 and communicates via the following two e-mails:
How Does CryptoShield Ransomware Infect
For the infection of victims by this ransomware virus, multiple methods may be used to spread malicious files. These files are in most cases disguised as legitimate document attachments or other types of files which are sent by e-mail. Accompanying the e-mail are convincing statements to open those attachments, like a deceptive message, saying the user has paid for something without his/her consent. These deceptive tricks usually work on inexperienced users.
Remove CryptoShield Ransomware
For the removal of this ransomware virus, recommendations are to use the instructions we have provided below. For fastest and most efficient removal however, you may want to download and scan your computer with an advanced anti-malware program. It will make sure to protect you in the future as well.
Booting in Safe Mode
For Windows:
1) Hold Windows Key and R
2) A run Window will appear, in it type “msconfig” and hit Enter
3) After the Window appears go to the Boot tab and select Safe Boot
Cut out CryptoShield 1.0 in Task Manager
1) Press CTRL+ESC+SHIFT at the same time.
2) Locate the “Processes” tab.
3) Locate the malicious process of CryptoShield 1.0, and end it’s task by right-clicking on it and clicking on “End Process”
Eliminate CryptoShield 1.0‘s Malicious Registries
For most Windows variants:
1) Hold Windows Button and R.
2) In the “Run” box type “Regedit” and hit “Enter”.
3) Hold CTRL+F keys and type CryptoShield 1.0 or the file name of the malicious executable of the virus which is usually located in %AppData%, %Temp%, %Local%, %Roaming% or %SystemDrive%.
4) After having located malicious registry objects, some of which are usually in the Run and RunOnce subkeys delete them ermanently and restart your computer. Here is how to find and delete keys for different versions.
For Windows 7: Open the Start Menu and in the search type and type regedit –> Open it. –> Hold CTRL + F buttons –> Type CryptoShield 1.0 Virus in the search field.
Win 8/10 users: Start Button –> Choose Run –> type regedit –> Hit Enter -> Press CTRL + F buttons. Type CryptoShield 1.0 in the search field.
Automatic Removal of CryptoShield 1.0
Recover files encrypted by the CryptoShield 1.0 Ransomware.
Method 1: Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Here are the vendors to look for:
- Kaspersky.
- Emsisoft.
- TrendMicro.
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files:
