Read this article in order to learn how to remove the latest Locky ransomware variant and how to restore .ykcol encrypted files that have been encrypted by it on your computer.
Locky ransomware is back following a successful infection campaign with it’s previous variant. Unlike the .lukitus file extension, used by the previous Locky iteration, this virus now uses the .ykcol (Locky in reverse) file extension. In addition to this, it has several other changes as well, such as lower ransom amount which the cyber-criminals ask from the vsictims of the virus to pay in order to get their files back. Besides this, the new virus also has some minor changes in it’s ransom note and it’s code. If you have been infected by the .ykcol files virus, we strongly suggest not to pay the ransom and to read the blog post below.
| Threat Name | .ykcol Files Virus |
| Category | Ransomware virus. |
| Main Activity | A new variant of the notorious Locky ransomware. Infects the computer after which encrypts important documents and holds them hostage until a ransom is paid. |
| Signs of Presence | Files are encrypted with the .ykcol file extension. |
| Spread | Via malicious e-mail spam and set of infection tools. |
| Detection+Removal | DOWNLOAD REMOVAL TOOL FOR .ykcol Files Virus |
| File Recovery | Download Data Recovery Software, to see how many files encrypted by .ykcol Files Virus ransomware you will be able to recover. |
Locky .ykcol File Virus – How Does It Infect
The creators of Locky ransomware have stuck to the well-known method of spreading the malware, using spam campaigns to replicate it via e-mail. E-mail messages used by the creators of Locky are considered to be the primary threat to users. The e-mails are reported to contain the following type of files that cause the infection:
- .xls file with a random name such as _2234_214252_
- .js and .wsf (JavaScript)
- .hta, .html, .htm (lead to malicious web hosts)
- .vbs (Visual Basic Script) that causes direct infection
These files are usually stored in archives such as .zip or .rar archives that have similar or the same names as the attachments to avoid detection by e-mail providers’ security. The latest Locky variant using the .ykcol file extension has been reported to use a file, named as “Ykcol.htm” or an “.xls” file with random numbers as a name.
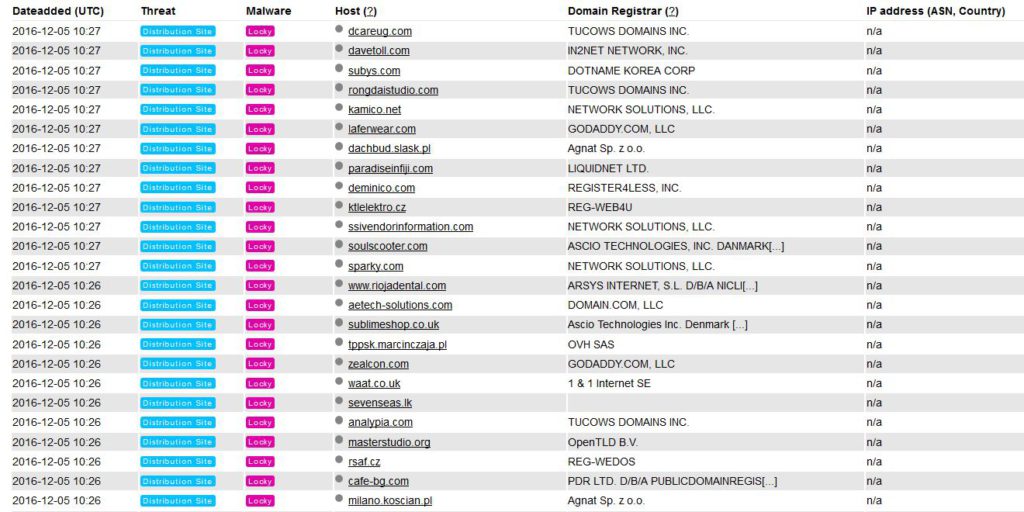
Once the user clicks on the file, obfuscated actions may immediately connect to one of the many Locky distribution websites:
After having connected to those webistes, the malware may download an obfuscated payload in crucial Windows folders, like the previously detected by Hybrid-Analysis .exe file containing Locky, located in %Temp%.
So far it is reported to be pre-configured in order to encrypt file types that are the same as the previous versions, like the .aesir, .shit, .zzzzz Locky variants. This includes encrypting most often met file formats of:
- Images.
- Videos.
- Virtual drives.
- Database files.
- Files that are associated with Microsoft Word.
- Microsoft Excel files.
- Files associated with Adobe Reader.
- Files that have something In common with most virtual drive players.
Once Locky .ykcol infects those files, the virus begins to replace the code of those files with custom symbols belonging to a very strong encryption algorithm, called AES-128. These files then generate unique decryption key. After this pass, the virus makes another pass using the also very advanced RSA-2048 encryption algorithm with the one and only purpose of generating unique RSA public and private keys. The virus then may either connect to the c2 servers and send the decryption keys on them or keep them on the infected computer for a specific Locky Decryptor which is sold for BTC. Encrypted files look like the below mentioned example:
After encryption by this Locky ransomware virus has completed, the virus begins to immediately display a “Read Me” .htm file that has the following instructions:
“All of your files are encrypted with RSA-2048 and AES-128 ciphers.
More information about the RSA and AES can be found here:
{links to Wikipedia}
Decrypting of your files is only possible with the private key and decrypt program, which is on our secret servers. To receive your private key follow one of the links:
If all of this addresses are not available, follow these steps:
1. Download and install tor Browser: https://www.torproject.org/download/download-easy.html
2. After a successful installation, run the browser and wait for initialization.
3. Type in the address bar: {unique Locky URL}
4. Follow the instructions on the site.”
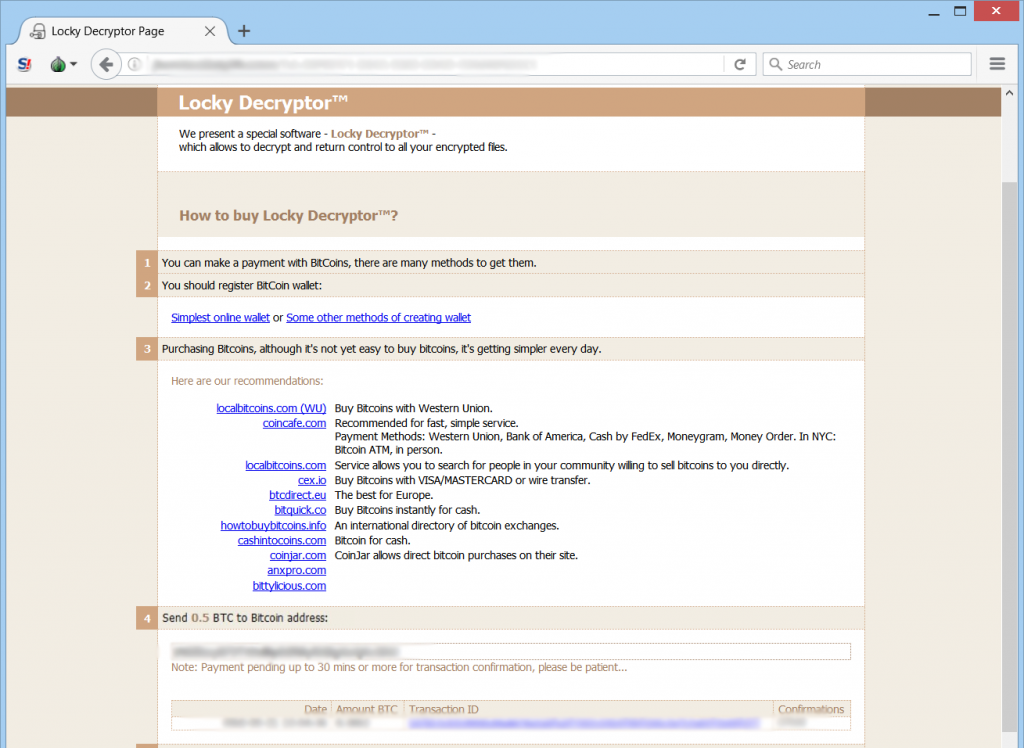
The instructions on the website are the standard Locky Decryptor instructions which are used in most of it’s variants – a web page with instructions on how to buy BitCoin and pay for a “Locky Decryptor”:
In addition to this the files YKCOL-{RAND}.htm and shtefans1.spe are also added on the infected computer amongst other files.
How to Remove Locky .ykcol Virus and Restore My Files
In case you feel like not paying any ransom to cyber-criminals that may or may not get your files back, we strongly advise you to firstly remove Locky from your computer after which focus on trying to restore your files using alternative methods. For the safest and best removal of Locky .ykcol ransomware experts strongly advise using an advanced anti-malware tool that will automatically take care of all the objects Locky ransomware has interfered with.
We advise you to carefully follow the below mentioned steps in order to remove Locky .ykcol properly:
Booting in Safe Mode
For Windows:
1) Hold Windows Key and R
2) A run Window will appear, in it type “msconfig” and hit Enter
3) After the Window appears go to the Boot tab and select Safe Boot
Cut out .ykcol Files Virus in Task Manager
1) Press CTRL+ESC+SHIFT at the same time.
2) Locate the “Processes” tab.
3) Locate the malicious process of .ykcol Files Virus, and end it’s task by right-clicking on it and clicking on “End Process”
Eliminate .ykcol Files Virus‘s Malicious Registries
For most Windows variants:
1) Hold Windows Button and R.
2) In the “Run” box type “Regedit” and hit “Enter”.
3) Hold CTRL+F keys and type .ykcol Files Virus or the file name of the malicious executable of the virus which is usually located in %AppData%, %Temp%, %Local%, %Roaming% or %SystemDrive%.
4) After having located malicious registry objects, some of which are usually in the Run and RunOnce subkeys delete them ermanently and restart your computer. Here is how to find and delete keys for different versions.
For Windows 7: Open the Start Menu and in the search type and type regedit –> Open it. –> Hold CTRL + F buttons –> Type .ykcol Files Virus Virus in the search field.
Win 8/10 users: Start Button –> Choose Run –> type regedit –> Hit Enter -> Press CTRL + F buttons. Type .ykcol Files Virus in the search field.
Automatic Removal of .ykcol Files Virus
Recover files encrypted by the .ykcol Files Virus Ransomware.
Method 1: Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Here are the vendors to look for:
- Kaspersky.
- Emsisoft.
- TrendMicro.
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files: