A blog post, made to show you how to remove the Explorer ransomware virus completely from your computer system and demonstrate how to try and recover .explorer files encrypted by this infection without paying the ransom.
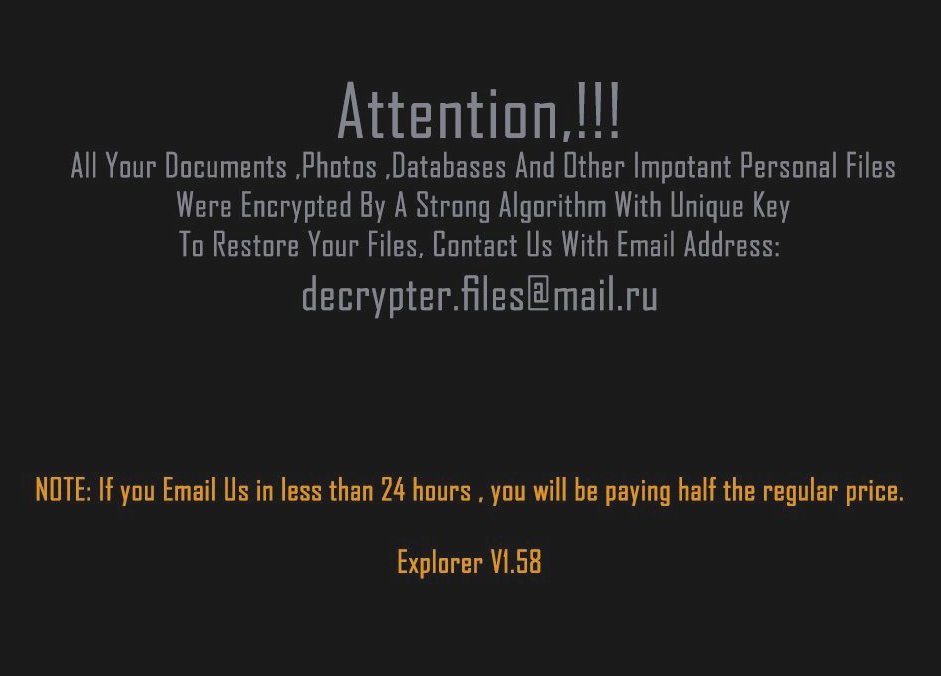
New ransomware infection, known as Explorer ransomware, has surfaced on our cyber-security radar. The virus aims to encrypt the files on the computers infected by it via what is known as AES encryption mode. The ransomware than adds .explorer file extension to the encrypted files and demands victims to contact the e-mail address [email protected]. The virus aims for one thing and one thing only – to get you to pay a hefty ransom fee in order to get the files restored back to normal again.
| Threat Name | .explorer |
| Category | Ransomware virus. |
| Main Activity | Infects the computer after which encrypts important documents and holds them hostage until a ransom is paid. |
| Signs of Presence | Files are encrypted with the .explorer file extension. |
| Spread | Via malicious e-mail spam and set of infection tools. |
| Detection+Removal | DOWNLOAD REMOVAL TOOL FOR .explorer |
| File Recovery | Download Data Recovery Software, to see how many files encrypted by .explorer ransomware you will be able to recover. |
.explorer Ransomware – What Does It Do?
As soon as an infection with this ransomware is already inevitable, the virus may immediately situate it’s payload on the computer of the victim. The payload may be located in several different folders, including:
- %AppData%
- %Local%
- %LocalLow%
- %Roaming%
- %Windows%
The virus drops it’s payload in several .DLL and other types of files with the .explorer file extension. Then, the .explorer threat begins to modify the Windows Registry Editor:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
Strings with data may be created under random names with the location of the virus files.
The .explorer ransomware infection is also reported by experts to delete the shadow volume copies and system recovery on Windows machines:
→ process call create “cmd.exe /c
vssadmin.exe delete shadows /all /quiet
bcdedit.exe /set {default} recoveryenabled no
bcdedit.exe /set {default} bootstatuspolicy ignoreallfailures
Other activity of the .explorer threat may be to stop MySQL and other Windows Processes. But this happens only after it has gained Administrative access.
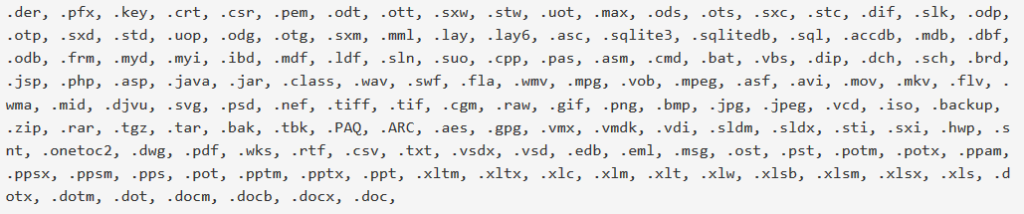
The .explorer virus may also uses a sophisticated algorithm to encrypt the files on the compromised computer. The ransomware infection scans for the following files in order to encrypt them:
After the files are encrypted, the .explorer adds the following extension:
- .explorer
.explorer – How Does It Infect?
The infection process of this virus begins with it’s method of spreading. So far, this may be via:
- E-mail spam messsages.
- Fake setups uploaded online.
- Via botnets that target organizations.
Remove .explorer File Virus and Recover Your Files
In order to remove this ransomware infection, you can follow the tutorial below. Be advised that the best removal method according to security researchers is to download an advanced anti-malware product that will help you remove this ransomware infection completely and protect your computer in the future as well.
Whatever the case may be, experts strongly advise against paying the ransom and removing the virus yourself as well as trying to restore the files using other methods, like the ones in the instructions below.
Booting in Safe Mode
For Windows:
1) Hold Windows Key and R
2) A run Window will appear, in it type “msconfig” and hit Enter
3) After the Window appears go to the Boot tab and select Safe Boot
Cut out .explorer in Task Manager
1) Press CTRL+ESC+SHIFT at the same time.
2) Locate the “Processes” tab.
3) Locate the malicious process of .explorer, and end it’s task by right-clicking on it and clicking on “End Process”
Eliminate .explorer‘s Malicious Registries
For most Windows variants:
1) Hold Windows Button and R.
2) In the “Run” box type “Regedit” and hit “Enter”.
3) Hold CTRL+F keys and type .explorer or the file name of the malicious executable of the virus which is usually located in %AppData%, %Temp%, %Local%, %Roaming% or %SystemDrive%.
4) After having located malicious registry objects, some of which are usually in the Run and RunOnce subkeys delete them ermanently and restart your computer. Here is how to find and delete keys for different versions.
For Windows 7: Open the Start Menu and in the search type and type regedit –> Open it. –> Hold CTRL + F buttons –> Type .explorer Virus in the search field.
Win 8/10 users: Start Button –> Choose Run –> type regedit –> Hit Enter -> Press CTRL + F buttons. Type .explorer in the search field.
Automatic Removal of .explorer
Recover files encrypted by the .explorer Ransomware.
Method 1: Using Shadow Explorer. In case you have enabled File history on your Windows Machine one thing you can do is to use Shadow Explorer to get your files back. Unfortunately some ransomware viruses may delete those shadow volume copies with an administrative command to prevent you from doing just that.
Method 2: If you try to decrypt your files using third-party decryption tools. There are many antivirus providers who have decrypted multiple ransomware viruses the last couple of years and posted decryptors for them. Chances are if your ransomware virus uses the same encryption code used by a decryptable virus, you may get the files back. However, this is also not a guarantee, so you might want to try this method with copies of the original encrypted files, because if a third-party program tampers with their encrypted structure, they may be damaged permanently. Here are the vendors to look for:
- Kaspersky.
- Emsisoft.
- TrendMicro.
Method 3: Using Data Recovery tools. This method is suggested by multiple experts in the field. It can be used to scan your hard drive’s sectors and hence scramble the encrypted files anew as if they were deleted. Most ransomware viruses usually delete a file and create an encrypted copy to prevent such programs for restoring the files, but not all are this sophisticated. So you may have a chance of restoring some of your files with this method. Here are several data recovery programs which you can try and restore at least some of your files: