What is the cizer Virus malware? How to open files, encrypted by cizer Virus virus? How to remove cizer Virus ransomware and try to restore files?
cizer Virus is a unique file-encoding Trojan that may make your whole PC unusable. The developers of this ransomware, which most likely use 256-bit AES encryption to modify all personal data of the user. If this operation is not interrupted, you may lose access to all of your Word documents, Excel tables, PowerPoint presentations, family photos, work-related files, music, videos, databases, and so on. What makes cizer Virus one-of-a-kind is the fact that it pretends to be a legitimate program, thus encouraging the unsuspecting user to install it willingly. The irony is that when this ransomware encrypts the machine, the hackers behind it will demand payment in BitCoin. While it may be difficult to fix your PC after cizer Virus hits it, you should still not pay the price for the decryption key.
| Threat Name | cizer Virus |
| Category | Ransomware/Cryptovirus. |
| Main Activity | Infects the computer after which encrypts important documents and holds them hostage until a ransom is paid. |
| Signs of Presence | Files are encrypted with a custom file extension and users are extorted to pay ransom to get the data to work again.. |
| Spread | Via malicious e-mail spam and set of infection tools. |
| Detection+Removal | DOWNLOAD REMOVAL TOOL FOR cizer Virus |
| File Recovery | Download Data Recovery Software, to see how many files encrypted by cizer Virus ransomware you will be able to recover. |
How Can cizer Virus Arrive on Your PC?
There are various ways for cizer Virus to get access to your system. Some user may download it completely willingly after searching for a way to solfe a problem online for free. You should always remember that there is not an ‘easy’ way to get rich. If some website offers you free money, free accounts or some suspiciously high discounts, then it is probably a scam. The purpose will be either to steal sensitive information from you or to deploy malware to your system. In this case, it is the latter.
If you have never searched for a free program, crack or patch, but your device is still encrypted by this ransomware, then it might have come as an email attachment or a corrupt link in a message. In this case, the hackers might have described it in a very different way. The payload of the cyber threat could have been disguised as an MS Word document or some .pdf file. The culprits behind cizer Virus may use social engineering tactics to trick the user into opening the attachment. The most common tactic is the mentioning of some shocking information such as unauthorized bank transactions or failed shipments.
What May Follow the Installation of cizer Virus?
Although cizer Virus will run various commands at the same time, you may not notice in time that you are infected. The cizer Virus ransomware tries to keep its processes in the background until the whole encryption operation has been completed. Once it happens, you will notice a lockdown message on your desktop. According to the developers of this ransomware, you have a several hours to pay a price for the decryption key, which may be the only way to get access to your file once again. The requested sum is usually paid in BitCoin. This cizer Virus Trojan sets it’s own suffix as the default extension of all of the affected files. As a result, you may notice it whenever you browse your pictures, documents, music or other files. Whenever you try to view or modify them, you may notice an error message such as ‘Windows cannot open this file format’.
How to Remove cizer Virus Ransomware?
The most important advice you can receive is not to pay the ransom. You should not finance cyber criminals because their motivation to create ransomware will only grow if their attacks are successful. Moreover, you can never trust hackers. They may not hold their end of the deal, which means you may lose your money in addition to your files. The suggested course of action is to eliminate all traces of cizer Virus, after which you can attempt alternative methods to decrypt your data. The most reliable tactic to delete this advanced ransomware is to use dedicated malware removal solutin, which can clean sensitive areas like the Windows Registries without the risk of ruining the whole operating system. After the successful removal of cizer Virus, you can attempt to use a free decryptor or the system restore feature.
Preparation before removal of cizer Virus:
1.Make sure to backup your files.
2.Make sure to have this instructions page always open so that you can follow the steps.
3.Be patient as the removal may take some time.
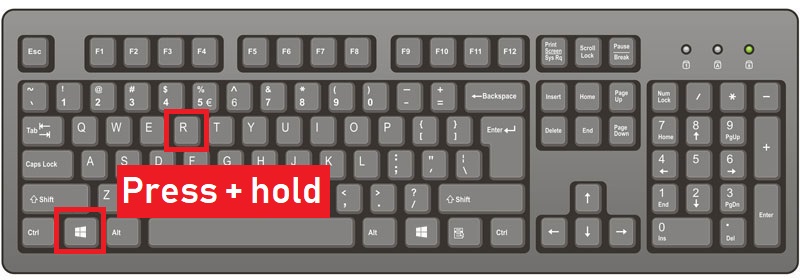
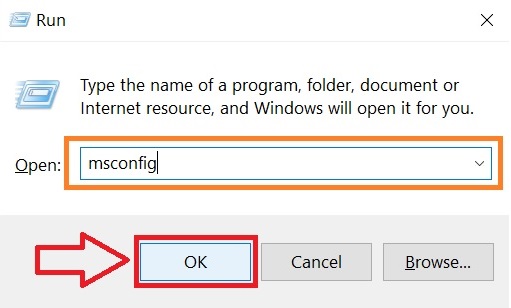
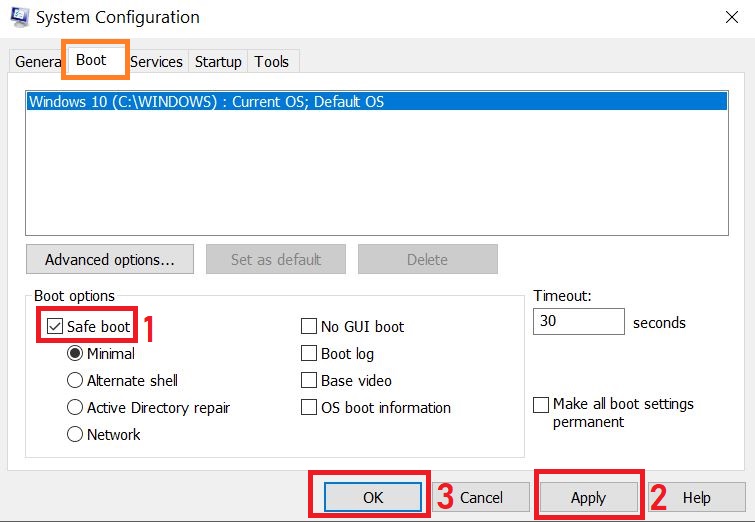
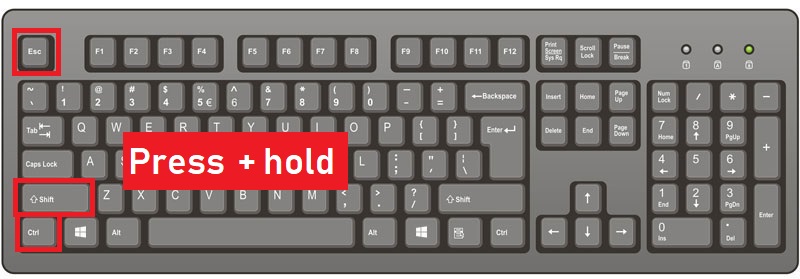
Step 1: Reboot your computer in Safe Mode:
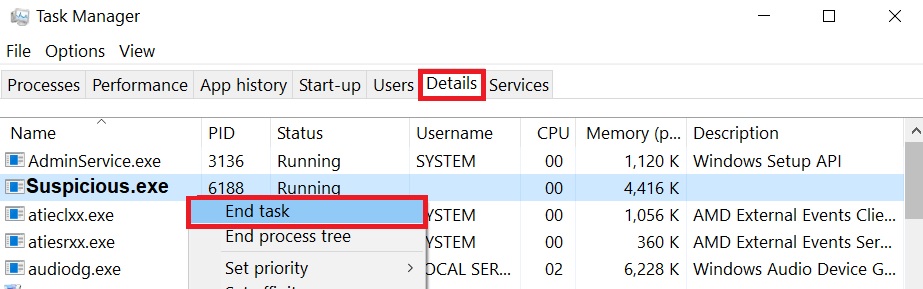
Step 2: Cut out cizer Virus in Task Manager
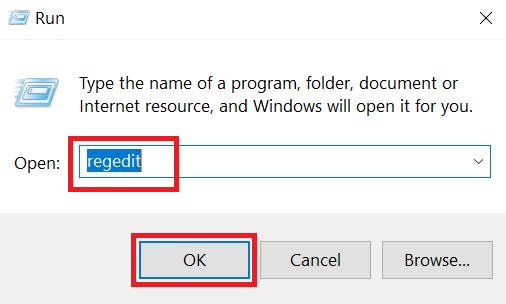
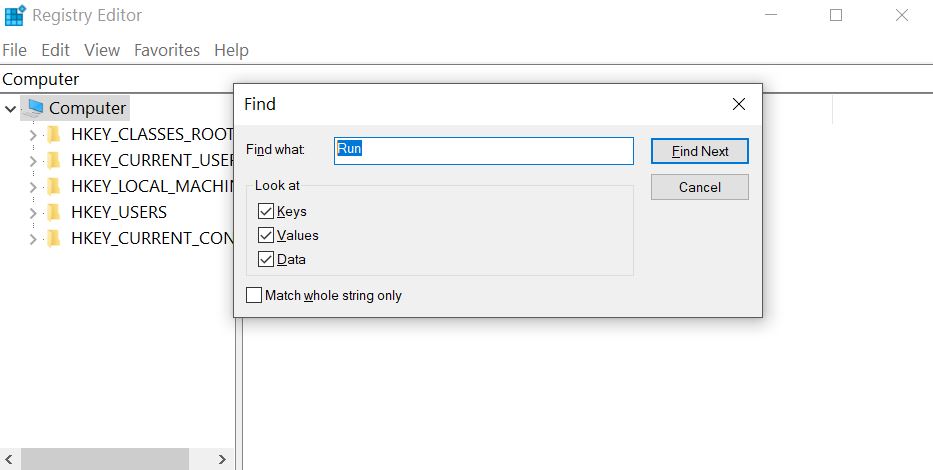
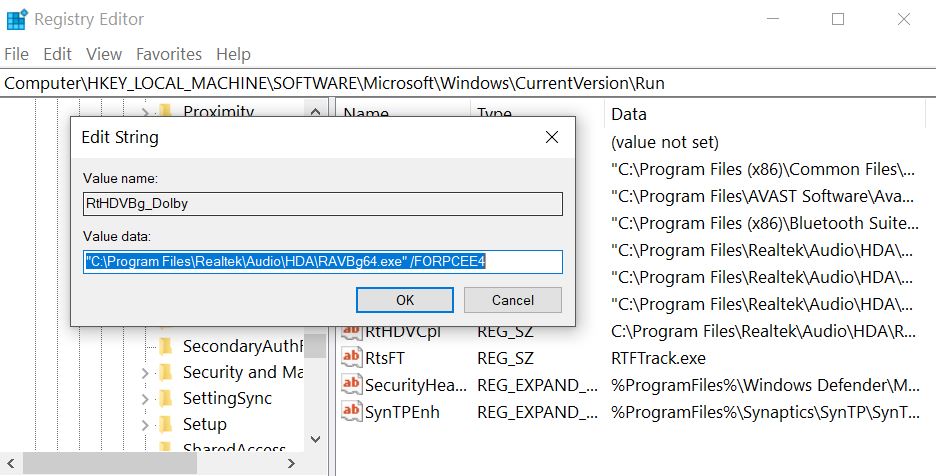
Step 3: Eliminate cizer Virus‘s Malicious Registries.
For most Windows variants:
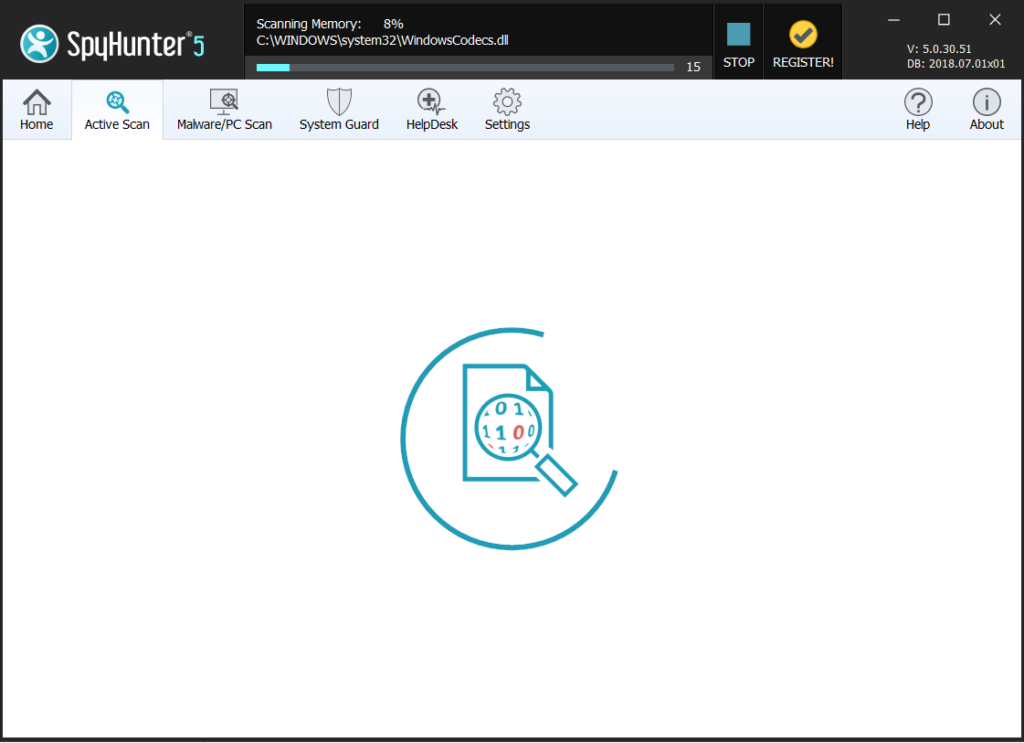
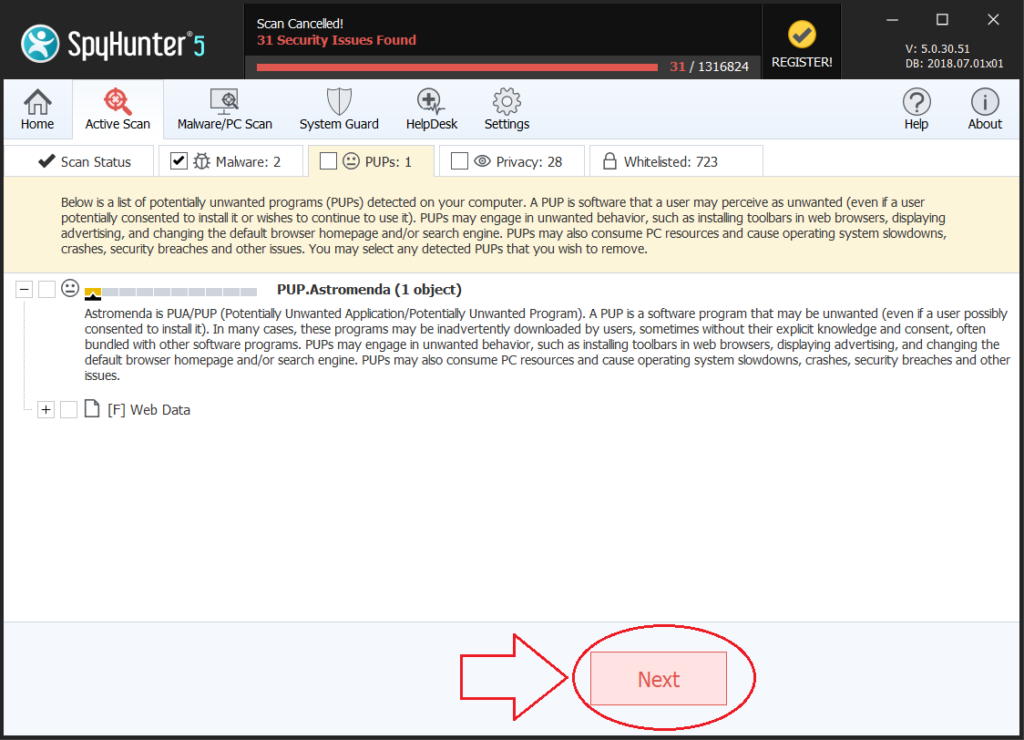
Step 4: Scan for and remove all virus files, related to cizer Virus and secure your system.
If you are in Safe Mode, boot back into normal mode and follow the steps below
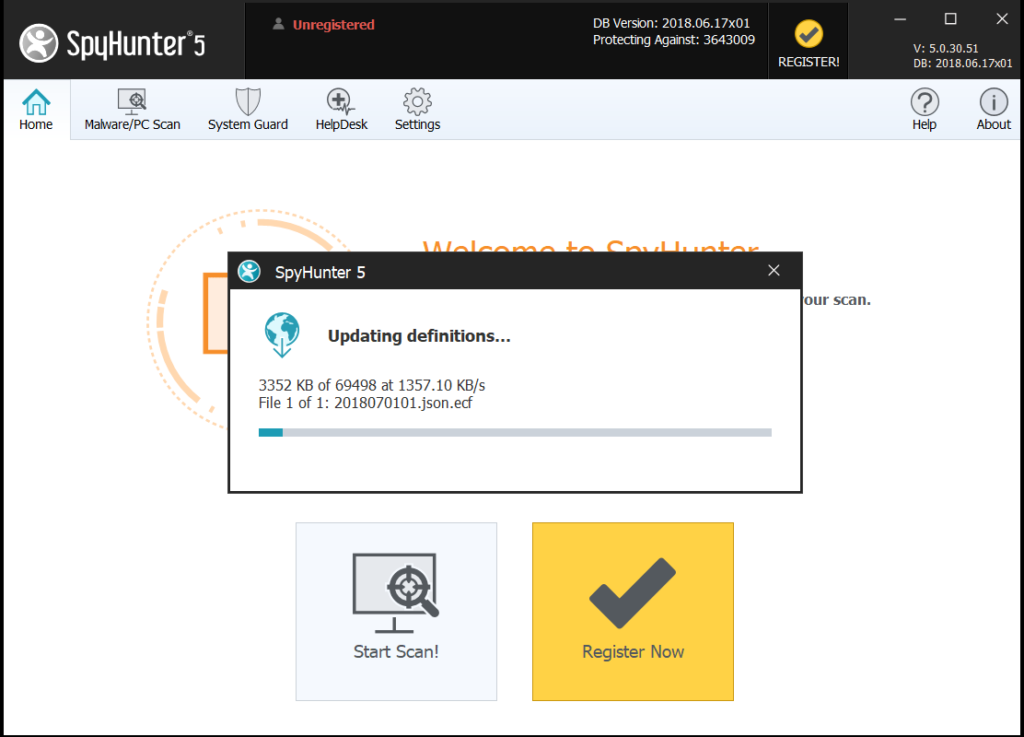
It is advisable to run a free scan before committing to the full version. You should make sure that the malware is detected by SpyHunter first.
Step 5:Recover files encrypted by the cizer Virus Ransomware.
Method 1: Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Most of the currently available decryptors for ransomware viruses can be seen if you visit the NoMoreRansom project – a project that is the result of combined efforts of researchers worldwide to create decryption software for all ransomware viruses. Simply go there by clicking on the following LINK and find your ransomware version decrypter and try it, but always remember to do a BACKUP first.
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files: