This post is made in order to show you how you can remove the .moresa files virus of STOP ransomware and how you can restore files, encrypted with the added .moresa file extension.
Yet another variant of STOP ransomware has been detected in the wild, this time using the .moresa file extension. The ransomware, like other variants of STOP aims to encrypt the files on the computers infected by it with the main idea to get the victims to pay ransom in order to get the files to be operational again. The virus gives a deadline of 24 hours for the ransom to be paid in cryptocurrencies and if it is not met, the price increases. If your computer has been infected by the .moresa files virus, we suggest that you read this article to learn more about what it does, how it spreads and how you can remove it and try to restore your files.
| Threat Name | .moresa Ransomware |
| Category | Ransomware virus. |
| Main Activity | Variant of STOP ransomware viruses. Infects the computer after which encrypts important documents and holds them hostage until a ransom is paid. |
| Signs of Presence | Files are encrypted with a .moresa file extension and ransom note is dropped with ransom instructions.. |
| Spread | Via malicious e-mail spam and set of infection tools. |
| Detection+Removal | DOWNLOAD REMOVAL TOOL FOR .moresa Ransomware |
| File Recovery | Download Data Recovery Software, to see how many files encrypted by .moresa Ransomware ransomware you will be able to recover. |
The STOP virus has been spotted in a new variant, this time using the .moresa file extension. It is related to the previous .trosak and .grovas ones. The new STOP ransomware also communicates via email through which it sends a decrypter after the ransom has been paid. In case you are a victim of the new STOP ransomware using the .moresa suffix, we advise you to read this article and learn how to remove the virus files and try to decode .stun encrypted objects.
.moresa Ransom Virus – What Does It Do
Being a variant of the STOP ransomware family, which exists in hundreds of variants, many of which are decryptable, .moresa ransomware has been reported to drop one or more executable files in the %AppData% Windows directory.
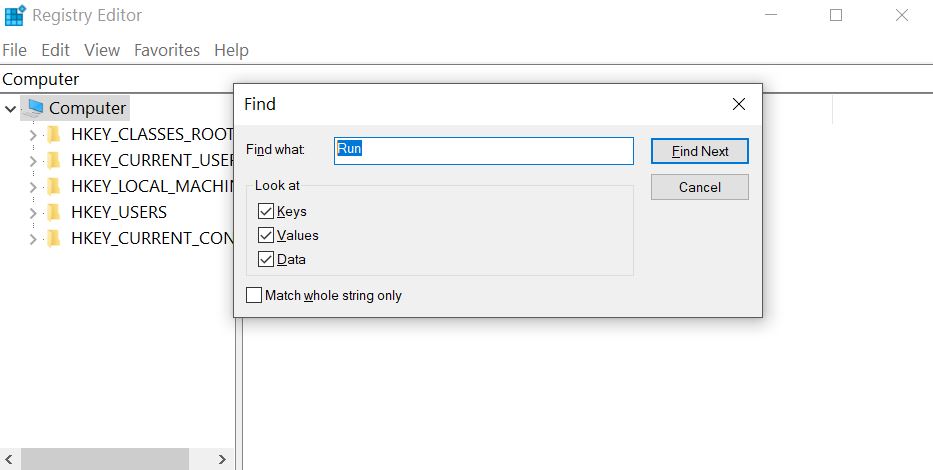
After doing so, the virus may modify the Windows registry entries, more specifically the Shell sub-key with the following location:
- HKLM/Software/Microsoft/WindowsNT/CurrentVersion/Winlogon/Shell
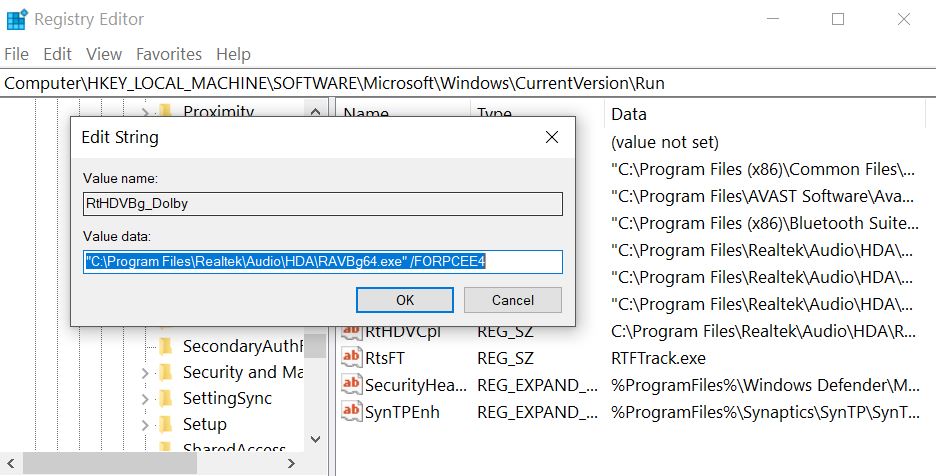
Then, the .moresavirus may also modify the Run registry key to run the executable file(s) in the %AppData% directory. The key is with the following path:
- HKLM/Software/Microsoft/Windows/CurrentVersion/Run/
This may result in the virus file booting alongside the Windows start-up process.
The STOP ransomware also drops a ransom note file with a ransom message and places it somewhere easy to locate. Then, .moresa ransomware virus may attach files with an extension of the same name.
After the encryption process of STOP ransomware has completed, the virus may also delete the VSS (shadow copies) on the infected computer in order to prevent victims from restoring their files via these backups.
STOP .moresa Ransomware – How Did I Get Infected
The infection process of STOP ransomware is conducted primarily via spammed e-mails that have deceptive messages embedded within them. Such messages may pretend to be sent from services such as PayPal, USPS, FedEx and others. They may contain attachments that pretend to be invoices and other fake type of files. Other social engineering techniques include:
- Fake buttons and pictures as if the e-mails are sent from a social media site, like LinkedIn.
- Fraudulent PayPal links.
- Links to GoogleDrive and fake e-mails that look the same as if they are sent from Google.
Other infection tools may also include the usage of torrent websites and other third-party sites to upload fake updates, fake installers as well as other fraudulent executables.
Remove STOP .moresa Ransomware and Get Encrypted Files Back
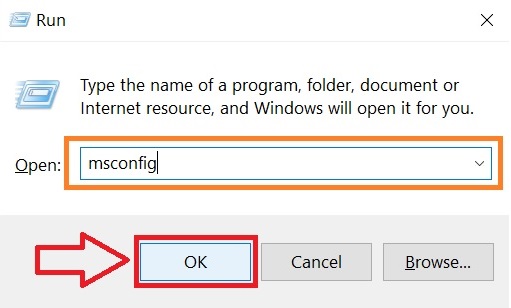
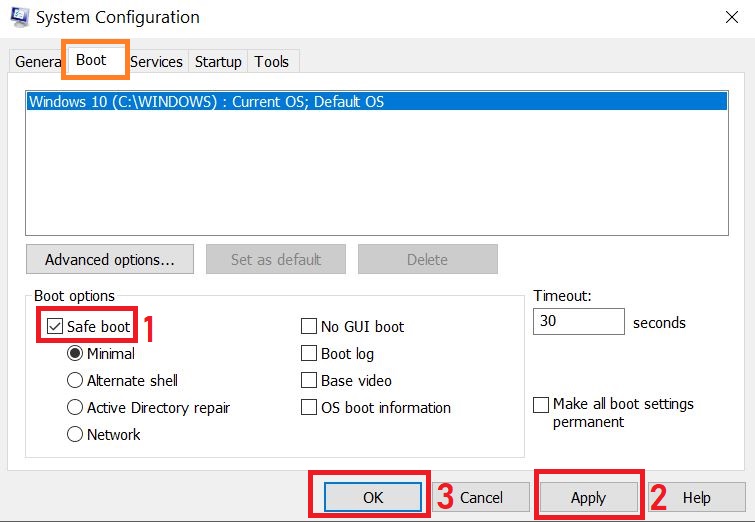
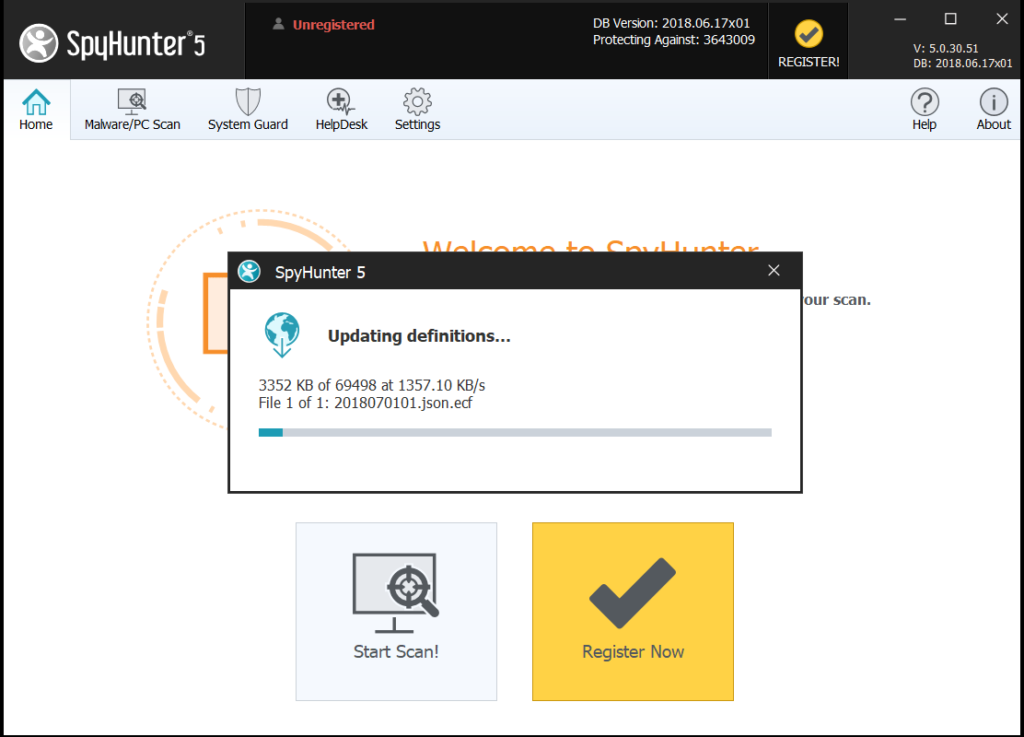
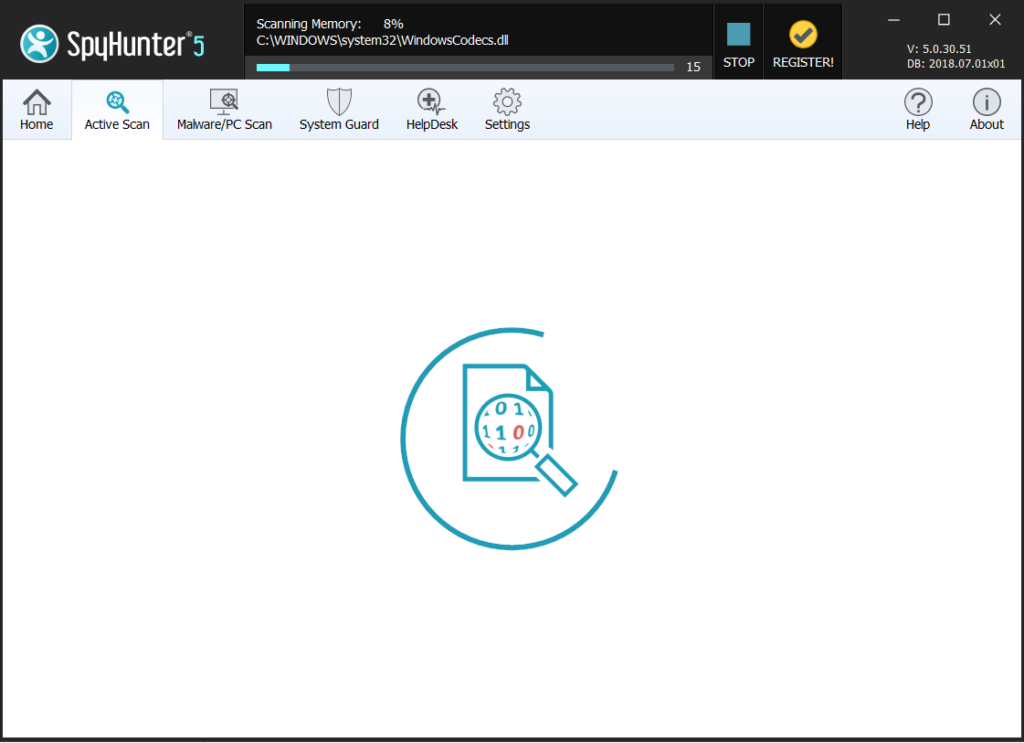
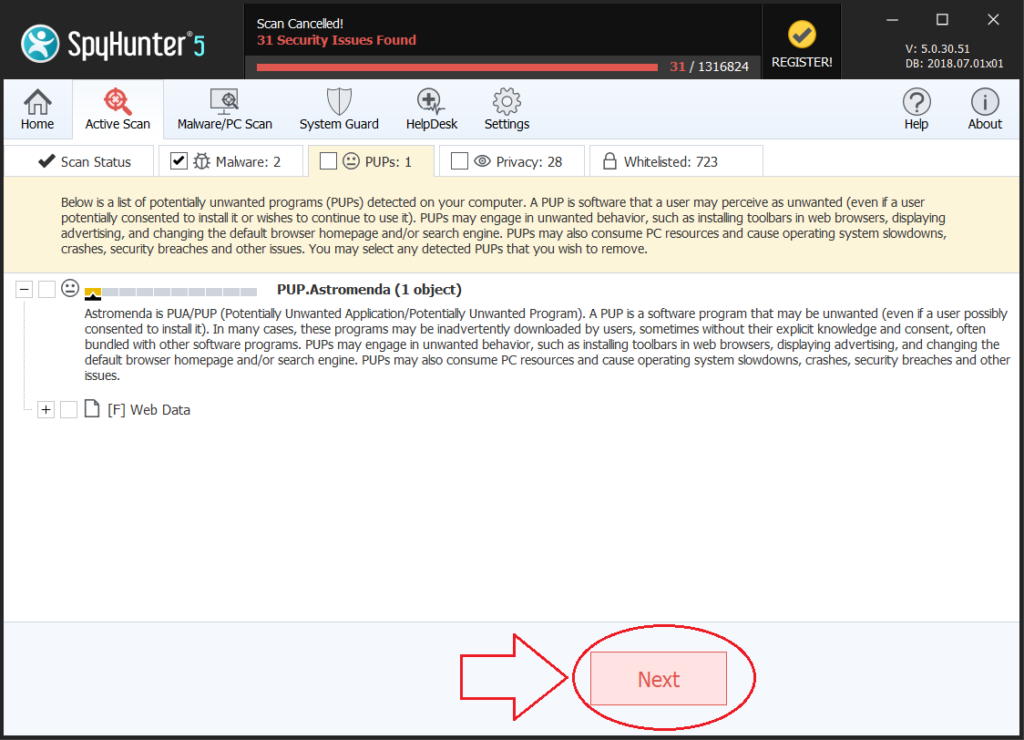
For the removal of the .moresa variant of STOP ransomware, recommendations are to focus on following the removal instructions below and boot your computer in Safe Mode. In case manual removal in the instructions below do not work for you, security professionals recommend downloading a powerful anti-malware tool that will quickly remove .moresa ransomware and protect your computer in the future as well. If you want to restore files encrypted by STOP, we have offered several suggestions below that may be able to assist with this issue.
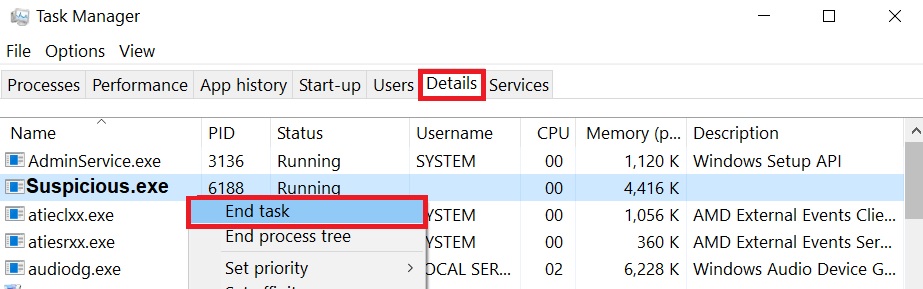
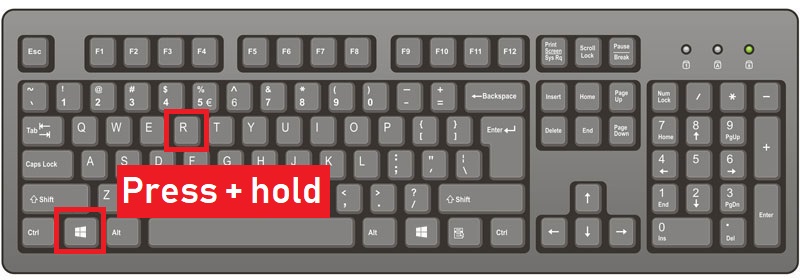
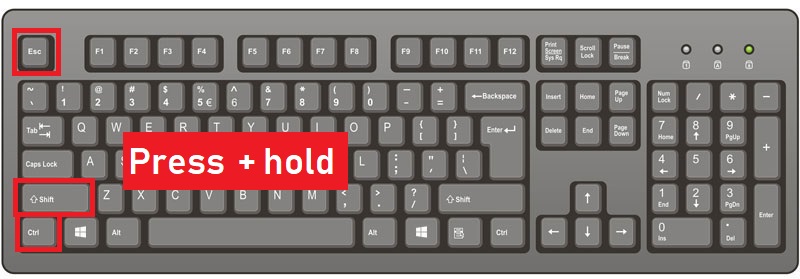
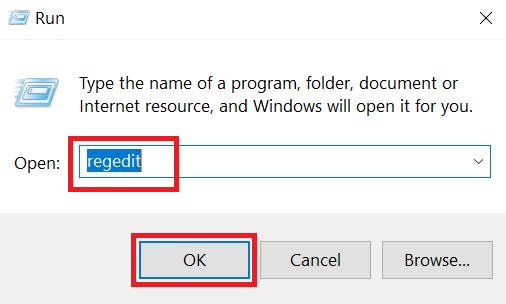
Preparation before removal of .moresa Ransomware: 1.Make sure to backup your files. 2.Make sure to have this instructions page always open so that you can follow the steps. 3.Be patient as the removal may take some time. Step 1: Reboot your computer in Safe Mode: Step 2: Cut out .moresa Ransomware in Task Manager