Ransomware is now one of the most dangerous threats in the cyber space. It will enter your computer uninvited, encrypt important files and keep them hostage until you pay the demanded amount. And all this is performed in a minacious manner.
Cyber crooks behind ransomware viruses earn money easily, quickly and safely especially thanks to notorious viruses like Locky, Zepto and the growing in popularity ransomware-as-a-service (RaaS). Users therefore need to know how to protect themselves before they lose their important data and money. Prevention is better than correction, and is possible only via proper education. This article will shed light on how ransomware spreads out into the open and how to increase the level of protection against it.
How Ransomware Viruses Spread
Cyber crooks use a wide variety of distribution methods to spread their ransomware infections. Some of the most used “cyber-weapons” to infect the average user or corporate PC are:
- Malware obfuscators
- File joiners
- JavaScript files
- Trojan.Droppers
- Exploit Kit
- Spam bots
- Modified malicious USB drives
To spread the virus via these tools, cyber criminals usually mask the name and real purpose of the attached file, thus tricking the users into opening it. But there are also tools that may automatically execute such files, making the infection vulnerable to fail but faster and automated.
Due to the high success rate of ransomware campaigns, cyber criminals have also come up with a whole new business model where they are now offering the so-called ransomware-as-a-service (RaaS). RaaS allows anyone with little technical and malware knowledge to create their own versions of ransomware and receive a percentage of the total ransom amount paid by their victims. RaaS could also be offered at a fixed rate, like the infamous Cerber Ransomware.
How to Protect Your Files from Ransomware
Unfortunately, there is not one single solution against ransomware. Whether it’s about corporate system or a personal computer, a whole set of tools, tricks, behavior and management instructions need to be used. I have decided to split them into several different stages:
Stage 1: Data Management and Control
Stage 2: Operating System Protection
Stage 3: Management of The Security Behavior
Data Management and Control
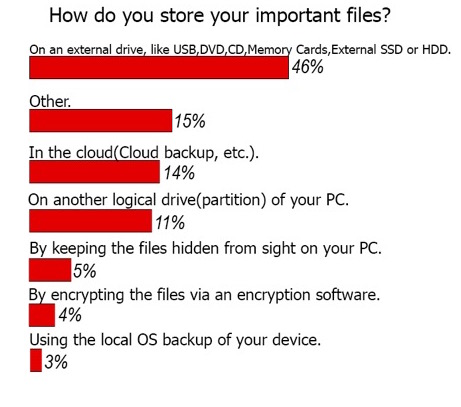
According to a survey conducted by SensorsTechForum, different types of users store files differently, but most of them use an external drive:
If your computer is infected with a ransomware virus that is more sophisticated, it may even be pre-programmed to encrypt the files on your remote drive in case it is connected to it. And that is why you need something that’s more than just a data storage solution. You need a data management system. This system allows the use of all kinds of storage methods, such as:
- External hard disk drives
- External solid state drives
- USB Flash Drives
- Memory cards
- Cloud drives and cloud backup software
- Encryption for protection
One question, however, arises and it is, “How will you then control your data?” Because even if you store the data somewhere remotely it may still not be safe. This is why management tools like encrypting the data yourself on the flash drive prevent it from being enciphered by ransom viruses and from prying eyes as well. The key issue with this method is that the data becomes subject to several other risks, like compromising your password for the encrypted files via a malicious keylogger software, for example. Still, however, this method is way more secure than not having it at all.
Operating System Protection
Besides the almost necessary anti-malware software that has a frequently updated real time shield and stops viruses from running, you may want to consider the type of operating system you are using. Since Windows is an “easy-to-work-with” OS, most users tend to choose it, making it the most widespread OS in the world and subject one to computer viruses. Along with it, Android OS is also a main subject to mobile malware, so choose wisely.
Using Mac OS and IOS is a safer option, but they may still let ransomware and malware in, and a good example for this was the Keranger ransomware for Mac users. However, on the bright side, Apple’s operating systems offer cloud backup as well, just in case you lose your data. Another secure choice for you is to try using Ubuntu or other Linux distributions as well. The advantages of the software is that It is free and secure and works on any PC as well. But bear in mind that there is malware for Ubuntu as well and you still need to implement safe data storage practices.
Management of The Security Behavior
Since the key factor when it comes to protecting your data remains human behavior, I have outlined few instructions that should constantly be implemented in order to keep the data safe.
1) Perform regular backup of the files. Automatic cloud backup software is always a good solution as well, since manual backup may take longer.
2) Keep your OS up-to-date. Make sure to have the latest updates installed because some of them may patch an exploit that may prevent ransomware from encrypting your files.
3) Learn how to spot fake e-mails and always check suspicious URLs and e-mail attachments.
4) Install an anti-ransomware program that is focused only on detecting ransomware.
5) Avoid using the Shadow Volume Copies on you computer (vssadmin.exe). Such backup is often deleted by ransomware.
6) Disable Microsoft Office macros.
7) Disable the AutoPlay feature in your OS.
8) Add a URL scanning file extension on your web browser to detect malicious URLs.
9) Always do more than one backup.
10) Make sure to check suspicious USB drives, CD/DVD drives or other external memory carriers on your network before using them.
11) Educate everyone on your network to be cautious.
Conclusion
These tips and methods for protection against ransomware viruses may significantly increase the level of security on your network if implemented correctly. But either way, you should know that there is no such thing as a 100% safe computer and this is why you should have an anti-malware protection on your whole network not just on one device. Because if one of the devices in the network is compromised, there is a risk for each of the devices to be compromised as well.