 This article has been made in order to explain what exactly is the Scarab ransomware infection and what are .xtbl files plus how to open them. It also explains how to remove the Scarab ransomware virus effectively from your computer system and how to try and recover .xtbl encrypted files without having to pay the ransom
This article has been made in order to explain what exactly is the Scarab ransomware infection and what are .xtbl files plus how to open them. It also explains how to remove the Scarab ransomware virus effectively from your computer system and how to try and recover .xtbl encrypted files without having to pay the ransom
A new version of the notorious Scarab ransomware infection has been detected by security researchers. The virus is from the “cryptovirus” type and it’s primary purpose is to attach the documents, videos, images and other important files on your computer system and render them no longer able to be opened. This may effectively result in the malware being able to be set it’s unique .xtbl file extension to the encoded files, which was also seen with some other viruses we have detected in the past. After the encryption by this ransomware has completed, Scarab makes your files no longer able to be opened until you pay ransom to get them back. The files cannot be directly decrypted and the only way to recover them seems to be the ransom, but do not despair because in this blog post, we have created several methods that can help you to try and recover your files without paying ransom. If you want to remove Scarab Ransomware from your computer and restore .xtbl encrypted files, we advise you to read this article completely.
| Threat Name | .xtbl Files Virus |
| Category | Ransomware virus. |
| Main Activity | New Scarab ransomware variant. Infects the computer after which encrypts important documents and holds them hostage until a ransom is paid. |
| Signs of Presence | Files are encrypted with the .xtbl file extension. |
| Spread | Via malicious e-mail spam and set of infection tools. |
| Detection+Removal | DOWNLOAD REMOVAL TOOL FOR .xtbl Files Virus |
| File Recovery | Download Data Recovery Software, to see how many files encrypted by .xtbl Files Virus ransomware you will be able to recover. |
The Scarab has been spotted in a third variant, this time using the .xtbl file extension, completely unrelated to the previous .dharma and .wallet ones. The new Dharma ransomware also communicates via an e-mail through which it sends a decryptor after the ransom has been paid.
.xtbl Ransom Virus – What Does It Do
Being a variant of the Scarab ransomware family, which exists in several variants, many of which are undecryptable, Scarab .xtbl ransomware has been reported to drop one or more executable files in the %AppData% Windows directory.
After doing so, the virus may modify the Windows registry entries, more specifically the Shell sub-key with the following location:
- HKLM/Software/Microsoft/WindowsNT/CurrentVersion/Winlogon/Shell
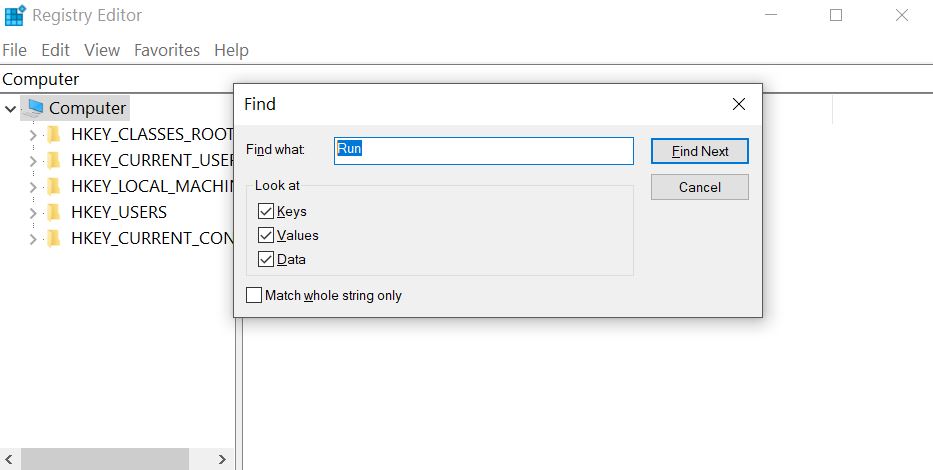
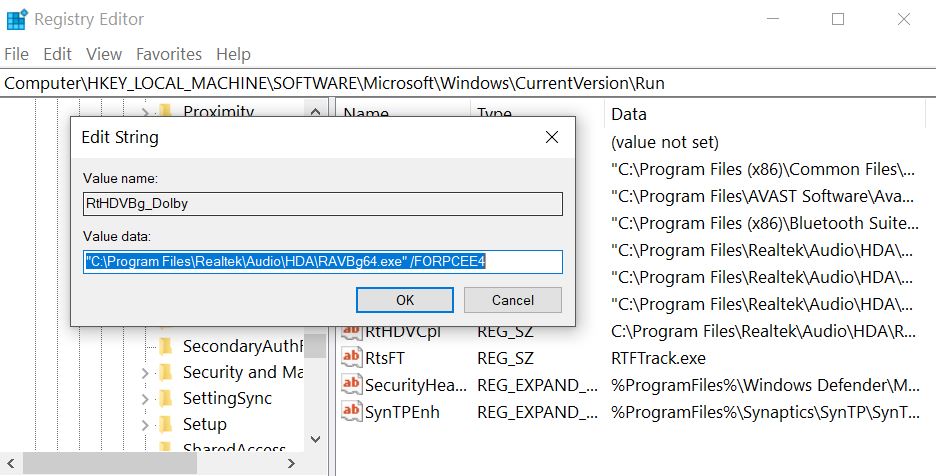
Then, the virus may also modify the Run registry key to run the executable file(s) in the %AppData% directory. The key is with the following path:
- HKLM/Software/Microsoft/Windows/CurrentVersion/Run/
This may result in the Scarab virus file booting alongside the Windows start-up process.
The Scarab ransomware also drops a ransom note file with a ransom message and places it somewhere easy to locate. The ransom note which is dropped by this virus Is named IF YOU WANT TO GET ALL YOUR FILES BACK, PLEASE READ THIS.TXT and has the following contents:
IF YOU WANT TO GET ALL YOUR FILES BACK, PLEASE READ THIS
________________________________________________________________________________________________I
email – [email protected]
Your files are now encrypted!
-BEGIN PERSONAL IDENTIFIER-
-END PERSONAL IDENTIFIER-
AII your files have been encrypted due to a security problem with your PC.
Now you should send us email with your personal identifier.
This email will be as confirmation you are ready to pay for decryption key.
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us.
After payment we will send you the decryption too] that will decrypt all your files.
Contact us using this email address: joxe1@cock.;i
Free decryption as guarantee!
Before paying you can send us up to 2 files for free decryption.
The total size of files must be less than 1Mb (non archived), and files should not contain
valuable information (databases, backups, large excel sheets, etc.).
_ . _ I
How to obtain Bitco1ns?
* The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click I
‘Buy bitcoins’, and select the seller by payment method and price: I
httpszflfllocalbitcoins.comflbuy_bitcoins I
* AIso you can find other places to buy Bitcoins and beginners guide here: I
httpzfiflwmw.coindesk.comflinformationflow-can-i-buy-bitcoins I
I I
I________________________________________________________________________________________________I
I _ I
I Attention! I
I I
I * Do not rename encrypted files. I
I * Do not try to decrypt your data using third party software, it may cause permanent data loss. I
I * Decryption of your files with the he p of third parties may cause increased price I
l (they add their fee to our) or you can become a victim of a scam. I
I I
I________________________________________________________________________________________________I
emaiI – [email protected]
The .xtbl files virus may attack often used files on the victim’s computer, such as:
- Documents.
- Archives.
- Videos.
- Images.
- Virtual Drive type of files.
- Other often used files of programs.
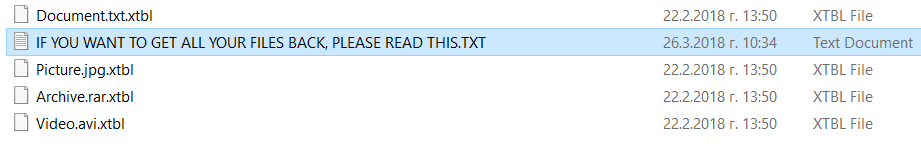
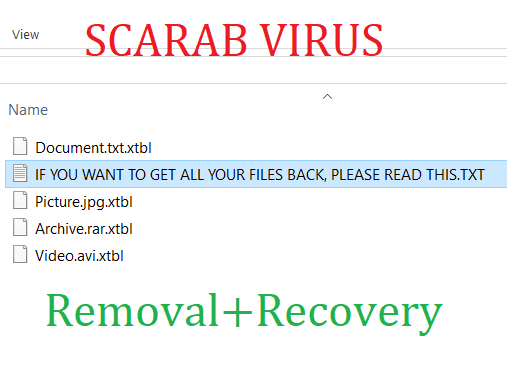
After Scarab ransomware encrypts the files, the virus leaves the files no longer able to be opened and appends the file extension .xtbl to each encrypted file. The files begin to look like the following:
After the encryption process of Dharma ransomware has completed, the virus may also delete the VSS (shadow copies) on the infected computer in order to prevent victims from restoring their files via these backups.
Scarab .xtbl Files Ransomware – How Did I Get Infected
The infection process of Scarab .xtbl file ransomware is conducted primarily via spammed e-mails that have deceptive messages embedded within them. Such messages may pretend to be sent from services such as PayPal, USPS, FedEx and others. They may contain attachments that pretend to be invoices and other fake type of files. Other social engineering techniques include:
- Fake buttons and pictures as if the e-mails are sent from a social media site, like LinkedIn.
- Fraudulent PayPal links.
- Links to GoogleDrive and fake e-mails that look the same as if they are sent from Google.
Other infection tools may also include the usage of torrent websites and other third-party sites to upload fake updates, fake installers as well as other fraudulent executables.
Remove Scarab .xtbl Ransomware and Get Encrypted Files Back
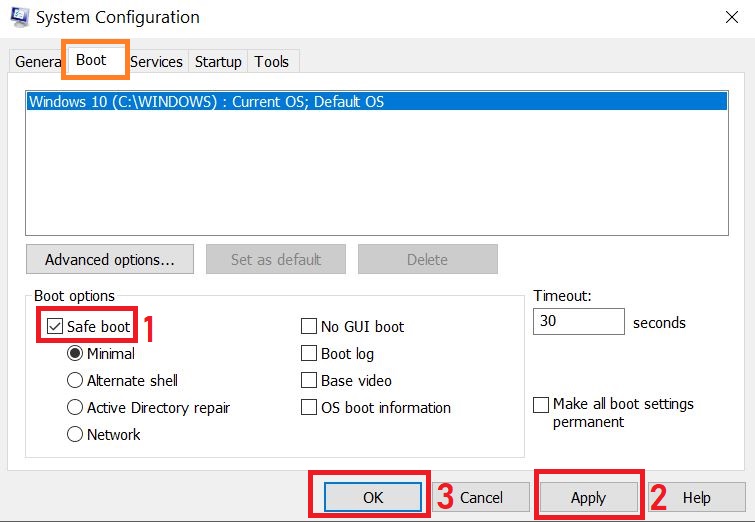
For the removal of the .xtbl variant of Scarab ransomware, recommendations are to focus on following the removal instructions below and boot your computer in Safe Mode to isolate the threat and manually remove it. But in case manual removal in the instructions below do not work for you do not boot in safe mode and follow the advise of security professionals who always recommend downloading a powerful anti-malware tool that will quickly remove Scarab .xtbl ransomware and protect your computer in the future as well. If you want to restore files encrypted by Scarab, we have offered several backup suggestions below that may be indirectly able to assist with this issue. They may not be 100% able to recover all of your files, but we have received feedback from ransomware victims who we able to recover half and even most of their decrypted files.
To REMOVE and TRY TO RESTORE files, please follow the instructions underneath
Preparation before removal of .xtbl Files Virus:
1.Make sure to backup your files.
2.Make sure to have this instructions page always open so that you can follow the steps.
3.Be patient as the removal may take some time.
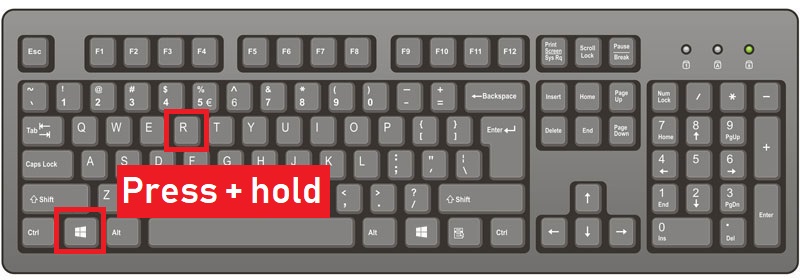
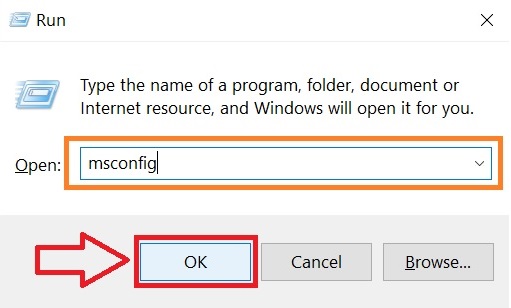
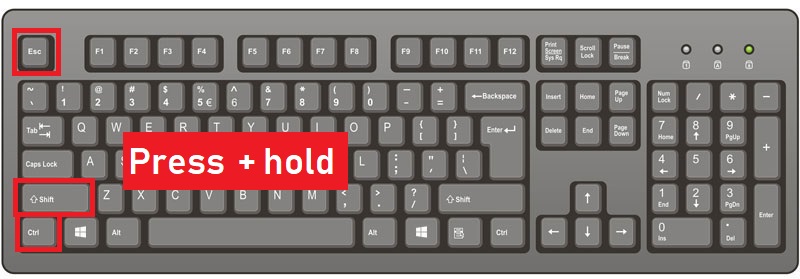
Step 1: Reboot your computer in Safe Mode:
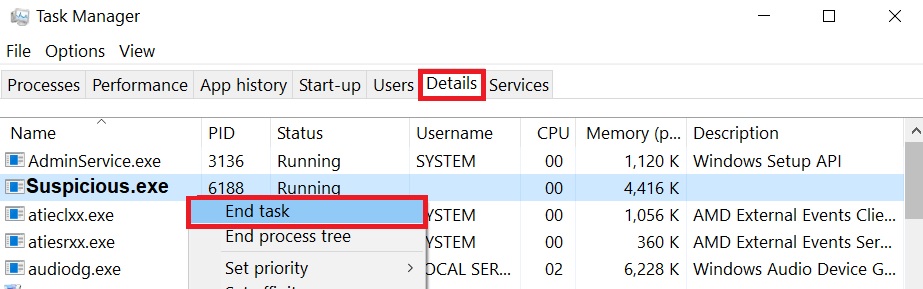
Step 2: Cut out .xtbl Files Virus in Task Manager
Step 3: Eliminate .xtbl Files Virus‘s Malicious Registries.
For most Windows variants:
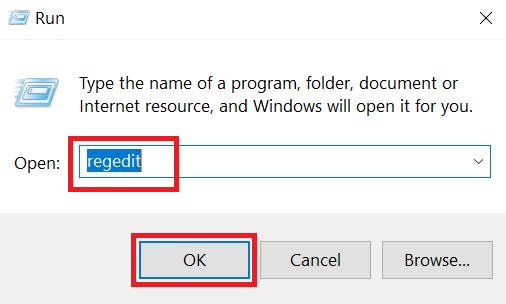
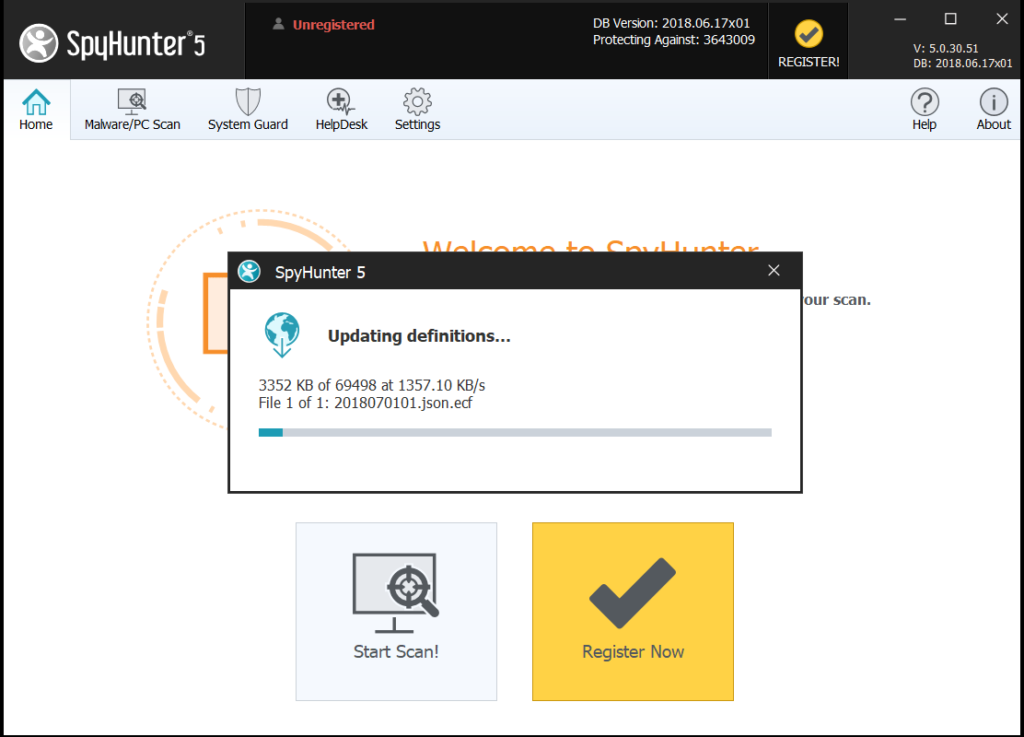
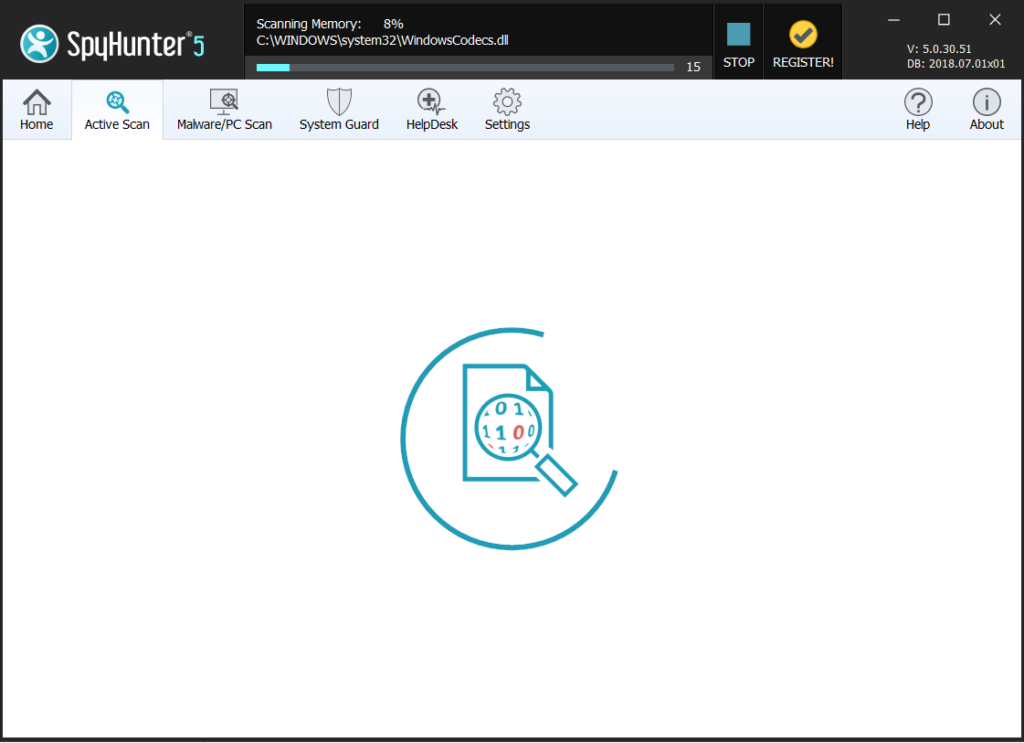
Step 4: Scan for and remove all virus files, related to .xtbl Files Virus and secure your system.
If you are in Safe Mode, boot back into normal mode and follow the steps below
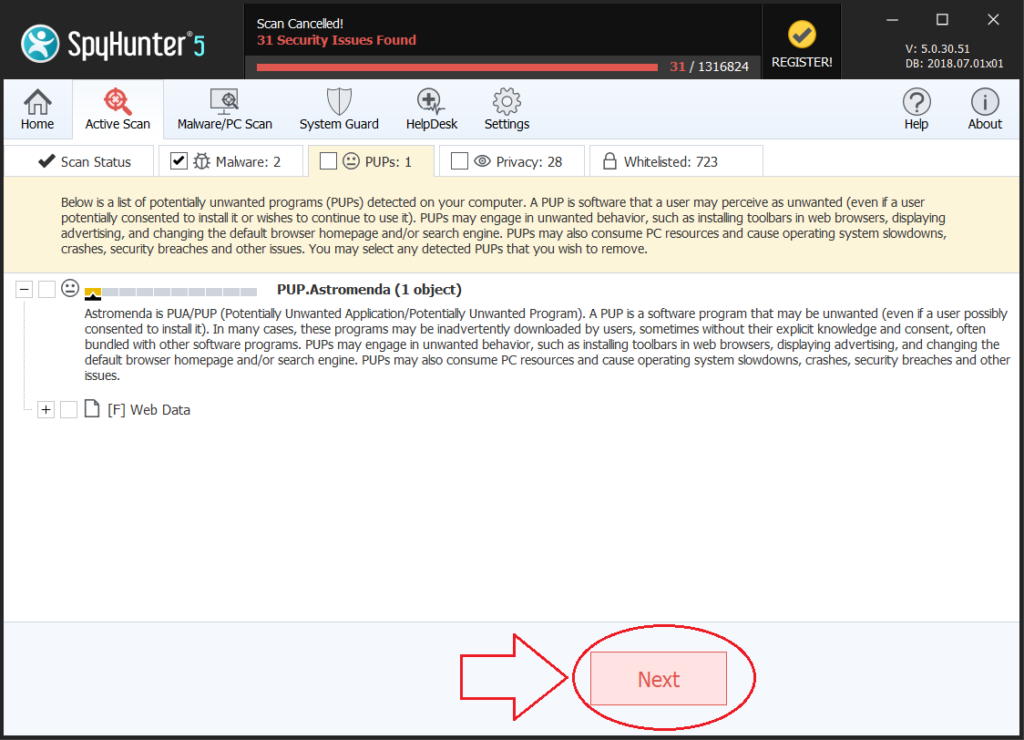
It is advisable to run a free scan before committing to the full version. You should make sure that the malware is detected by SpyHunter first.
Step 5:Recover files encrypted by the .xtbl Files Virus Ransomware.
Method 1: Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Most of the currently available decryptors for ransomware viruses can be seen if you visit the NoMoreRansom project – a project that is the result of combined efforts of researchers worldwide to create decryption software for all ransomware viruses. Simply go there by clicking on the following LINK and find your ransomware version decrypter and try it, but always remember to do a BACKUP first.
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files: