Fiesta exploit kit’s authors have a new payload to deliver to their victims. Instead of crypto-malware and browser plug-ins, they are now using a rogue antivirus program that runs a fake system scan and tricks users into buying the full version of the product in order to remove non-existent threats.
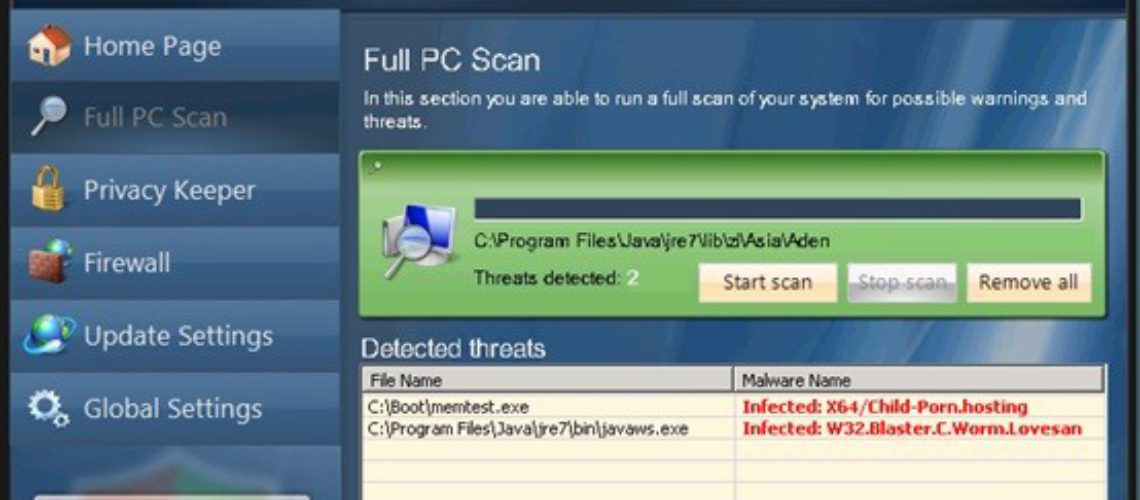
The fake AV tool is dubbed Antivirus Pro 2015 and blocks certain Windows tools and similar software capable of deactivating it.
Users in the US, Australia and Japan Most Targeted
Trend Micro specialists report that the cyber crooks have started using the new payload after March 19. In their previous attacks, the hackers relied on the TeslaCrypt malware that is known for its file-encrypting capabilities. What makes the threat even more severe is the fact that it also deletes the Shadow Volume copies.
TeslaCrypt affects games like World of Warcraft, Call of Duty, WarCraft 3, Minecraft, Assassin’s Creed, and others.
So far, experts have not established the reason for the payload switch.
The most targeted countries, according to Trend Micro’s research are:
- the USA – 36.9%
- Japan – 15.73%
- Australia – 11.9%
Update Your Software to Protect the System
Rogue security solutions like Antivirus Pro 2015 use scare tactics to trick users into purchasing the product. They display a variety of security notifications alerting the user about non-existent threats and multiple viruses supposedly detected on the compromised machine. The advertised AV tool is allegedly going to clean the system and keep it safe in the future.
Naturally, the full version of the rogue software comes at a price ($64), and the user is required to enter sensitive data on the online payment page.
Many legitimate antivirus products (including free versions) can detect Antivirus Pro 2015. Experts recommend using one of them and keeping it updated.