Dieser Artikel wurde helfen erstellt zu erklären, was die sind .PUMA Dateien, gehört, Ransomware Virus zu stoppen und wie die Virusvariante zu entfernen und wie Sie Dateien wiederherstellen, mit der .PUMA Dateierweiterung.
Eine neue Version von .PUMA Ransomware wurde in der Wildnis entdeckt. Das Virus zielt darauf ab, die Dateien zu verschlüsseln, sie unbrauchbar machen, bis das Opfer Geld in Form von cryptocurrencies zu den Cyber-Kriminellen bezahlt und sie entschlüsseln Sie die Dateien, um sie wieder nutzbar. Die schlechte Nachricht ist, dass .PUMA Ransomware ist ein Virus, das ganze Systeme Krüppel, so dass es ist die Entfernung ein wenig komplizierter. Wenn Ihr Computer durch die .PUMA Dateien Virus infiziert, Wir empfehlen dringend, dass Sie diesen Artikel lesen, da es enthält weitere Informationen und Anleitungen zum Entfernen und Dateiwiederherstellung von Dateien, durch diese Infektion verschlüsselt.
Note!Falls Sie hatten Ihre Mac infiziert von .PUMA Ransomware, Sie sollten folgen Sie den Anweisungen auf wie zu erkennen und Malware für Mac-Computer entfernen so dass Sie alle Mac Bedrohungen effektiv angehen können, und entfernen Sie sie richtig.
| Name der Bedrohung | .PUMA Ransomware |
| Kategorie | Ransomware / Cryptovirus |
| Hauptaktivität | Eine Variante der STOP-Ransomware, verschlüsselt Dateien und erpresst den Benutzer Lösegeld für sie zu bezahlen. |
| Signs of Presence | Die Dateien werden die .PUMA Dateierweiterung und die Dateityp Änderungen an PUMA angehängt. Ein Erpresserbrief, namens !readme.txt auf dem Opfer-PC fallen gelassen. |
| Verbreitung | Via bösartigem E-Mail-Spam und eine Reihe von Infektions Tool. |
| Erkennung + Entfernen | DOWNLOAD Entriegelungswerkzeug für .PUMA Ransomware
Note!Für Mac-Anwender, Bitte Verwenden Sie die folgenden Anweisungen. |
| Wiederherstellung von Dateien | Laden Sie Data Recovery Software, um zu sehen, wie viele von .PUMA Ransomware Ransomware verschlüsselten Dateien können Sie sich erholen. |
Welche Dateien betroffen erhalten Kann durch .PUMA Ransomware Ransomware?
.PUMA Ransomware Ransomware dient als typische Datei-kodierenden Trojan. Sobald es den Zugriff auf Ihre Maschine bekommt, diese cryptomalware einen schnellen Scan führen die Wege, um alle Ihre persönlichen Dateien zu finden. Die gezielten Daten umfassen alle MS Office-Dokumente, Ihre wertvollen Fotos und Videos, Ihre Datenbanken, die Programmdateien, etc. Nur wenige Dateien wie die, die auf die Kernprozesse von Windows im Zusammenhang geschont werden können. Sobald die Operation endet, Sie werden eine bedrohliche Lockdown Nachricht auf Ihrem Desktop und die Standard-Dateierweiterung wird sich feststellen ‚DLL‘. Die Cyber-Kriminellen geben die Opfer nur einige Tage, um das Lösegeld von Bitcoins zahlen, sonst drohen sie für immer den Entschlüsselungsschlüssel löschen. Der Zweck dieser erschreckenden Nachricht ist, die Person zu schocken und ihn irrational machen handeln. Die Opfer fühlen sich oft als die einzige Lösung für das Problem ist, das Geld zu zahlen. In Wirklichkeit, alle Spezialisten empfehlen einstimmig, die Anweisungen des Hacker aus verschiedenen Gründen zu folgen.So schützen Sie sich vor .PUMA Ransomware Ransomware?
Diese Ransomware verursachen enorme und oft irreversiblen Schädigung der betroffenen Maschinen. Zum Glück, Sie können die Infektion verhindern, solange Sie bei Ihrer Online-Sitzungen sind wachsam. Dieser Trojaner ist nicht bekannt, einige einzigartige Methoden zu verwenden, um die Abwehrkräfte Ihres Computers zu infiltrieren. Die wahrscheinlichste Ursache für .PUMA Ransomware Ransomware gibt über Spam-E-Mails. Sie können eine Nachricht mit einem schockierenden Inhalt erhalten, ermutigen Sie auf einem schädlichen Link zu klicken Sie entweder oder eine geschwächte-Datei herunterladen. Die Hacker haben ein ganzes Arsenal von Tools, die Sie zu manipulieren, dass sie so tun. Beispielsweise, sie können behaupten, eine internationale Bank oder einige beliebte Reederei zu vertreten. Wenn sie sprechen Sie ohne Ihren Namen zu nennen, die E-Mail ist wahrscheinlich ein Betrug, und Sie sollten es ignorieren. Leider, wenn Sie einfach klicken oder die infizierte Datei herunterladen, Ihre Aktion wird höchstwahrscheinlich genug sein, um die schädlichen Codes von .PUMA Ransomware Ransomware aktivieren. In diesem Fall, nur eine glaubwürdige Sicherheitslösung kann in der Lage sein, den bevorstehenden Schaden zu verhindern,.
Wie man .PUMA Ransomware Ransomware löschen und Ihre Dateien kostenlos Entschlüsselt?
Die Hauptgründe dafür nicht das Lösegeld zu zahlen sind zwei. Erste, Sie können nicht die versprochene Entsperrschlüssel auch nach genau das tun, wie die Hacker Nachfrage erhalten. Sie Betrug häufig Opfer, weil die Bitcoin-Plattform erlaubt es nicht, Erstattungen und die Menschen haben keine Möglichkeit, ihr Geld zurück zu bekommen. Der zweite Grund nicht Cyber-Kriminellen zu finanzieren ist, dass Ihr Geld wird sie motivieren, nur aggressive Ransomware wie .PUMA Ransomware zu schaffen. Andererseits, wenn ihre Angriffe sind vergeblich, sie können mit einem solchen bösartigen Trojaner Spam im Internet stoppen. Diese Parasiten erfordern ganz einige Anstrengungen professionell erstellt werden und verbreiten effizient.
Wenn Sie sich entscheiden, nicht das Lösegeld zu zahlen, gibt es mehrere andere Möglichkeiten, die Sie entschlüsseln Ihre persönlichen Dateien können helfen. Sie sollen die Versuche, indem alle Spuren des Malware beginnen. Wenn Sie nicht .PUMA Ransomware Ransomware ordnungsgemäß löschen, es kann Ihre Dateien wieder in der Zukunft oder sich auf andere angeschlossene Geräte entschlüsseln. Die manuelle Entfernung ist nicht die empfohlene Lösung, da es auf Expertenebene Wissen in Computern erfordert. Die zuverlässigste Taktik ist dedizierte Sicherheits-Software zu verwenden, die F.PUMA Ransomware Ransomware zu seiner Datenbank hinzugefügt. Sobald die Scan beendet, Sie sollten einige der Programme für die Wiederherstellung von Dateien versuchen oder die integrierte Systemwiederherstellung. Wenn Sie Glück genug, um eine Ersatzkopie der Dateien auf einem externen Gerät zu haben,, Sie können sie importieren sicher auf den Computer zurück.
Booting im abgesicherten Modus
Für Windows:
1) Halt Windows-Taste und R
2) Ein Run Fenster erscheint, darin Typ “msconfig” und traf Eingeben
3) Nachdem das Fenster erscheint auf der Registerkarte Start gehen und Safe Boot wählen
Schneiden Sie .PUMA Ransomware im Task-Manager
1) Drücken Sie STRG + ESC + SHIFT gleichzeitig.
2) Suchen Sie den “Prozesse” Tab.
3) Suchen Sie den bösartigen Prozess der .PUMA Ransomware, und es ist Aufgabe durch einen Rechtsklick auf das enden und klicken auf “End-Prozess”
Beseitigen Sie .PUMA Ransomware Malicious Register
Für die meisten Windows-Varianten:
1) Halt Windows-Taste und R.
2) In dem “Lauf” Box-Typ “regedit” und traf “Eingeben”.
3) Halt STRG + F Tasten gedrückt und gibt .PUMA Ransomware oder den Dateinamen des schädlichen ausführbaren des Virus, die in der Regel in% AppData% liegen, %Temp%, %Lokal%, %Roaming% oder% Systemdrive%.
4) Nachdem böswillige Registrierung Objekte befinden, einige davon sind in der Regel in den Run und RunOnce Subkeys löschen ermanently und starten Sie Ihren Computer. Hier ist, wie zu finden und löschen Schlüssel für verschiedene Versionen.
Für Windows 7: Öffnen Sie das Startmenü und in den Suchtyp und geben Sie regedit -> Öffnen Sie es. -> Halten Sie CTRL + F-Tasten -> Typ .PUMA Ransomware Virus in das Suchfeld ein.
Sieg 8/10 Benutzer: Start Button -> Wählen Sie Ausführen -> regedit -> drücken Sie die Eingabetaste -> Drücken Sie Strg + F-Tasten. Geben Sie .PUMA Ransomware im Suchfeld.
Automatische Entfernung von .PUMA Ransomware
Schritt 1:Klicken Sie auf die Schaltfläche SpyHunter Installer herunterladen.
Es ist ratsam, einen Scan, bevor ich zum Kauf der Vollversion laufen. Sie sollten sicherstellen, dass die Malware von SpyHunter erkannt wird zuerst.
Schritt 2: Führen Sie sich selbst von den Download-Anweisungen für jeden Browser bereitgestellt.
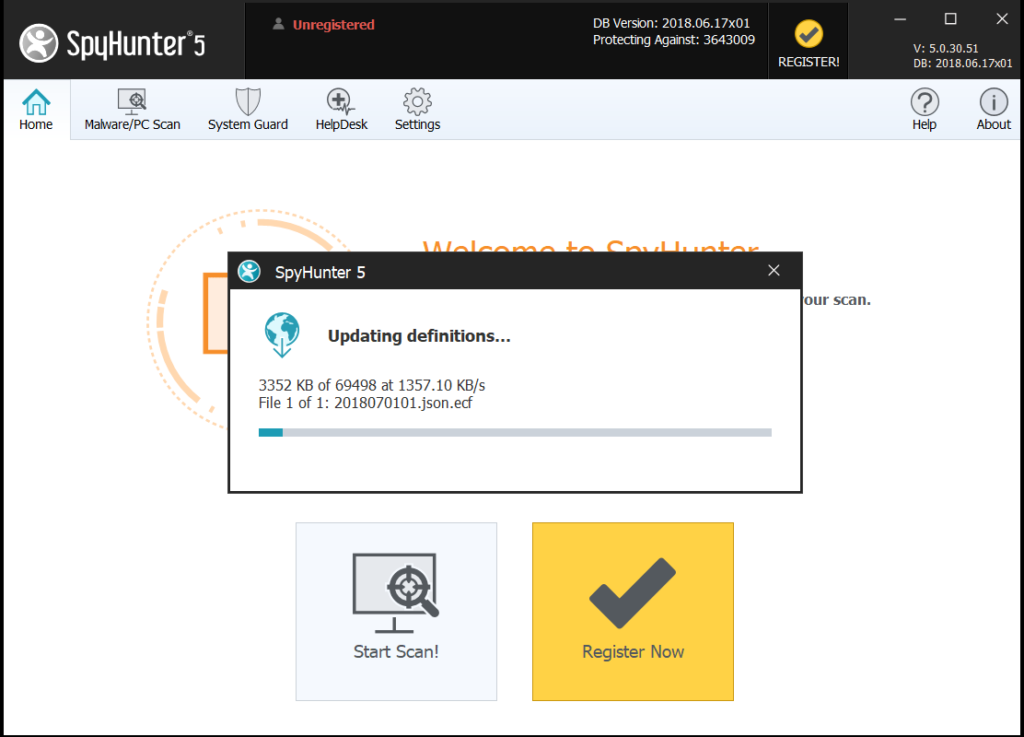
Schritt 3: Nachdem Sie SpyHunter installiert, warten, bis das Programm aktualisieren.
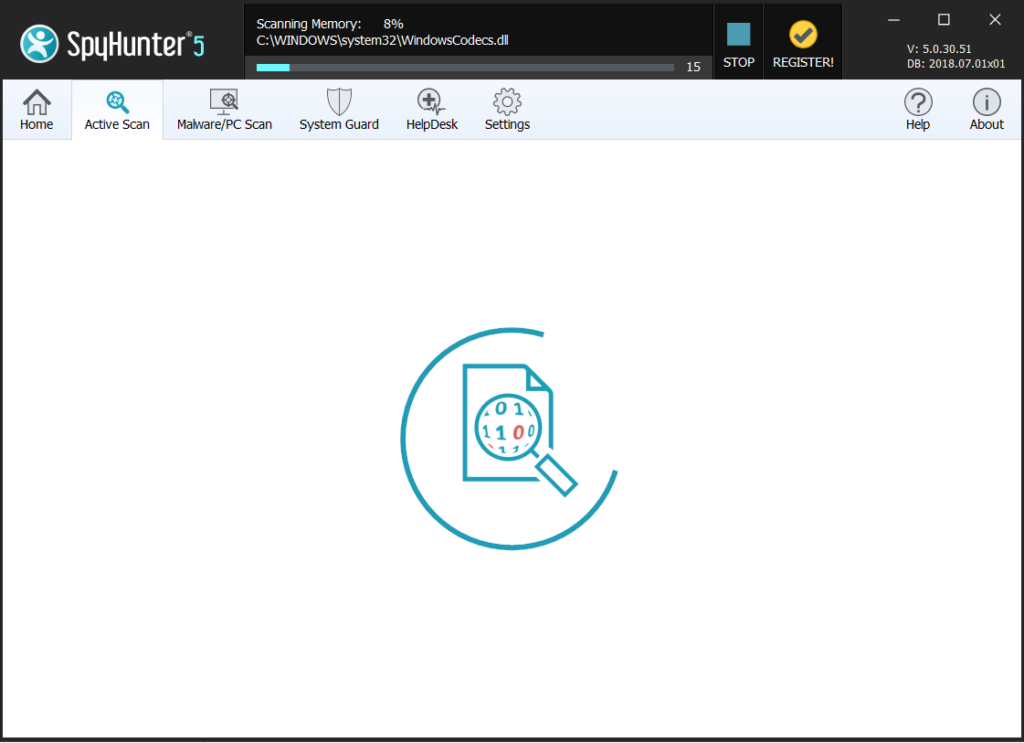
Schritt 4: Wenn das Programm nicht automatisch starten scannen, klicken Sie auf die “Scan Computer jetzt” Taste.
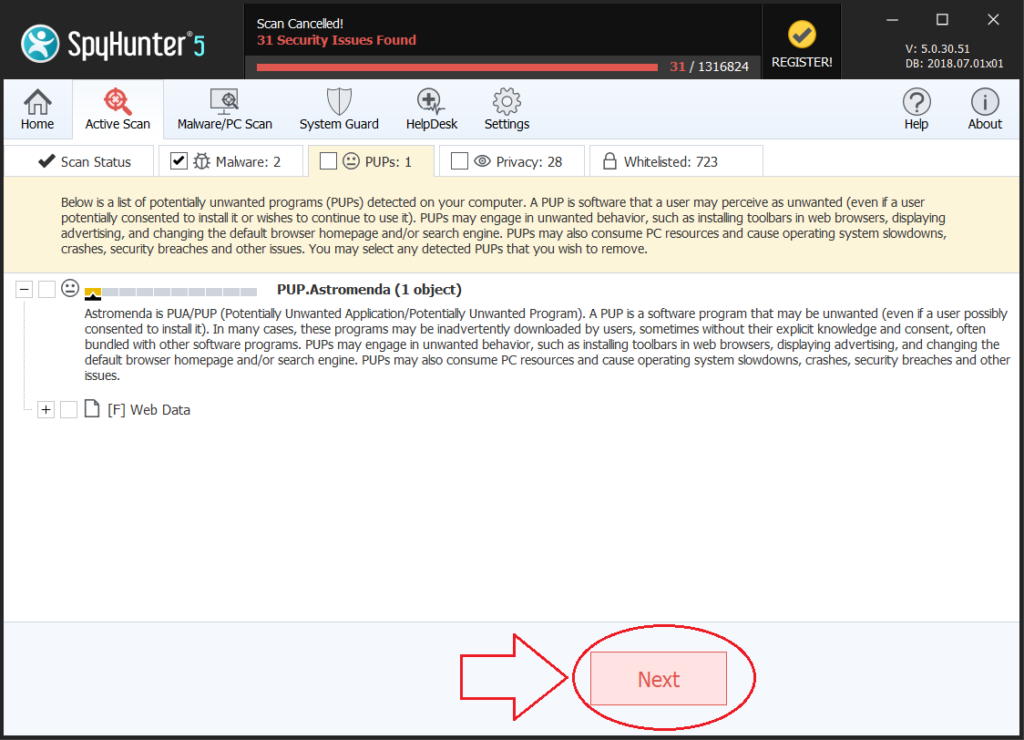
Schritt 5: Nach SpyHunter abgeschlossen mit Ihrem System `scannen, klicken Sie auf die “Als Nächstes” Taste, um es zu löschen.
Step6: Sobald Ihr Computer ist sauber, ist es ratsam, es neu zu starten.
Wiederherstellen von Dateien verschlüsselt durch die .PUMA Ransomware Ransomware.
Methode 1: Mit Schatten Explorer. Falls Sie Dateiversionen auf Ihrem Windows-Rechner eine Sache aktiviert Sie tun können, ist Schatten Explorer zu verwenden, um Ihre Dateien zurück. Leider von einigen Ransomware Viren können diese Schattenvolumen Kopien mit einem administrativen Befehl löschen Sie verhindern, dass nur tun, dass.
Methode 2: Wenn Sie versuchen, Ihre Dateien mit Drittanbieter-Entschlüsselungs-Tool zum Entschlüsseln. Es gibt viele Anti-Virus-Anbieter, die in den letzten paar Jahren entschlüsselt haben mehrere Erpresser-Viren und veröffentlicht Decryptoren für sie. Die Chancen stehen gut, wenn Ihr Erpresser-Virus den gleichen Verschlüsselungscode verwendet ein entschlüsselbar Virus verwendet, Sie können die Dateien wieder. Jedoch, dies ist auch keine Garantie, so sollten Sie diese Methode mit Kopien der ursprünglichen verschlüsselten Dateien versuchen,, denn wenn ein Fremdanbieter-Programm Stampfer mit ihrer verschlüsselten Struktur, sie können dauerhaft beschädigt werden. Hier sind die Anbieter zu suchen,:
- Kaspersky.
- Emsisoft.
- Trend Micro.
Methode 3: Mit Data Recovery Tools. Diese Methode wird von mehreren Experten auf dem Gebiet vorgeschlagen. Es kann Ihre Festplatte Sektor zu scannen und damit die verschlüsselten Dateien verschlüsselt erneut verwendet werden, als ob sie gelöscht wurden. Die meisten Ransomware Viren in der Regel eine Datei löschen und eine verschlüsselte Kopie erstellen, um solche Programme zu verhindern, dass die Dateien für die Wiederherstellung, aber nicht alle sind diese anspruchsvolle. So können Sie eine Chance haben, einige Ihrer Dateien mit dieser Methode der Wiederherstellung. Hier sind mehrere Daten-Recovery-Programme, die Sie versuchen können, und zumindest einige Ihrer Dateien wiederherstellen: